Zero Trust Explained In 5 Minutes
Enable Zero Trust Bigid That’s where zero trust comes in. in this quick video, jacob breaks down what zero trust means, why it matters, and how it can protect your organization from modern cyberattacks. What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable.

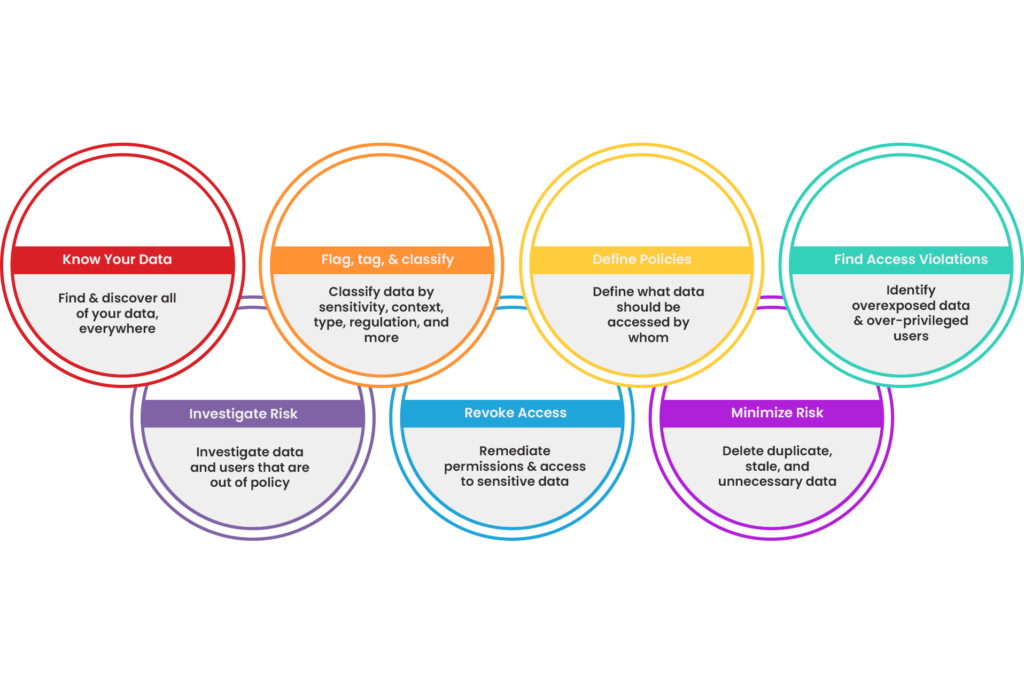
Zero Trust Explained Watch marc battigan, zscaler senior sales engineer, explain how zscaler’s zero trust enforces true user to app security. Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. Zero trust is a cybersecurity strategy that removes implicit trust and requires explicit, continuous verification for every access request, across users, devices, applications, workloads, and data, regardless of location. What is zero trust, and why should you consider implementing it in your company? the zero trust security model, also known as a zero trust architecture (zta), is an approach to designing and implementing it systems based on caution and scepticism.

Zero Trust Security Explained And Applied Xylos Zero trust is a cybersecurity strategy that removes implicit trust and requires explicit, continuous verification for every access request, across users, devices, applications, workloads, and data, regardless of location. What is zero trust, and why should you consider implementing it in your company? the zero trust security model, also known as a zero trust architecture (zta), is an approach to designing and implementing it systems based on caution and scepticism. Zero trust security is a modern cybersecurity framework centered around one core belief: never trust, always verify. no user, device, or application regardless of its location is granted implicit access. Zero trust: practical guides, insights, and real world strategies to help organisations implement zero trust security, manage risks, and stay compliant. What is zero trust security? zero trust security is an it security model that requires strict identity verification for every person and device trying to access resources on a private network, regardless of whether they are sitting within or outside of the network perimeter. Using continuously verified identities to manage network access, the zero trust methodology creates a stronger defense for your system while simplifying security and the users experience, ultimately creating safer and more efficient organizations.
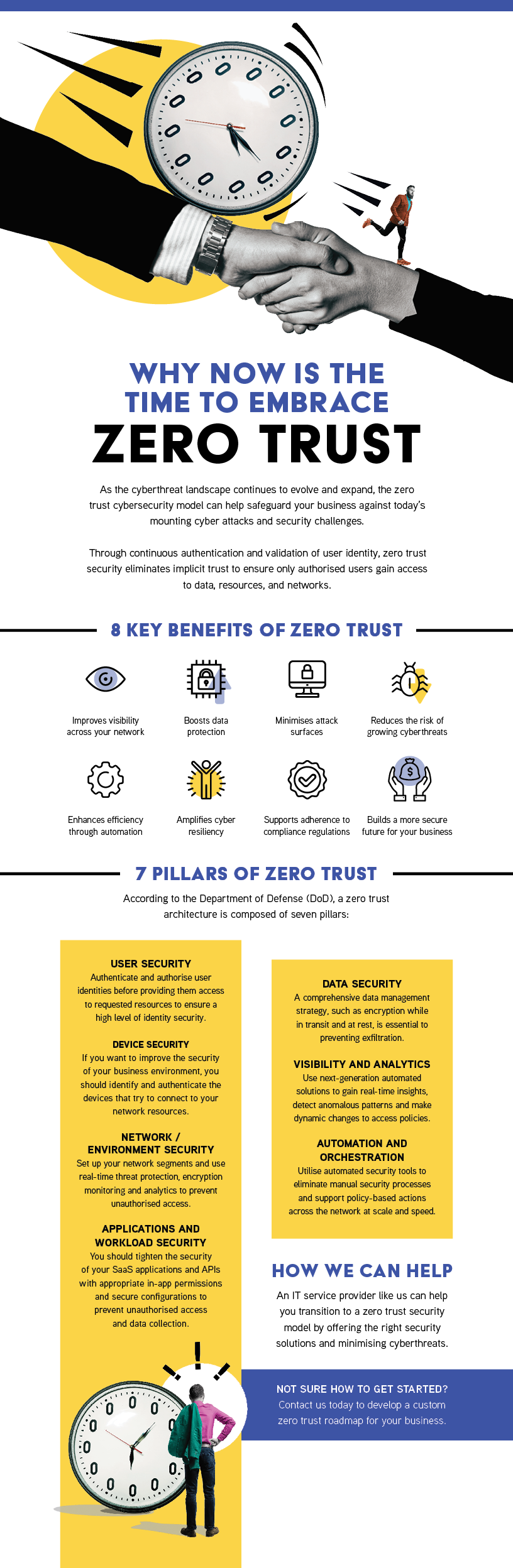
Territory Technology Solutions Zero Trust Zero trust security is a modern cybersecurity framework centered around one core belief: never trust, always verify. no user, device, or application regardless of its location is granted implicit access. Zero trust: practical guides, insights, and real world strategies to help organisations implement zero trust security, manage risks, and stay compliant. What is zero trust security? zero trust security is an it security model that requires strict identity verification for every person and device trying to access resources on a private network, regardless of whether they are sitting within or outside of the network perimeter. Using continuously verified identities to manage network access, the zero trust methodology creates a stronger defense for your system while simplifying security and the users experience, ultimately creating safer and more efficient organizations.
Comments are closed.