Zero Trust Automation Full Architecture Breakdown

Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac Zero trust architecture guide: components, nist model, implementation roadmap, maturity stages, and enterprise security metrics. Deep dive into zero trust architecture principles, implementation components, and performance trade offs with real world examples from 2026. learn about identity centric security, sase, and ai driven threat detection.

Zero Trust Architecture This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. Fortunately, the journey doesn’t have to be an all or nothing leap; it can be approached as a structured, phased roadmap. this guide outlines a practical path, breaking down the transformation into manageable steps your organization can follow to build a resilient, modern security posture. In conclusion, designing a zero trust architecture is essential for modern cybersecurity. it shifts the focus from relying on perimeter defenses to continuously verifying every user, device, and connection within a network. In this article, we’ll break down what zero trust is, why it matters, its main benefits, and how your organization can begin to adopt it. what is zero trust architecture (zta)? zta was created and formalized by nist (national institute of standards and technology).
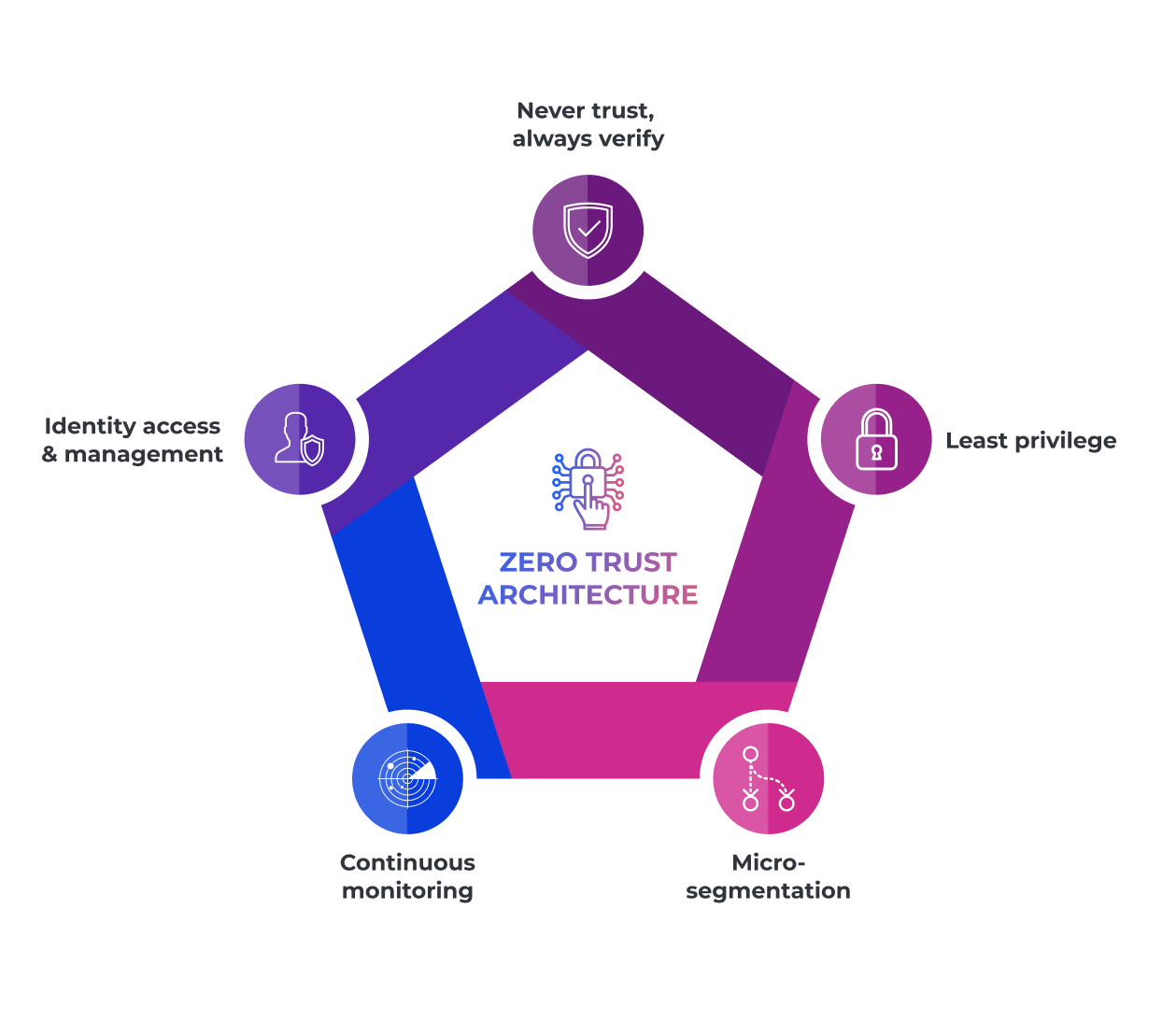
The Comprehensive Guide To Zero Trust Architecture In conclusion, designing a zero trust architecture is essential for modern cybersecurity. it shifts the focus from relying on perimeter defenses to continuously verifying every user, device, and connection within a network. In this article, we’ll break down what zero trust is, why it matters, its main benefits, and how your organization can begin to adopt it. what is zero trust architecture (zta)? zta was created and formalized by nist (national institute of standards and technology). Master zero trust architecture with this comprehensive guide covering principles, components, and implementation strategies for modern cybersecurity. Developed with the expertise of cybersecurity professionals and industry leaders, this guide provides valuable insights, best practices, and key considerations to aid federal agencies in their journey toward implementing a zta. Step by step zero trust plan: inventory assets, enforce strong identity and mfa, segment networks, deploy dlp and detection, automate policies, and roll out in phases. Zero trust architecture (zta) is redefining cybersecurity by eliminating implicit trust. learn the core principles, benefits, implementation steps, and best practices for adopting a zero trust model.

Zero Trust Architecture Master zero trust architecture with this comprehensive guide covering principles, components, and implementation strategies for modern cybersecurity. Developed with the expertise of cybersecurity professionals and industry leaders, this guide provides valuable insights, best practices, and key considerations to aid federal agencies in their journey toward implementing a zta. Step by step zero trust plan: inventory assets, enforce strong identity and mfa, segment networks, deploy dlp and detection, automate policies, and roll out in phases. Zero trust architecture (zta) is redefining cybersecurity by eliminating implicit trust. learn the core principles, benefits, implementation steps, and best practices for adopting a zero trust model.

Zero Trust Network Access Logical Components Of Zero Trust Architecture Step by step zero trust plan: inventory assets, enforce strong identity and mfa, segment networks, deploy dlp and detection, automate policies, and roll out in phases. Zero trust architecture (zta) is redefining cybersecurity by eliminating implicit trust. learn the core principles, benefits, implementation steps, and best practices for adopting a zero trust model.
Comments are closed.