Zero Trust Architecture The Future Of It Security

Zero Trust Security Architecture Cybersecurity Magazine Explore the future of zero trust architecture in cybersecurity, driven by ai, automation, and identity based security. learn how zta enhances protection with continuous verification, supports cloud and remote environments, and strengthens defence against modern cyber threats in evolving digital ecosystems. As traditional perimeter based security models become increasingly ineffective against modern cyber threats, zero trust architecture (zta) has emerged as a transformative approach to.

Zero Trust Architecture Cybersecurity S Future Hts "explore how zero trust architecture is reshaping it security by eliminating implicit trust, strengthening access controls, and protecting against modern cyber threats.". Explore how identity intelligence, ai driven verification, global compliance shifts, and sase convergence are redefining zero trust security and shaping the next era of digital resilience. As zero trust architectures continues to be adopted and evolved, there will be a strong em phasis on endpoint detection and response (edr) solutions to en sure the security of all devices ac cessing the network. In this paper we delve into the core concepts of zero trust architecture, dissecting the underpinnings microsegmentation, least privilege access and continuous monitoring.
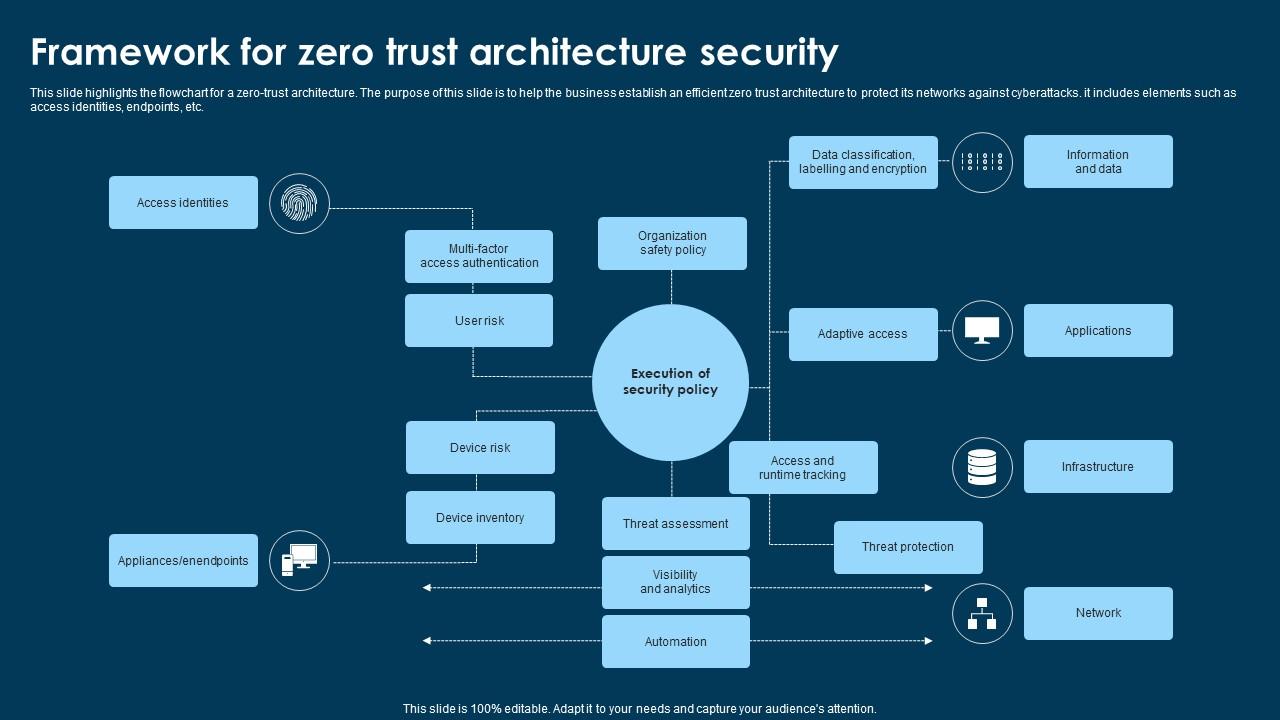
Framework For Zero Trust Architecture Security Ppt Example As zero trust architectures continues to be adopted and evolved, there will be a strong em phasis on endpoint detection and response (edr) solutions to en sure the security of all devices ac cessing the network. In this paper we delve into the core concepts of zero trust architecture, dissecting the underpinnings microsegmentation, least privilege access and continuous monitoring. Explore how zero trust architecture enables cyber resilience across multi cloud environments, with core principles and practical implementation strategies. Abstract: the implementation and benefits of zero trust (zt) architectures across various domains. the shift from traditional perimeter based security models to zt models, which advocate for continuous verification and stringent access controls. Explore the essential guide to zero trust architecture principles, benefits, implementation steps, and industry use cases to secure your enterprise in 2025. Explore how zero trust architecture is transforming cybersecurity with key insights, adoption trends, and market growth projections.
Comments are closed.