Zero Trust Architecture Explained

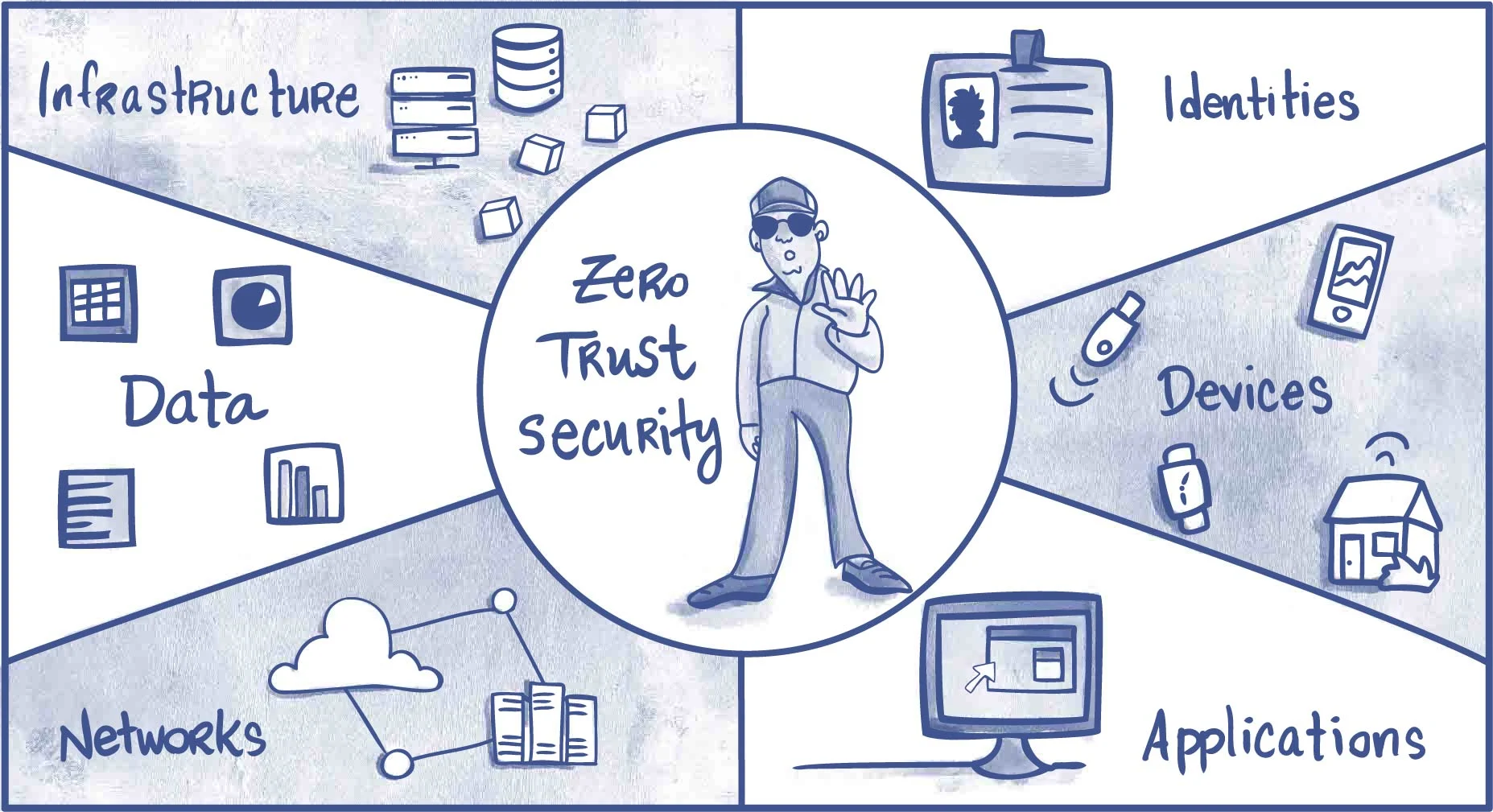
Rh Isac Zero Trust Architecture Zta How To Get Started Rh Isac Zero trust protects user accounts, devices, applications, and data wherever they're located. a zero trust approach should extend throughout the entire organization and serve as an integrated security philosophy and end to end strategy. Zero trust architecture (zta) is a security model that assumes no user, device, or network is trusted by default, whether inside or outside the organization's network. every access request must be authenticated, authorized, and continuously validated, applying the principle of least privilege.

Zero Trust Architecture In this article, we’ll break down nist 800 207 to show what a zero trust architecture really is, how it works, and why it’s not a product but a security philosophy. Zero trust is a security model where the core architecture assumes no entity, inside or outside the network, is trustworthy by default and requires strict verification. This guide explains what zero trust architecture is, its core principles, how it works, and why businesses should adopt it to secure their digital assets. what is zero trust architecture? zero trust architecture is a security model designed to eliminate implicit trust within a network. This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network.

