Zero Trust Explained Real World Example

Zero Trust Explained Real World Example Shakeel F In this article, i’m pulling back the curtain on real zero trust security examples i’ve encountered, analyzed, and built myself. you’ll see concrete implementations from enterprise environments, cloud infrastructures, and iot deployments. In this article, we’ll explore real world examples of organizations that have successfully implemented zero trust principles, showcasing their strategies and outcomes.
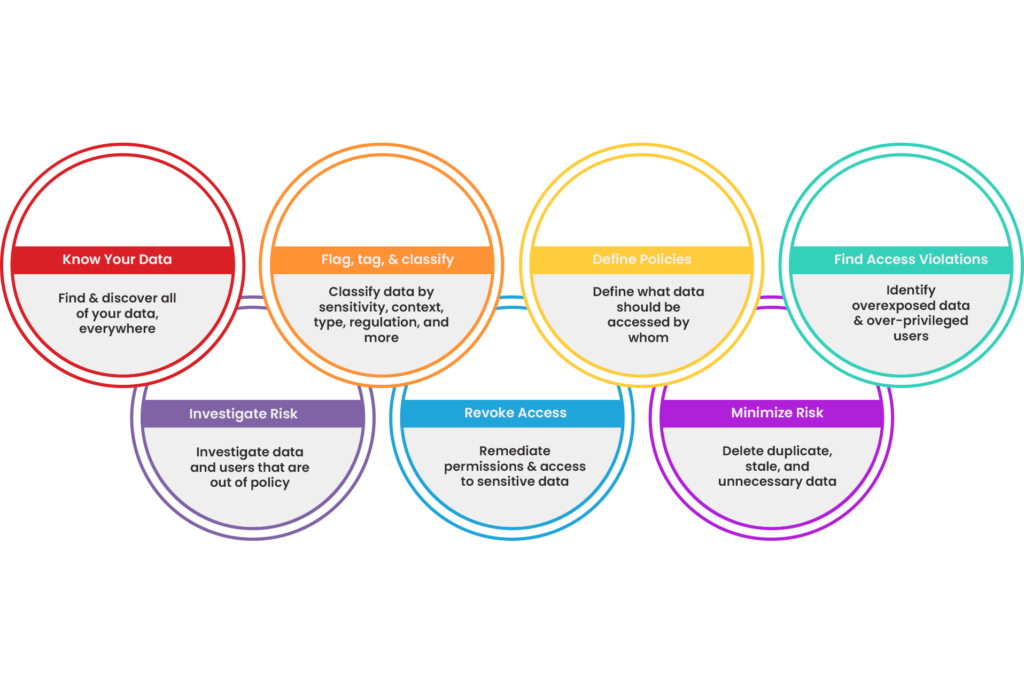
Enable Zero Trust Bigid In this article, we have presented a zero trust architecture example to illustrate how a fully secured organization operates and included 12 additional zero trust examples highlighting the features and tools required for 360 degree zero trust protection. Let’s break down how zero trust can work in a real world scenario. imagine a company with employees spread out across different cities, all working remotely. Zero trust is a broader security model than endpoint security. zero trust checks identity, device status, and user behavior before it allows access to apps or data. Zero trust strategy: real world implementation zero trust is not a product you buy — it’s a strategy you architect. this hub provides the most operationally practical zero trust guidance available, drawn from real deployments across government and enterprise in 40 countries.

Zero Trust Explained Zero trust is a broader security model than endpoint security. zero trust checks identity, device status, and user behavior before it allows access to apps or data. Zero trust strategy: real world implementation zero trust is not a product you buy — it’s a strategy you architect. this hub provides the most operationally practical zero trust guidance available, drawn from real deployments across government and enterprise in 40 countries. This article delves deep into the principles, implementation strategies, and real world case studies of zero trust security, offering actionable insights for professionals seeking to fortify their organizations against modern threats. But if you're like most of us, you might be wondering: what does zero trust actually look like when you move beyond the marketing buzzwords and start implementing it in the real world?. Real zero trust architecture demands integration across identity, access, endpoints, network, and data. let’s explore what zero trust really looks like in action – and what separates effective deployments from checkbox ones. Complete guide to zero trust security architecture. learn the principles of "never trust, always verify," how to implement zero trust, and real world architecture patterns for enterprises.
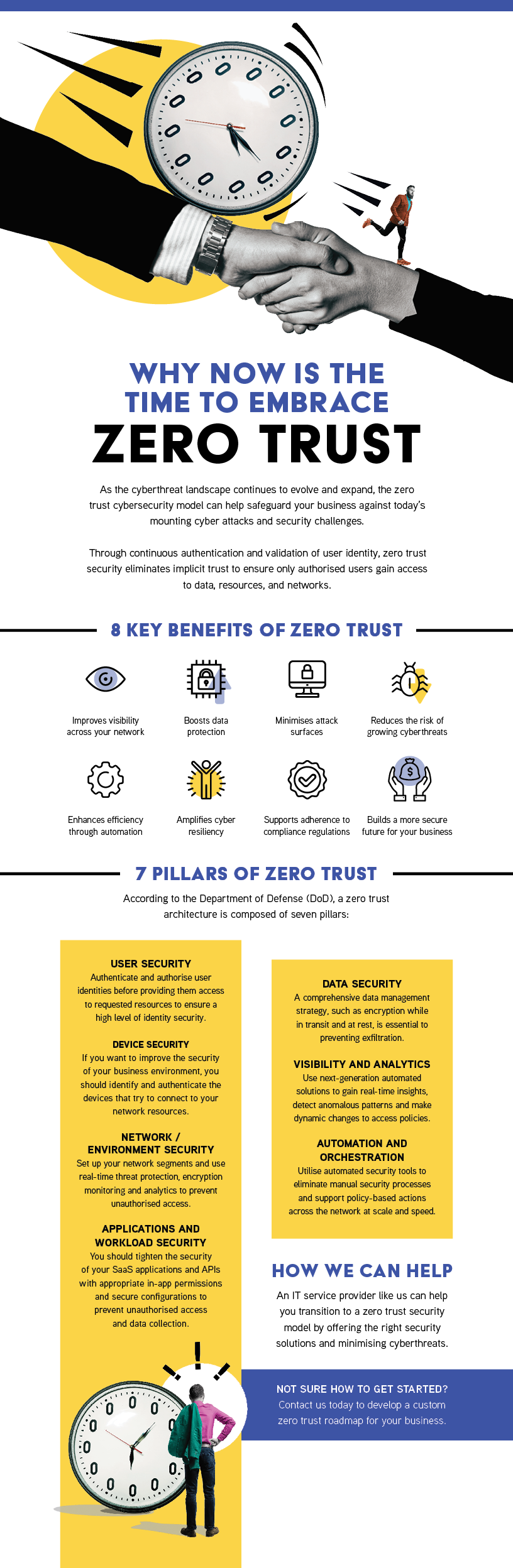
Territory Technology Solutions Zero Trust This article delves deep into the principles, implementation strategies, and real world case studies of zero trust security, offering actionable insights for professionals seeking to fortify their organizations against modern threats. But if you're like most of us, you might be wondering: what does zero trust actually look like when you move beyond the marketing buzzwords and start implementing it in the real world?. Real zero trust architecture demands integration across identity, access, endpoints, network, and data. let’s explore what zero trust really looks like in action – and what separates effective deployments from checkbox ones. Complete guide to zero trust security architecture. learn the principles of "never trust, always verify," how to implement zero trust, and real world architecture patterns for enterprises.
Comments are closed.