Zero Trust Architecture In Azure
Zero Trust Architecture In Microsoft Azure Kate S Tech Blog Learn how to apply the guiding principles of zero trust to azure infrastructure and services. A practical step by step guide to implementing zero trust network access in azure using microsoft entra, conditional access, and azure firewall.

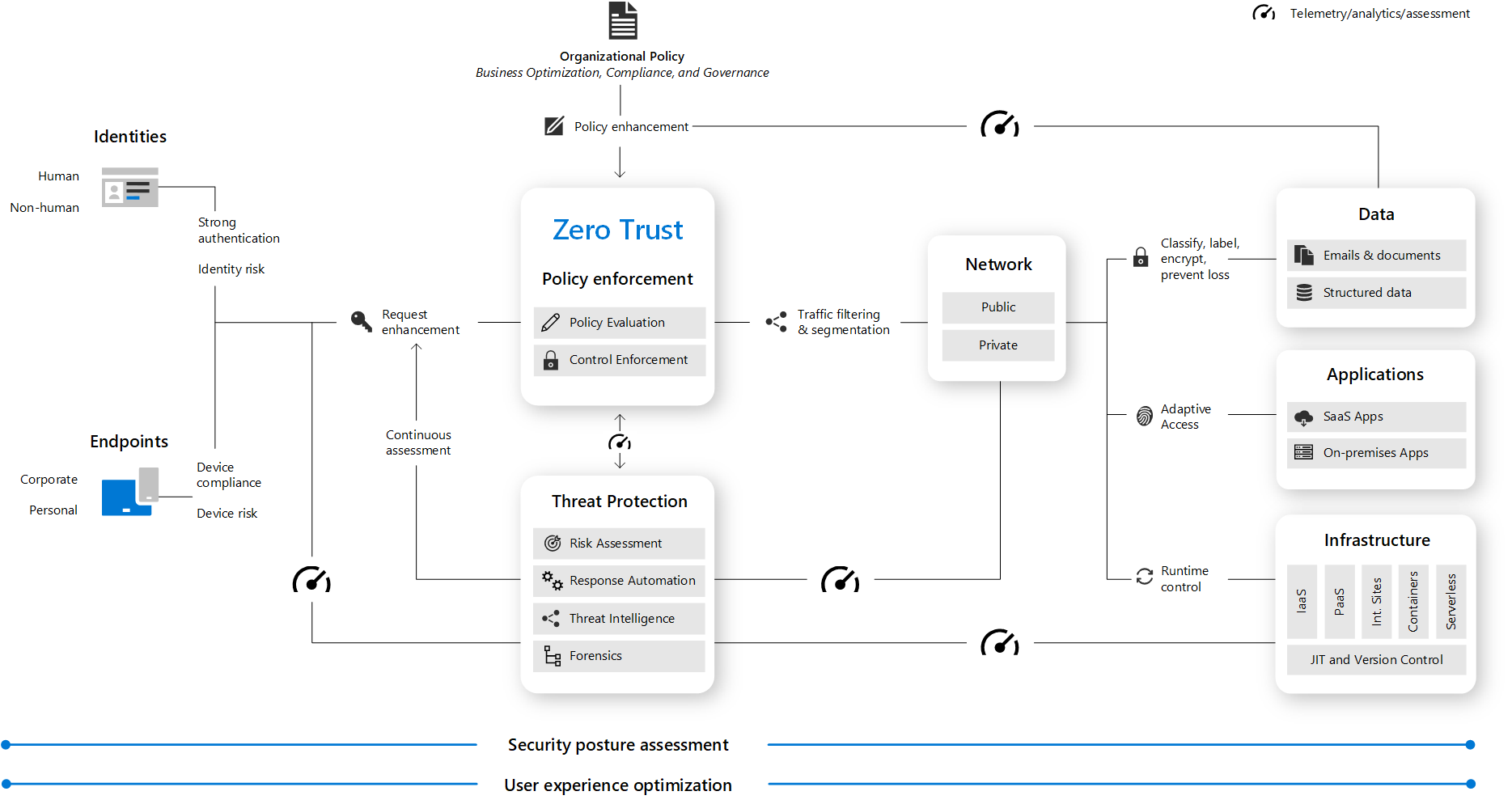
Zero Trust Architecture For Azure Managed Databases The Teck Talk Goal: build a robust zero trust security framework in azure that explicitly verifies every access request, limits blast radius, and enforces least privilege. while staying cost effective and. On day 2 of our azure well architected framework series, we focus on applying zero trust principles in azure. we’ll explore how to leverage microsoft services to verify identities, secure endpoints, segment networks, protect data, and continuously monitor for threats. Comprehensive guide to zero trust architecture in azure using microsoft entra id, conditional access, device compliance, rbac, and risk based access control. Azure zero trust is implemented by combining entra id, conditional access, azure networking controls, and continuous monitoring. users and workloads authenticate through entra id using mfa and risk based policies. access to azure resources is controlled using rbac and managed identities.

