Zero Trust Architecture Redefining Cybersecurity

Zero Trust Architecture Redefining Cybersecurity For Modern This research article examines the concept of zero trust architecture and its effectiveness in protecting against insider threats and advanced persistent threats (apts) in modern network. Zero trust architecture represents a fundamental reconceptualization of enterprise security strategy, moving from location based trust to continuous verification of every access request regardless of source.
Zero Trust Architecture Redefining Cybersecurity The increasing complexity of digital ecosystems and evolving cybersecurity threats have highlighted the limitations of traditional perimeter based security models, leading to the growing adoption of zero trust architecture (zta). The emergence of zero trust architecture (zta) marks a significant shift in cybersecurity paradigms, redefining how organizations approach security in an increasingly complex digital landscape. Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Explore how identity intelligence, ai driven verification, global compliance shifts, and sase convergence are redefining zero trust security and shaping the next era of digital resilience.

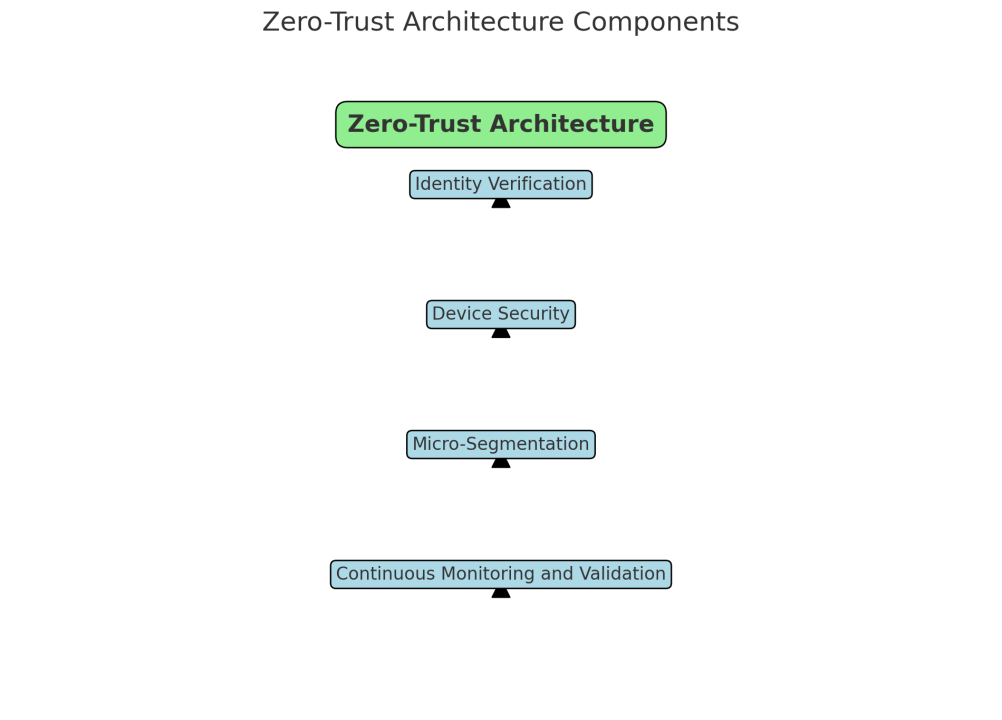
Understanding Zero Trust Architecture Redefining Cybersecurity Paradigms Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Explore how identity intelligence, ai driven verification, global compliance shifts, and sase convergence are redefining zero trust security and shaping the next era of digital resilience. This article explores the fundamentals of zero trust architecture, its core principles, benefits, and how organizations can implement it to strengthen their cybersecurity posture. We present a detailed survey of the zero trust (zt) security paradigm which has a growing number of advocates in the critical infrastructure risk management space. Zero trust architecture is a cybersecurity framework designed to prevent unauthorized access to systems and data by enforcing strict identity verification and access controls. Zero trust architecture (zta) is redefining cybersecurity by eliminating implicit trust. learn the core principles, benefits, implementation steps, and best practices for adopting a zero trust model.
Comments are closed.