Zero Trust Explained The Cybersecurity Model Stopping Hackers Cold

Zero Trust Cyber Security Model Pdf Security Computer Security What is zero trust and why is it considered the future of cybersecurity? in this video, we explain the zero trust security model in simple, beginner friendly terms. Zero trust differs from conventional security models that take users within the network as secured, instead adopting a strict policy of "never trust, always verify".

Embracing A Zero Trust Security Model Pdf Computer Security Security This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security. Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.

Zero Trust Security Models Overview Pdf Learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. The zero trust security model redefines protection for our connected world. it ditches old trust for endless checks, fitting cloud shifts, remote setups, and clever hackers. Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.
Zero Trust Security Model Explained Principles Architectu Blog The zero trust security model redefines protection for our connected world. it ditches old trust for endless checks, fitting cloud shifts, remote setups, and clever hackers. Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.
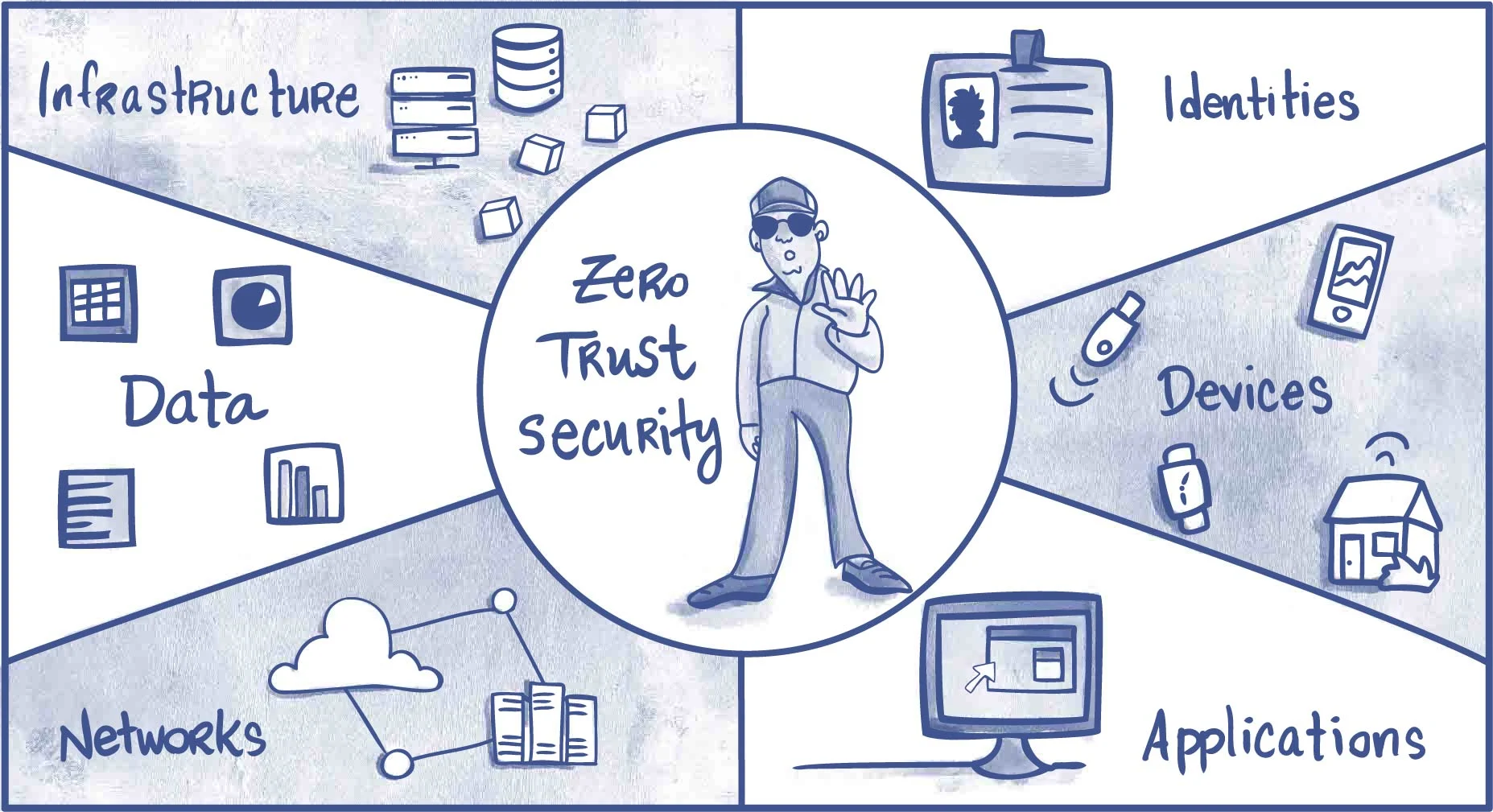
Zero Trust Explained How To Implement Zero Trust Architecture Reduce Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.
Comments are closed.