Zero Trust Architecture Principles Components Benefits Explained
Zero Trust Architecture Key Components And Considerations Get a comprehensive guide to key zero trust concepts, the most influential frameworks, top zero trust benefits, and best practices for selecting a zero trust vendor. In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy.

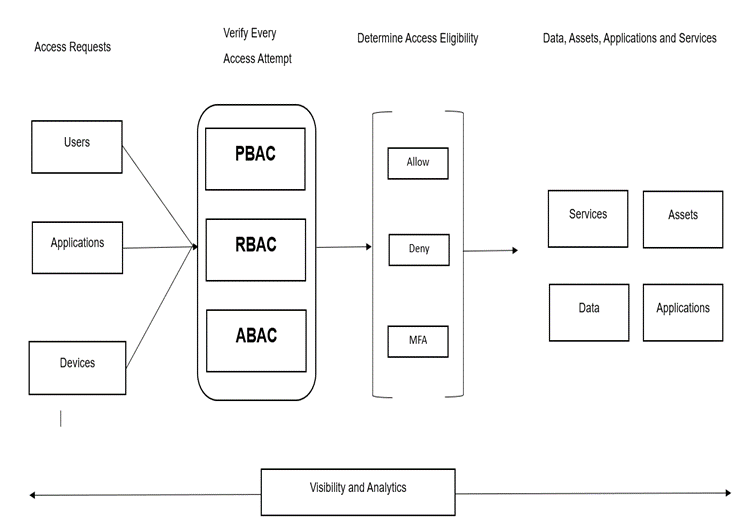
Zero Trust Network Access Logical Components Of Zero Trust Architecture This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. Learn how zero trust architecture transforms security. discover core concepts, components, real world examples, and steps for effective modern protection. Zero trust architecture outlines how these principles are applied across an enterprise's systems, networks, and workflows to ensure that no entity (user, device, or application) gains access without thorough validation. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization.
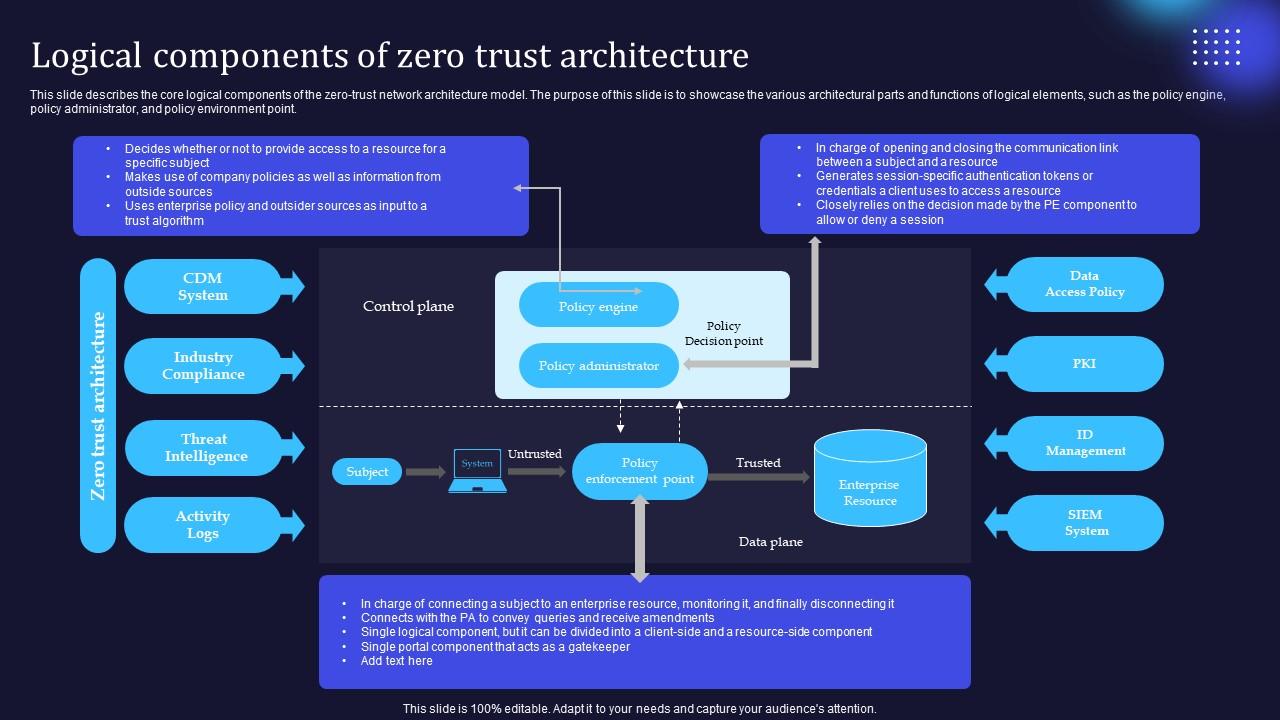
Zero Trust Model Logical Components Of Zero Trust Architecture Zero trust architecture outlines how these principles are applied across an enterprise's systems, networks, and workflows to ensure that no entity (user, device, or application) gains access without thorough validation. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Zero trust architecture represents the future of enterprise security, moving beyond perimeter based defenses to create truly resilient security postures. while implementation requires significant planning and investment, the security benefits extend far beyond traditional compliance requirements. Learn what zero trust architecture is, how it works, and how organizations apply nist zero trust principles to reduce cyber risk. Explore zero trust architecture with this study guide covering its core concepts, components, tenets, and implementation strategies for modern enterprise security. Zero trust architecture (zta) emerges as a pivotal paradigm shift, fundamentally redefining organizational cybersecurity by eliminating implicit trust and enforcing continuous verification of.