The Comprehensive Guide To Zero Trust Architecture This guide explains what zero trust architecture is, its core principles, how it works, and why businesses should adopt it to secure their digital assets. what is zero trust architecture? zero trust architecture is a security model designed to eliminate implicit trust within a network. This cheat sheet will help you implement zero trust architecture (zta) in your organization. zero trust means "never trust, always verify" you don't trust anyone or anything by default, even if they're inside your network. Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. What is zero trust architecture? this article outlines what zero trust is, how zero trust works, the five core principles of zero trust, and the stages of implementing zero trust. By replacing outdated traditional security models and traditional perimeter based defenses, zero trust architecture ensures that access is tightly controlled, network traffic is monitored, and security measures are consistently enforced across all it environments.
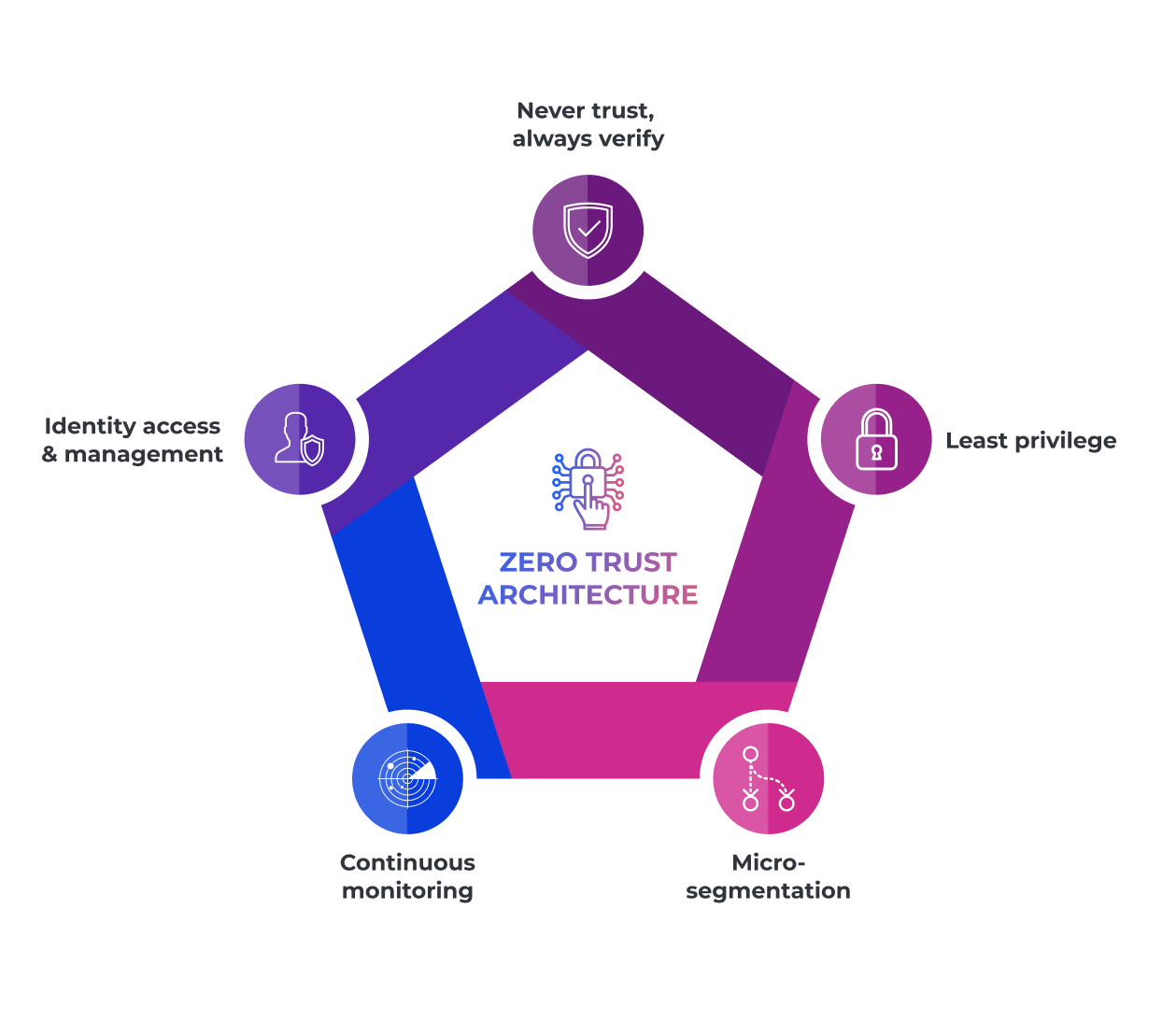
The Comprehensive Guide To Zero Trust Architecture Zero trust (zt) is the term for an evolving set of cybersecurity paradigms that move defenses from static, network based perimeters to focus on users, assets, and resources. a zero trust architecture (zta) uses zero trust principles to plan industrial and enterprise infrastructure and workflows. zero trust assumes there is no implicit trust granted to assets or user accounts based solely on. Zero trust architecture addresses security for all physical and virtual infrastructure, including routers, switches, servers, cloud services, and iot devices. it ensures that every component is continuously verified and protected, regardless of whether it resides on premises or in the cloud. What is zero trust architecture? this article outlines what zero trust is, how zero trust works, the five core principles of zero trust, and the stages of implementing zero trust. By replacing outdated traditional security models and traditional perimeter based defenses, zero trust architecture ensures that access is tightly controlled, network traffic is monitored, and security measures are consistently enforced across all it environments.
Zero Trust Explained How To Implement Zero Trust Architecture Reduce What is zero trust architecture? this article outlines what zero trust is, how zero trust works, the five core principles of zero trust, and the stages of implementing zero trust. By replacing outdated traditional security models and traditional perimeter based defenses, zero trust architecture ensures that access is tightly controlled, network traffic is monitored, and security measures are consistently enforced across all it environments.

Zero Trust Network Access Logical Components Of Zero Trust Architecture
Comments are closed.