Microsoft Azure Zero Trust Architecture Secure Cloud Migration With Comprehensive guide to zero trust architecture in azure using microsoft entra id, conditional access, device compliance, rbac, and risk based access control. Azure zero trust is implemented by combining entra id, conditional access, azure networking controls, and continuous monitoring. users and workloads authenticate through entra id using mfa and risk based policies. access to azure resources is controlled using rbac and managed identities. In azure environments, the shift to zero trust is particularly important because cloud resources exist outside traditional network perimeters. organizations must embrace a zero trust approach to access control as they embrace remote work and use cloud technology to transform their business model. In this post, we’ll explore zero trust architecture in azure, examining its principles, key components, and how azure’s native tools empower organizations to implement this model effectively. Discover how to implement a robust zero trust architecture in azure with techrupt's comprehensive guide. learn practical strategies to secure your cloud environment through identity verification, least privilege access, and continuous monitoring. This paper describes how microsoft azure uses zta to enforce strict identity verification and access rules across the cloud environment to improve security. implementation takes time and effort. azure’s extensive services and customizations require careful design and implementation.
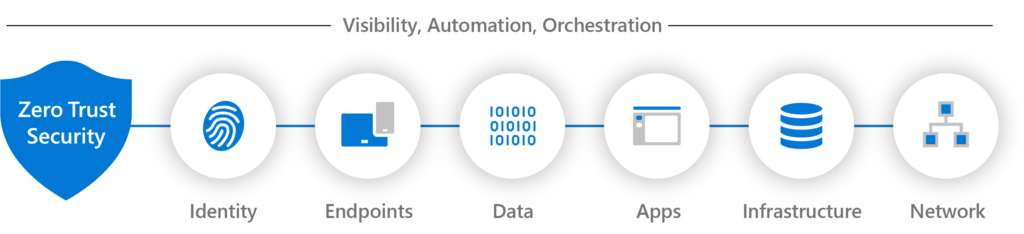
Day 4 Zero Trust Architecture In Azure In azure environments, the shift to zero trust is particularly important because cloud resources exist outside traditional network perimeters. organizations must embrace a zero trust approach to access control as they embrace remote work and use cloud technology to transform their business model. In this post, we’ll explore zero trust architecture in azure, examining its principles, key components, and how azure’s native tools empower organizations to implement this model effectively. Discover how to implement a robust zero trust architecture in azure with techrupt's comprehensive guide. learn practical strategies to secure your cloud environment through identity verification, least privilege access, and continuous monitoring. This paper describes how microsoft azure uses zta to enforce strict identity verification and access rules across the cloud environment to improve security. implementation takes time and effort. azure’s extensive services and customizations require careful design and implementation.
