Zero Trust Architecture Enhancing Network Security Secureblitz

Zero Trust Architecture Enhancing Network Security Secureblitz In this article, we’ll delve deep into the concept of zero trust architecture, exploring its principles, benefits, and implementation strategies to fortify your network against modern cyber threats. Zero trust architecture (zta) represents a significant shift in network security by moving away from the traditional perimeter based approach. instead, zta operates on the principle of.

Zero Trust Architecture Enhancing Network Security Secureblitz By providing highly performant, scalable, secure, integrated, and 601 cloaked zero trust access, appgate sdp is able to ensure that the correct device and user (under the 602 appropriate conditions at that moment in time) are connected. This guide provides a comprehensive overview of zero trust principles, architectural models, practical implementation steps, and the tools needed to build a more secure and resilient organization. Explore how zero trust architecture enables cyber resilience across multi cloud environments, with core principles and practical implementation strategies. This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems.

Zero Trust Architecture Enhancing Network Security Secureblitz Explore how zero trust architecture enables cyber resilience across multi cloud environments, with core principles and practical implementation strategies. This paper explores the zero trust architecture (zta) as a contemporary cybersecurity framework that addresses the challenges posed by increasingly interconnected systems. This article examines the combination of artificial intelligence (ai) with zero trust principles to improve the resilience of cyber security. this study demonstrates the enhanced accuracy, sensitivity, and specificity of ai driven techniques in comparison to conventional security models. Zero trust architecture closes these gaps by validating every user, device, and access request through strict identity controls. this approach strengthens network security, reduces breach risks, and ensures consistent protection across applications and data. This practical book provides a detailed explanation of the zero trust security model. zero trust is a security paradigm shift that eliminates the concept of traditional perimeter based. This paper systematically compares the current mainstream cybersecurity models, thoroughly explores the advantages and limitations of the zero trust model, and provides an in depth review of its components and key technologies.

Premium Ai Image Enhancing Network Security With Zero Trust Architecture This article examines the combination of artificial intelligence (ai) with zero trust principles to improve the resilience of cyber security. this study demonstrates the enhanced accuracy, sensitivity, and specificity of ai driven techniques in comparison to conventional security models. Zero trust architecture closes these gaps by validating every user, device, and access request through strict identity controls. this approach strengthens network security, reduces breach risks, and ensures consistent protection across applications and data. This practical book provides a detailed explanation of the zero trust security model. zero trust is a security paradigm shift that eliminates the concept of traditional perimeter based. This paper systematically compares the current mainstream cybersecurity models, thoroughly explores the advantages and limitations of the zero trust model, and provides an in depth review of its components and key technologies.
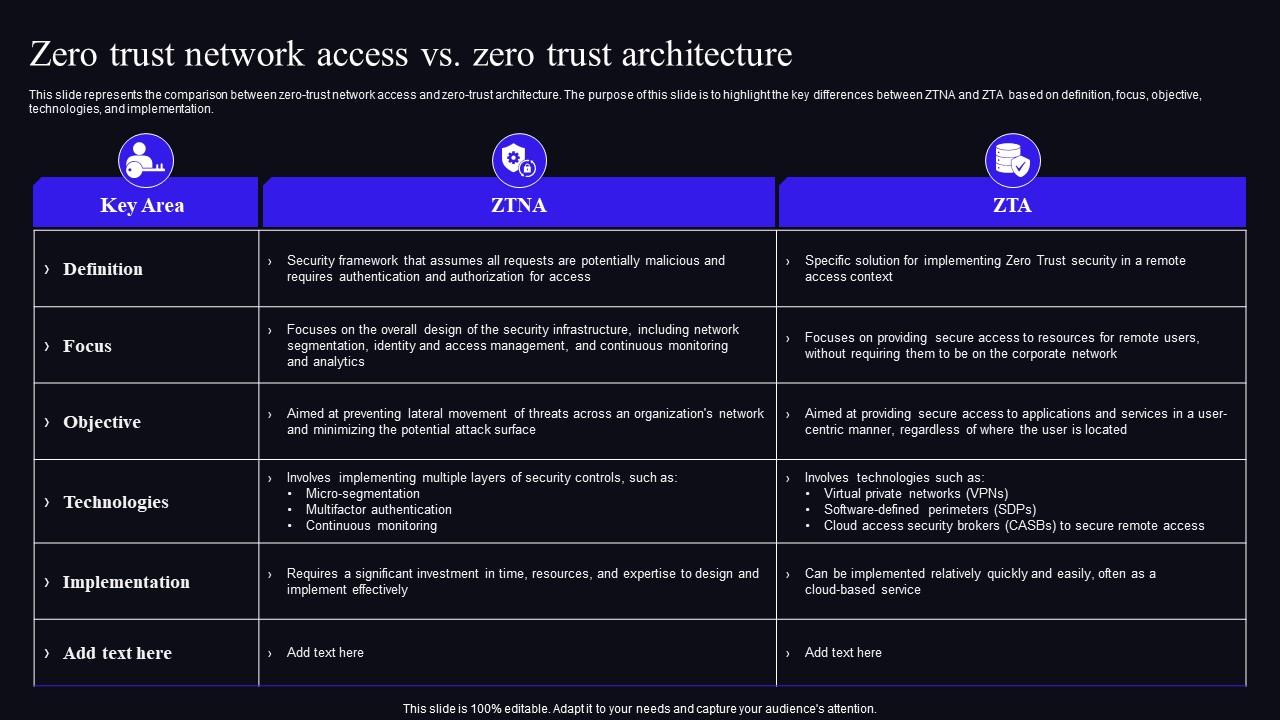
Zero Trust Network Access Vs Zero Trust Architecture Zero Trust This practical book provides a detailed explanation of the zero trust security model. zero trust is a security paradigm shift that eliminates the concept of traditional perimeter based. This paper systematically compares the current mainstream cybersecurity models, thoroughly explores the advantages and limitations of the zero trust model, and provides an in depth review of its components and key technologies.
Comments are closed.