Zero Trust Authorization

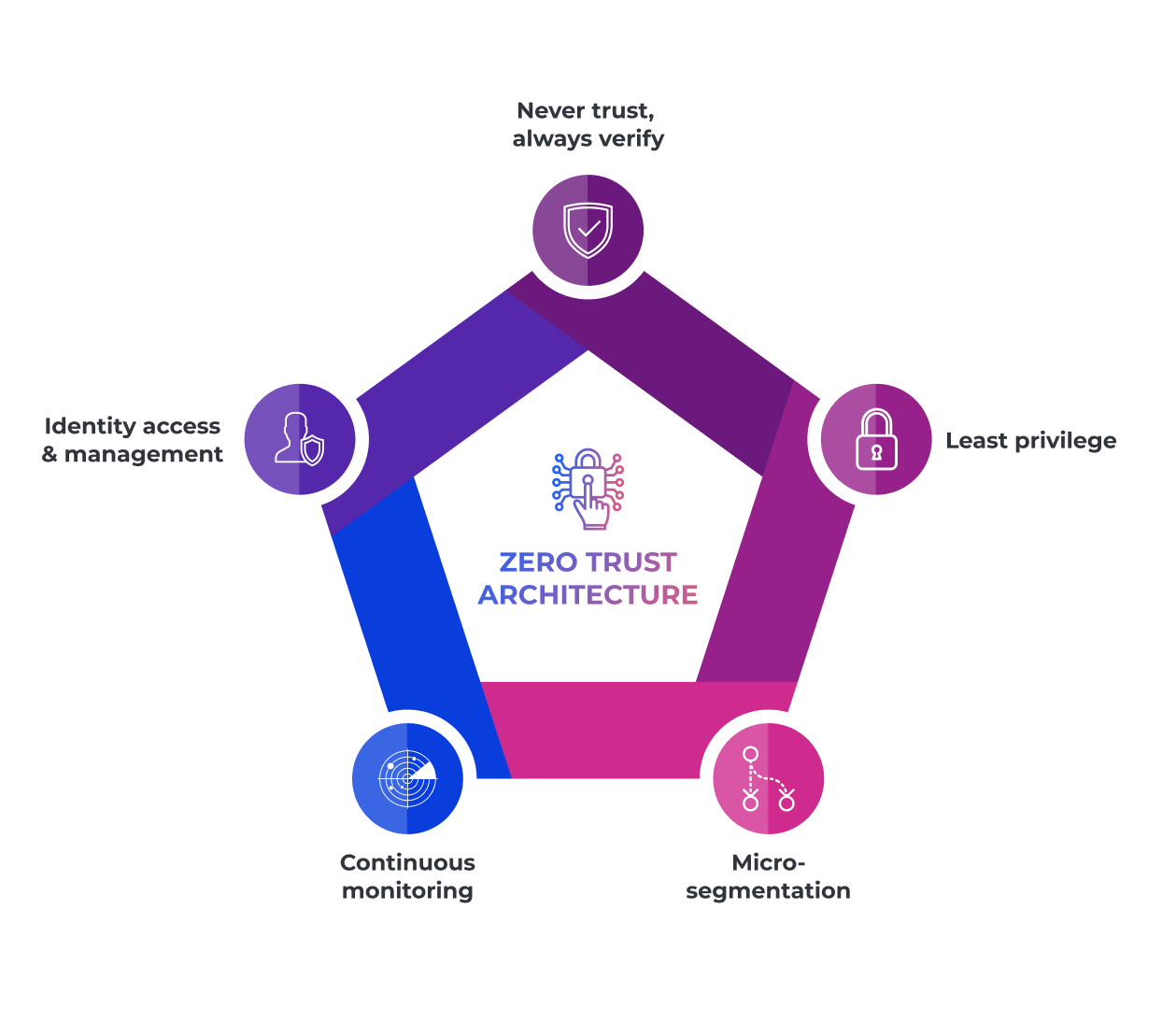
Zero Trust Networking Cohesive Networks Zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. traditional security works like a castle with walls. once you're inside, you can access everything. Zero trust is not a product or tool, but an essential security strategy that seeks to continuously verify every transaction, asserts least privilege access, and assumes that every transaction could be a possible attack.

Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac Permanent elevated privileges are removed, and users pes are required to request just in time (jit) access for administrative tasks, aligning with zero trust (zt) principles by ensuring. This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security. Zero trust is a cloud security model designed to secure modern organizations by removing implicit trust and enforcing strict identity authentication and authorization. What is zero trust architecture? zero trust architecture is a security framework and operational model that replaces perimeter based trust with continuous verification. it asserts that all access requests—whether from inside or outside the network—must be authenticated, authorized, and inspected based on identity, device posture, and context before granting least privilege access. what it.

The Comprehensive Guide To Zero Trust Architecture Zero trust is a cloud security model designed to secure modern organizations by removing implicit trust and enforcing strict identity authentication and authorization. What is zero trust architecture? zero trust architecture is a security framework and operational model that replaces perimeter based trust with continuous verification. it asserts that all access requests—whether from inside or outside the network—must be authenticated, authorized, and inspected based on identity, device posture, and context before granting least privilege access. what it. Discover the essentials of zero trust authorization (zta) in this guide, starting with key principles like continuous verification, least privileged access, and granular policy controls. learn how to implement zta, overcome common challenges, and streamline the process using open source solutions. What zero trust actually means in azure zero trust is a security model built on one principle: never trust, always verify. instead of assuming everything inside your network perimeter is safe, zero trust assumes breach and verifies every access request explicitly — regardless of where it comes from. in traditional perimeter based security, once a user or device is inside the network they're. The zero trust architecture replaces implicit trust with continuous verification. every access request to applications, network resources, or sensitive data must be authenticated, authorized, and evaluated through strict access controls. Discover how zero trust architecture enhances security by verifying every user and device, ensuring trusted access in today's evolving it environments.
The Comprehensive Guide To Zero Trust Architecture Discover the essentials of zero trust authorization (zta) in this guide, starting with key principles like continuous verification, least privileged access, and granular policy controls. learn how to implement zta, overcome common challenges, and streamline the process using open source solutions. What zero trust actually means in azure zero trust is a security model built on one principle: never trust, always verify. instead of assuming everything inside your network perimeter is safe, zero trust assumes breach and verifies every access request explicitly — regardless of where it comes from. in traditional perimeter based security, once a user or device is inside the network they're. The zero trust architecture replaces implicit trust with continuous verification. every access request to applications, network resources, or sensitive data must be authenticated, authorized, and evaluated through strict access controls. Discover how zero trust architecture enhances security by verifying every user and device, ensuring trusted access in today's evolving it environments.

Zero Trust Privileged Access Management Pam Solution Strongdm The zero trust architecture replaces implicit trust with continuous verification. every access request to applications, network resources, or sensitive data must be authenticated, authorized, and evaluated through strict access controls. Discover how zero trust architecture enhances security by verifying every user and device, ensuring trusted access in today's evolving it environments.
Comments are closed.