Zero Trust Architecture Implementation Challenges And Solutions
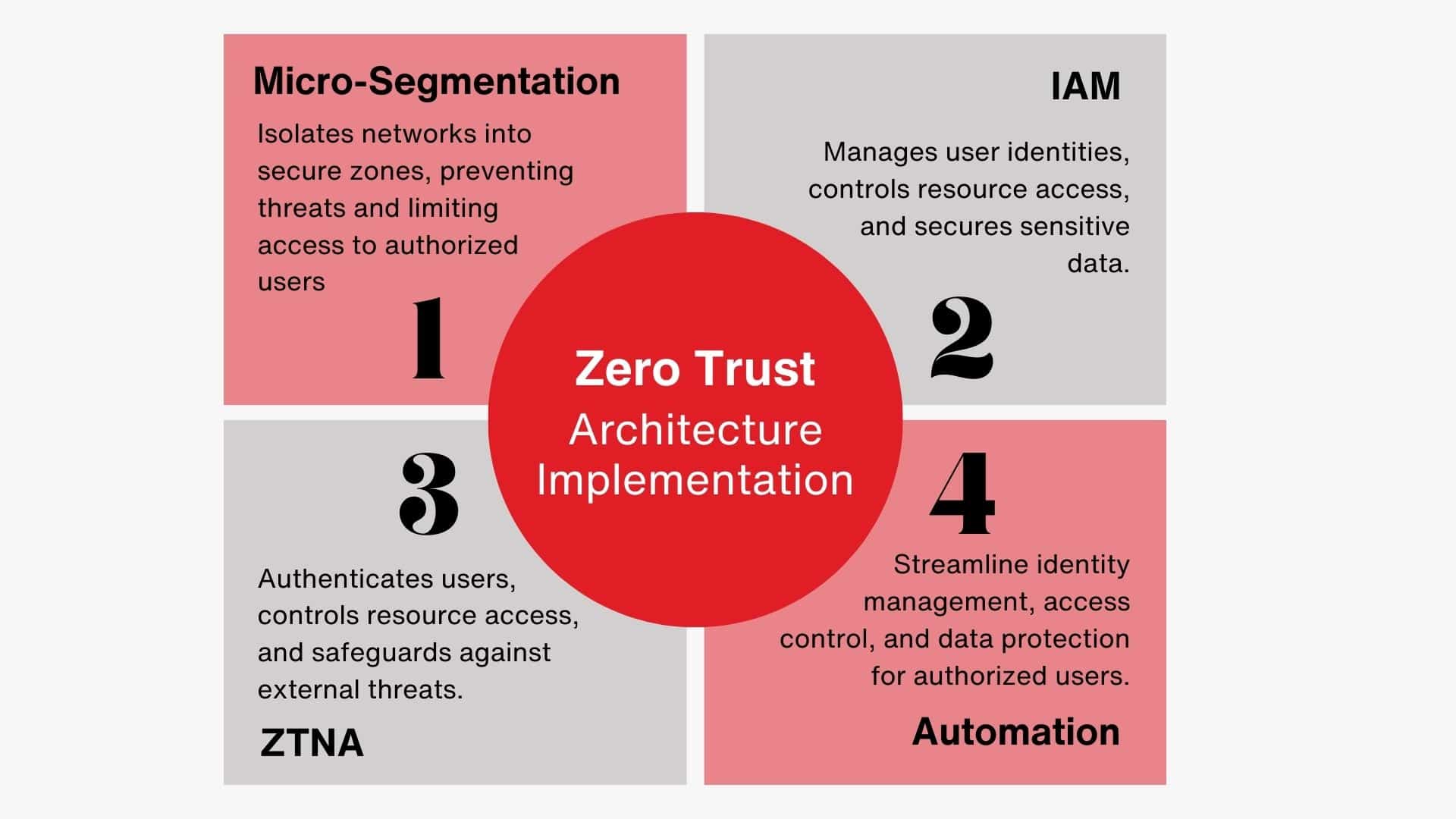
Zero Trust Architecture Implementation Challenges And Solutions Zero trust architecture (zta) improves security by verifying every access attempt, but implementing it has challenges—from legacy systems to compliance issues. learn to overcome 8 key hurdles and deploy zta strategically in your infrastructure. Zero trust architecture (zta) is a broad security approach that emphasizes verifying trust for every access attempt across a network. zta operates on the “never trust, always verify” principle, meaning every access request is scrutinized before granting permission.

Zero Trust Architecture Implementation Challenges And Solutions Knowing how to implement zero trust security requires an understanding of the most common obstacles you may encounter. these include complex infrastructures, cost, effort, and the need for flexible software solutions. organizations must also be aware of the potential risks associated with zero trust architecture. Learn about the most common zero trust implementation challenges that organizations face, and how they can be overcome. These case studies illustrate how zero trust architecture (zta) can be tailored to address specific cybersecurity challenges and organizational needs across different sectors. Enterprises grapple with network security challenges, including legacy systems, cultural resistance, and resource constraints. this piece explores those zero‑trust adoption barriers, maps.

Challenges To Zero Trust Network Architecture Implementation Ppt Slide These case studies illustrate how zero trust architecture (zta) can be tailored to address specific cybersecurity challenges and organizational needs across different sectors. Enterprises grapple with network security challenges, including legacy systems, cultural resistance, and resource constraints. this piece explores those zero‑trust adoption barriers, maps. Learn how to implement zero trust architecture with best practices, overcome challenges, and ensure compliance for robust cybersecurity. Despite its conceptual strength, the practical implementation of zta faces multiple challenges, including the lack of standard frameworks, difficulty in orchestration, limited interoperability, and the need for significant policy configuration. It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Discover the top challenges organizations face when implementing zero trust architecture and learn practical strategies to overcome them.
Zero Trust Network Architecture Implementation By Bhuvanesh C On Prezi Learn how to implement zero trust architecture with best practices, overcome challenges, and ensure compliance for robust cybersecurity. Despite its conceptual strength, the practical implementation of zta faces multiple challenges, including the lack of standard frameworks, difficulty in orchestration, limited interoperability, and the need for significant policy configuration. It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Discover the top challenges organizations face when implementing zero trust architecture and learn practical strategies to overcome them.

Zero Trust Implementation Challenges How To Solve Them It explores how organizations can transition to zero trust architectures, the challenges associated with its implementation, and the technologies that enable its adoption, such as artificial intelligence (ai), multi factor authentication (mfa), and zero trust network access (ztna). Discover the top challenges organizations face when implementing zero trust architecture and learn practical strategies to overcome them.

Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac
Comments are closed.