Guiding Principles Of Zero Trust Architecture 2024 Zero trust architecture represents the future of enterprise security, moving beyond perimeter based defenses to create truly resilient security postures. while implementation requires significant planning and investment, the security benefits extend far beyond traditional compliance requirements. Learn what zero trust architecture is, how it works, and how organizations apply nist zero trust principles to reduce cyber risk. Explore zero trust architecture with this study guide covering its core concepts, components, tenets, and implementation strategies for modern enterprise security. Zero trust architecture (zta) emerges as a pivotal paradigm shift, fundamentally redefining organizational cybersecurity by eliminating implicit trust and enforcing continuous verification of.
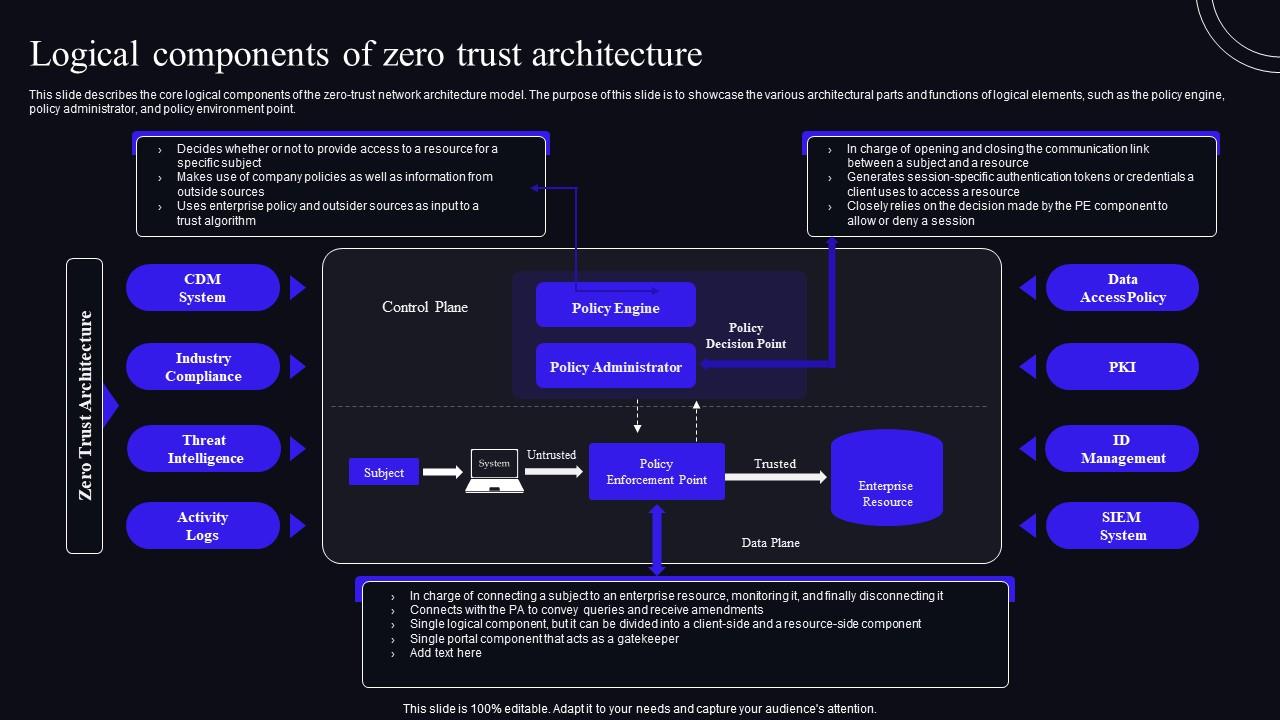
Logical Components Of Zero Trust Architecture Zero Trust Security Model Explore zero trust architecture with this study guide covering its core concepts, components, tenets, and implementation strategies for modern enterprise security. Zero trust architecture (zta) emerges as a pivotal paradigm shift, fundamentally redefining organizational cybersecurity by eliminating implicit trust and enforcing continuous verification of.
Comments are closed.