Zero Trust Explained In 4 Mins
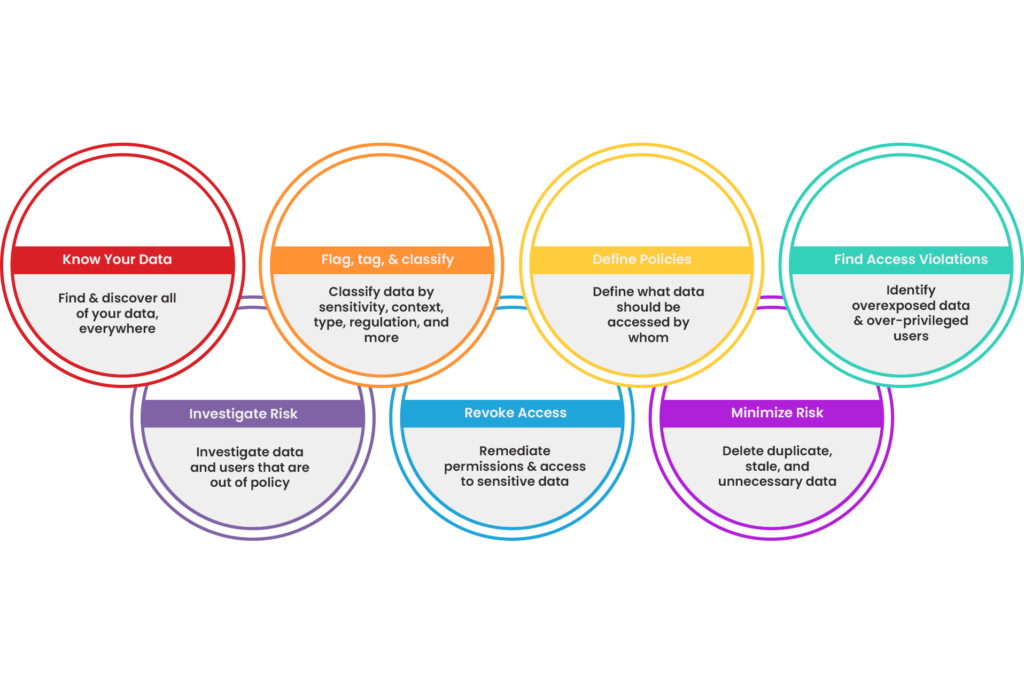
Enable Zero Trust Bigid Unify and integrate your security tools to protect your most valuable assets and proactively manage threats. A zero trust approach aims to wrap security around every user, every device, every connection — every time. unify and integrate your security tools to protect your most valuable assets and proactively manage threats.

Zero Trust Explained The zero trust security approach offers a paradigm shift by eliminating implicit trust and enforcing strict verification for every access request. this article explores the principles, implementation strategies, and benefits of zero trust security to minimize risks effectively. In this edition of behind the buzzword, we cover a hot topic in the tech industry right now: zero trust. here's what you need to know about it, explained in a four minute read. What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud.
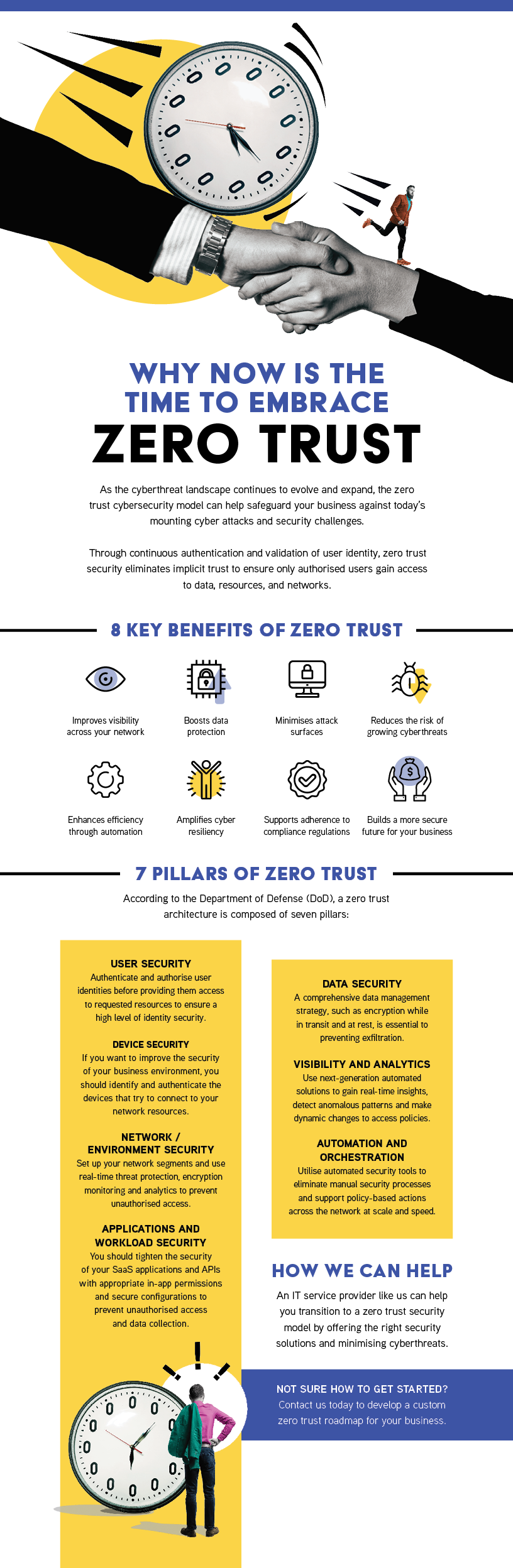
Territory Technology Solutions Zero Trust What is zero trust? the basics explained as government services move online and across systems, zero trust becomes essential to ensuring every interaction is secure and verifiable. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. Zero trust explained in 4 minutes: for those of you who would rather watch a video than read an article, here is a great video by ibm security that explains the model in four minutes!. Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust is a security model based on one core idea: access should never be granted solely because something is inside a network perimeter. instead, every request is evaluated continuously based on identity, device state, and context.
Zero Trust Security Model Explained Principles Architectu Blog Zero trust explained in 4 minutes: for those of you who would rather watch a video than read an article, here is a great video by ibm security that explains the model in four minutes!. Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust is a security model based on one core idea: access should never be granted solely because something is inside a network perimeter. instead, every request is evaluated continuously based on identity, device state, and context.
Comments are closed.