Zero Trust Create A Roadmap

Zero Trust Roadmap Pdf Cloud Computing Cyberspace This roadmap was built by security experts to provide a vendor agnostic zero trust architecture and example implementation timeline. the timeline assumes that an organization is beginning their zero trust journey from scratch, but is meant to be useful for all organizations. To help, we’ve built a vendor neutral roadmap for the entire zero trust journey, covering these five projects and others like them. some will take far longer than a few days, but the roadmap can provide greater clarity into what zero trust adoption means.

Zero Trust Roadmap Wp Pdf Computer Network Proxy Server A practical, stage by stage zero trust implementation guide. learn how to move from legacy perimeter security to zero trust without disrupting operations—with real milestones and decision criteria. This roadmap provides precise, step by step guidance for implementing a secure zero trust posture, along with measurable milestones to track progress. create a detailed, customized zero trust roadmap that is relevant to your organization. measure progress and impact of your zt journey. This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. Follow our proven five step roadmap, deployment checklist, and expert faqs to roll out a zero trust security model without derailing operations.
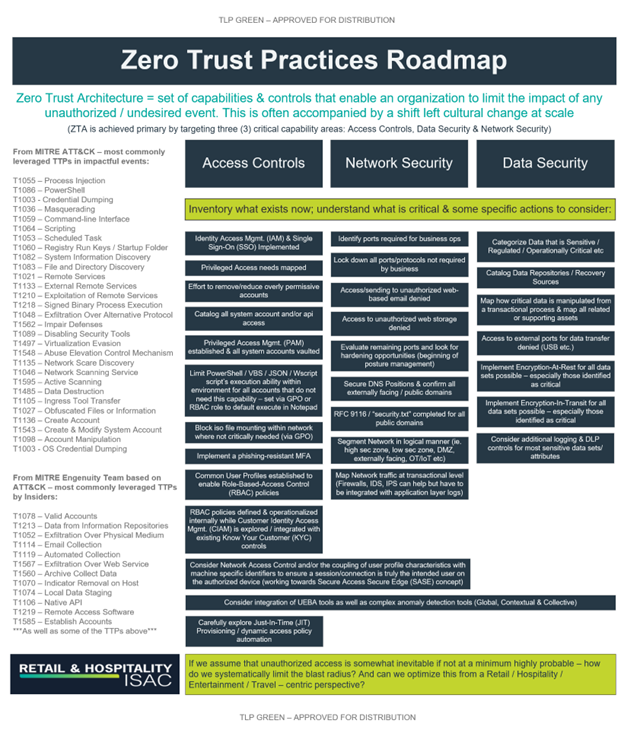
Rh Isac A Roadmap To Zero Trust Maturity Rh Isac This post was inspired by the zero trust journey takeaways outlined in nist special publication 1800 35, which offers an in depth technical roadmap for organizations looking to implement zero trust across complex environments. Follow our proven five step roadmap, deployment checklist, and expert faqs to roll out a zero trust security model without derailing operations. Learn how to create a zero trust roadmap tailored to your organization. discover key steps, best practices, and expert insights to enhance security and resilience. This guide provides a phased roadmap for enterprise zero trust adoption based on real world deployments, including how to handle legacy systems and avoid business disruption. The full report provides a detailed step by step approach to designing and implementing a zero trust roadmap, addressing each stage of the process. by following the recommendations and avoiding common pitfalls, organizations can successfully transition to the zero trust security model. Once you have built out your zero trust architecture for all the other elements of your organization, there are a set of actions you can take to move your organization to a zero trust steady state, ensuring consistency with the architecture moving forward.
Comments are closed.