Zero Trust Essentials Team Technology

Zero Trust Essentials Team Technology Protect against modern threats with a zero trust security strategy powered by ai. discover zero trust security and strategy today with microsoft security. Distributed tech teams face unique cybersecurity challenges, but these can be effectively managed with a combination of zero trust frameworks, identity management, encryption, and endpoint.

Zero Trust Essentials Smitix Services Ltd Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. How can organizations foster team trust in environments governed by the "never trust, always verify" principles of zero trust?. Zero trust is a modern cybersecurity strategy based on "never trust, always verify," meaning no user, device, or application is inherently trusted, even if inside the network. it requires strict identity verification for every access request, and grants only the minimum necessary privileges.
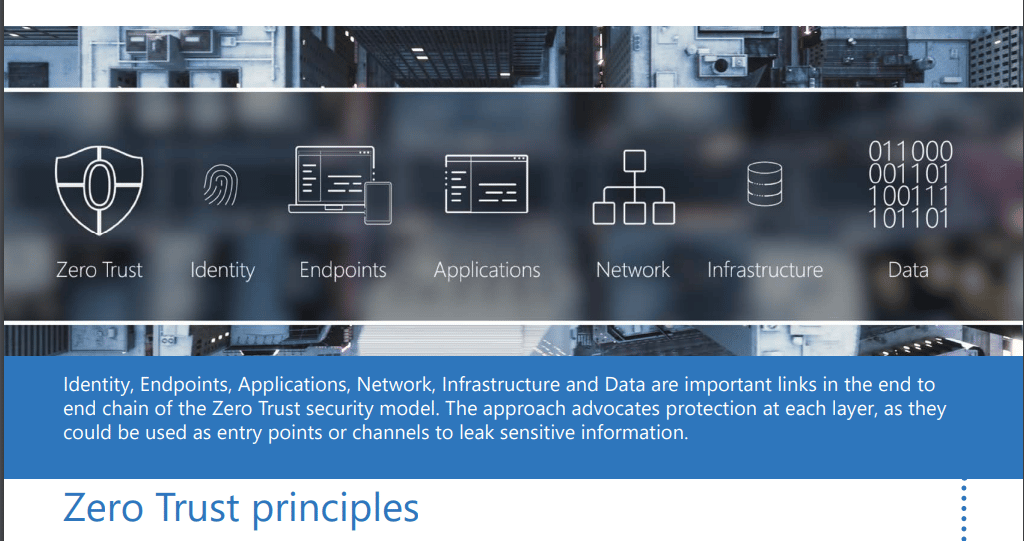
Disc Infosec Blogzero Trust Essentials Ebook Disc Infosec Blog How can organizations foster team trust in environments governed by the "never trust, always verify" principles of zero trust?. Zero trust is a modern cybersecurity strategy based on "never trust, always verify," meaning no user, device, or application is inherently trusted, even if inside the network. it requires strict identity verification for every access request, and grants only the minimum necessary privileges. With solutions like tailscale or cloudflare zero trust, teams can implement identity aware routing to internal resources, removing the need for clunky vpns while retaining strong security controls. Today’s cybersecurity landscape has promoted zero trust to the top of the agenda for teams and cisos alike. nitin uttreja, cissp, shares his experience and a plan for implementing zero trust in an organization. There are several ways that we help you to apply zero trust protections to your applications. we have already looked at the benefits of azure ad as the single entity provider for authenticated sign in, as well as the use of conditional access. Conclusion a perimeter less world requires zero trust for security because it eliminates the idea of trusting people and verifies every action a user takes while using real time visibility over all assets. this type of approach allows smaller security teams to defend against larger threats. by implementing zero trust, organizations can reduce breach risk, accelerate compliance achievement, and.
Comments are closed.