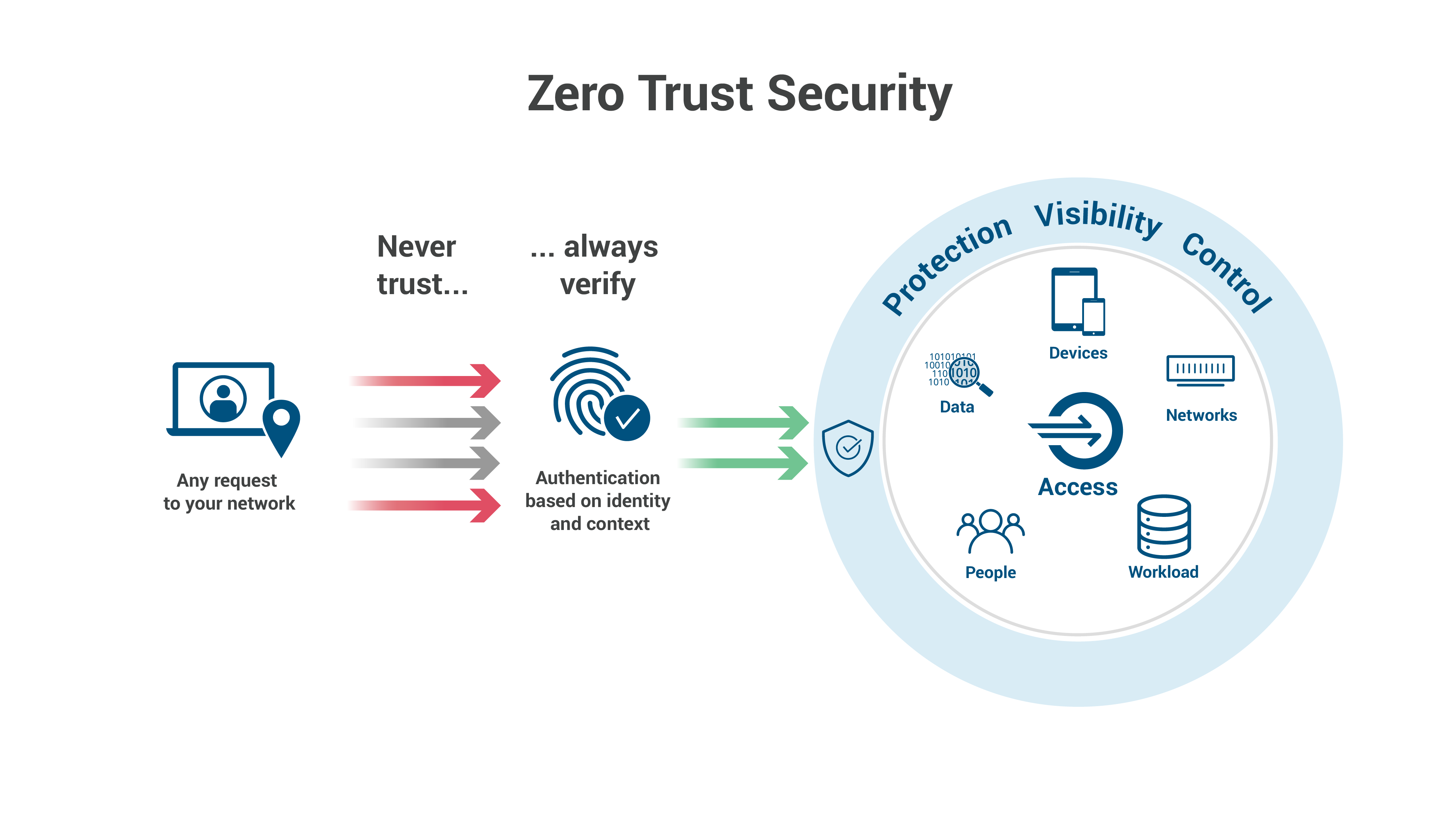
Implementing Zero Trust Architecture On Azure Hybrid Cloud Discover how to implement a robust zero trust architecture in azure with techrupt's comprehensive guide. learn practical strategies to secure your cloud environment through identity verification, least privilege access, and continuous monitoring. This paper describes how microsoft azure uses zta to enforce strict identity verification and access rules across the cloud environment to improve security. implementation takes time and effort. azure’s extensive services and customizations require careful design and implementation.
Comments are closed.