Zero Trust Explained In Under 5 Minutes
Enable Zero Trust Bigid That’s where zero trust comes in. in this quick video, jacob breaks down what zero trust means, why it matters, and how it can protect your organization from modern cyberattacks. Want to see zero trust explained in under five minutes? check out our quick video below for a visual breakdown of the concepts we just covered!.

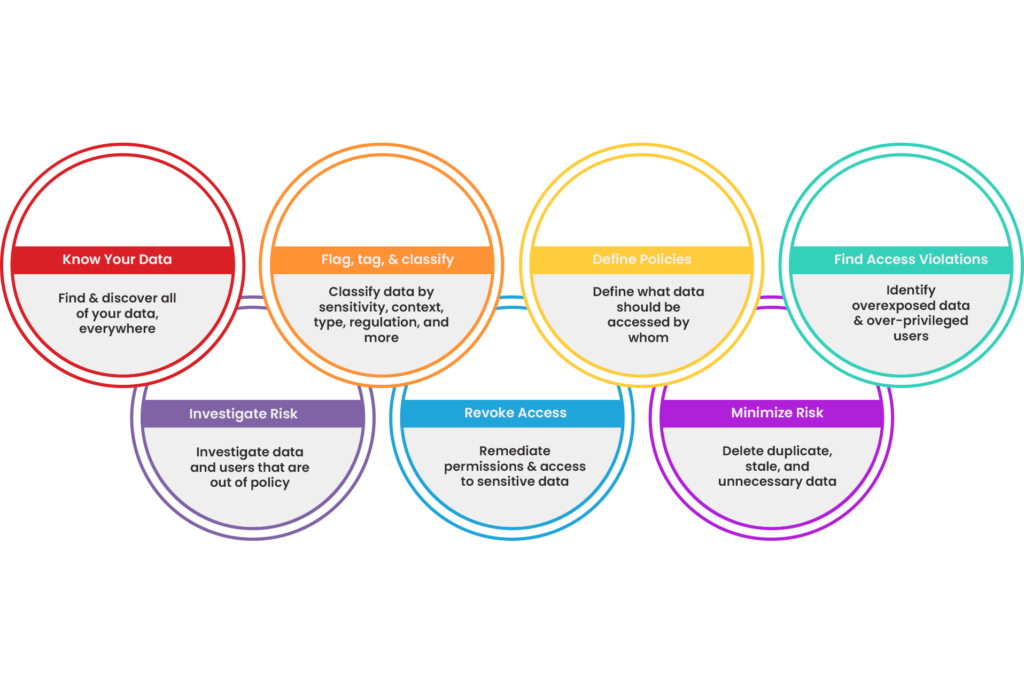
Zero Trust Explained In this post, we break down exactly what zero trust means, why vpn always falls short, and how the zscaler zero trust exchange makes “you can’t attack what you can’t see” a technical reality. What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable. Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. Zero trust is a cybersecurity strategy that removes implicit trust and requires explicit, continuous verification for every access request, across users, devices, applications, workloads, and data, regardless of location.

Zero Trust Security Explained And Applied Xylos Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. Zero trust is a cybersecurity strategy that removes implicit trust and requires explicit, continuous verification for every access request, across users, devices, applications, workloads, and data, regardless of location. Jacob breaks down what zero trust really means and why it’s essential for protecting your business in under 5 minutes. Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Discover what is zero trust security and how to implement it. learn zero trust cyber security, zero trust data security, and practical steps—plus how amplify security accelerates zero trust enforcement. Discover zero trust security explained simply for beginners. learn the zero trust security model, principles, and how it beats traditional security in modern cybersecurity.
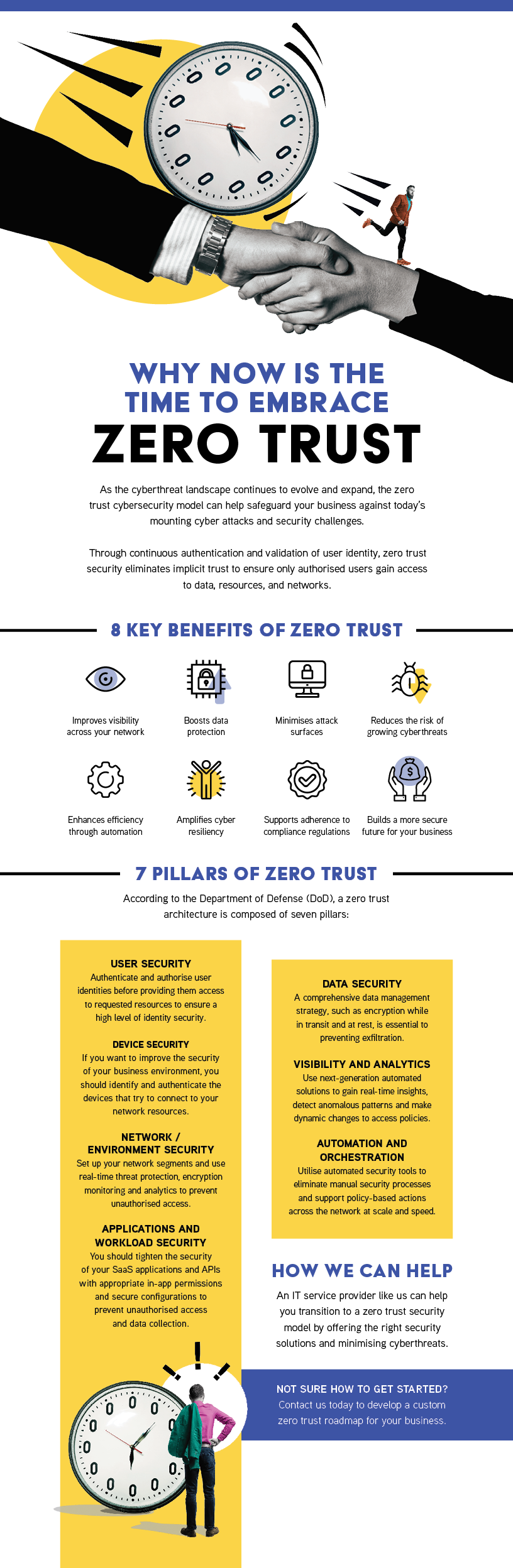
Territory Technology Solutions Zero Trust Jacob breaks down what zero trust really means and why it’s essential for protecting your business in under 5 minutes. Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Discover what is zero trust security and how to implement it. learn zero trust cyber security, zero trust data security, and practical steps—plus how amplify security accelerates zero trust enforcement. Discover zero trust security explained simply for beginners. learn the zero trust security model, principles, and how it beats traditional security in modern cybersecurity.
Zero Trust Security Model Explained Principles Architectu Blog Discover what is zero trust security and how to implement it. learn zero trust cyber security, zero trust data security, and practical steps—plus how amplify security accelerates zero trust enforcement. Discover zero trust security explained simply for beginners. learn the zero trust security model, principles, and how it beats traditional security in modern cybersecurity.
Zero Trust Security Model Explained Principles Architectu Blog
Comments are closed.