Zero Trust Explained Netbase Solutions
Zero Trust Framework For Network Security Algosec Today’s enterprise customers need a better security model that adapts to security threats and provides a secure place to store data with microsoft 365. watch this video to get an overview of zero trust. Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust.

Zero Trust Explained Netbase Solutions Zero trust is a newer model of cybersecurity designed to better address changing security requirements for modern organizations. zero trust frameworks can improve security posture, limit lateral movement throughout the network, and prevent data breaches. A zero trust solution should integrate with your existing security stack (siem, vulnerability management, asset inventory, threat intelligence, and remediation tools) to avoid creating new silos. Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. What is zero trust? zero trust is a modern cybersecurity paradigm that shifts the focus of perimeter defense from broader network based perimeters to individual assets and resources.

Demo Video Context Security And Concepts Of Zero Trust Netskope Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. What is zero trust? zero trust is a modern cybersecurity paradigm that shifts the focus of perimeter defense from broader network based perimeters to individual assets and resources. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. What is a zero trust security? learn what zero trust is, how to implement zero trust security, and the challenges faced in implementing a zero trust security model from opentext. By enforcing least privileged access and evaluating context like identity, behavior, and device posture, zero trust secures users, workloads, iot ot devices, and b2b partners as they connect to applications and data—whether on premises, in the cloud, or at the edge. Zero trust is a modern security strategy that follows the principle of never trust, always verify. it assumes that every identity, device, and application is untrusted by default, regardless of location, rather than assuming internal users and devices are safe.
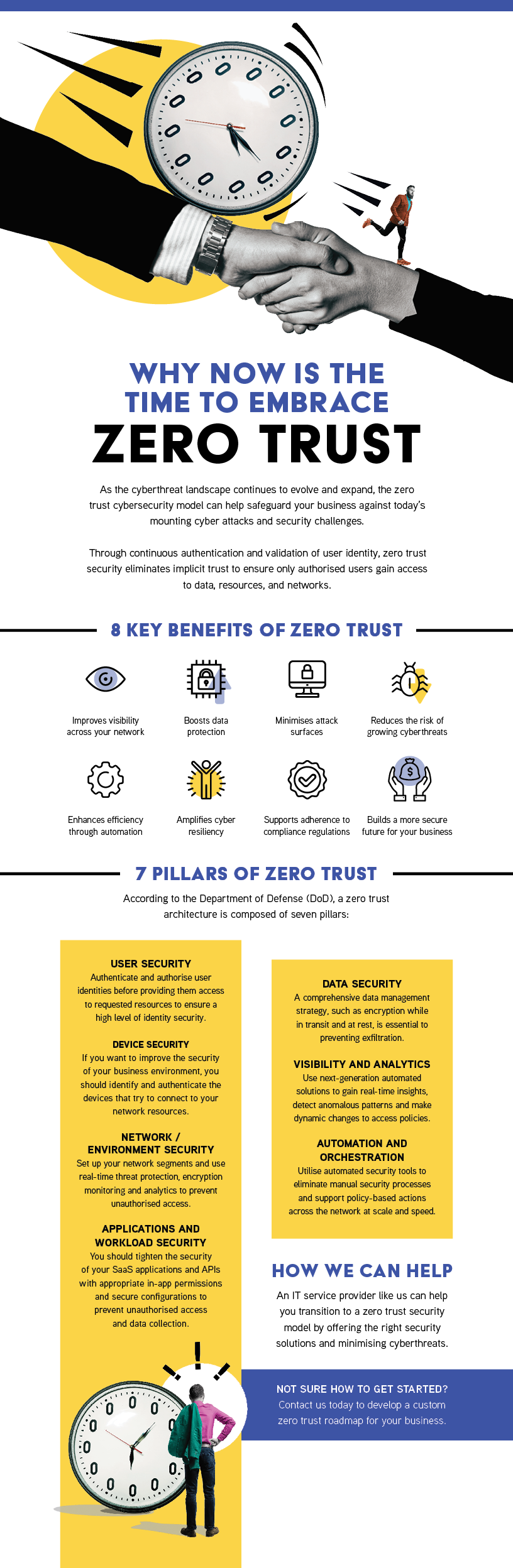
Territory Technology Solutions Zero Trust What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. What is a zero trust security? learn what zero trust is, how to implement zero trust security, and the challenges faced in implementing a zero trust security model from opentext. By enforcing least privileged access and evaluating context like identity, behavior, and device posture, zero trust secures users, workloads, iot ot devices, and b2b partners as they connect to applications and data—whether on premises, in the cloud, or at the edge. Zero trust is a modern security strategy that follows the principle of never trust, always verify. it assumes that every identity, device, and application is untrusted by default, regardless of location, rather than assuming internal users and devices are safe.

Zero Trust Essentials Netbase Solutions By enforcing least privileged access and evaluating context like identity, behavior, and device posture, zero trust secures users, workloads, iot ot devices, and b2b partners as they connect to applications and data—whether on premises, in the cloud, or at the edge. Zero trust is a modern security strategy that follows the principle of never trust, always verify. it assumes that every identity, device, and application is untrusted by default, regardless of location, rather than assuming internal users and devices are safe.
Comments are closed.