Zero Trust And Automation A Security First Approach

Zero Trust And Automation A Security First Approach Automation is the key to making zero trust work at scale. without automated security controls, organizations would be overwhelmed by manual access approvals and threat responses. in this article, we’ll explore how zero trust and automation work together to enforce security policies, mitigate threats, and protect enterprise systems. Learn how devsecops integrates security into ci cd pipelines to enable secure cloud modernization. explore shift left security, automated testing, zero trust, and ai driven threat detection for resilient applications.

Cybersecurity What Is The Zero Trust Approach Ecs Blog Drawing on an extensive review of contemporary literature, the study analyses how ai techniques, such as machine learning, behavioural analytics, and automated threat response, can operationalise zero trust principles more effectively. This guide will walk you through the steps required to manage visibility, automation, and orchestration following the principles of a zero trust security framework. Zero trust is a cybersecurity strategy that shifts from a location centric to a more data centric approach for better security controls between users, systems, data and assets that may change over time (cisa, 2021). The study provides actionable insights into the implementation of zta, helping organizations prioritize security efforts to mitigate risks effectively and build a resilient digital infrastructure.

Zero To Zero Trust Automation Index Zero trust is a cybersecurity strategy that shifts from a location centric to a more data centric approach for better security controls between users, systems, data and assets that may change over time (cisa, 2021). The study provides actionable insights into the implementation of zta, helping organizations prioritize security efforts to mitigate risks effectively and build a resilient digital infrastructure. We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. Zero trust architecture (zta) represents a vital security approach that mandates trust for no entities, whether inside or outside organizational boundaries. ai integration to zta makes the framework more adaptable through its real time threat detection system and continuous authentication protocols, together with automated security responses. It examines the benefits, challenges, and future trends, providing a comprehensive guide to leveraging zero trust and ai for fortified cyber defenses. Zero trust automation workflows are built upon several non negotiable security tenets. these principles ensure that automation enhances security without introducing new vulnerabilities or compromising the stringent requirements of a zero trust model.
What Is The Zero Trust Security Model We propose a detailed and systematic taxonomy categorizing zta applications, implementation requirements, enabling technologies, and associated challenges. this taxonomy serves as a valuable reference for researchers and practitioners aiming to adopt or study zta in diverse contexts. Zero trust architecture (zta) represents a vital security approach that mandates trust for no entities, whether inside or outside organizational boundaries. ai integration to zta makes the framework more adaptable through its real time threat detection system and continuous authentication protocols, together with automated security responses. It examines the benefits, challenges, and future trends, providing a comprehensive guide to leveraging zero trust and ai for fortified cyber defenses. Zero trust automation workflows are built upon several non negotiable security tenets. these principles ensure that automation enhances security without introducing new vulnerabilities or compromising the stringent requirements of a zero trust model.
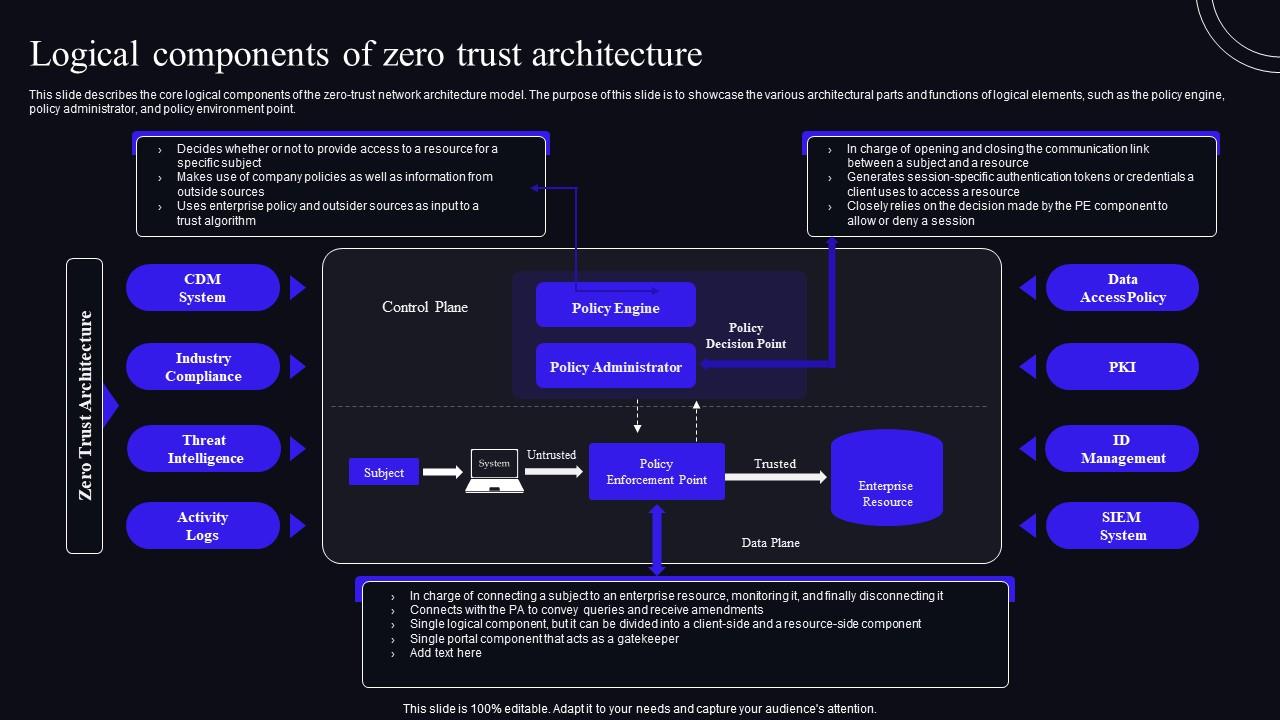
Logical Components Of Zero Trust Architecture Zero Trust Security Model It examines the benefits, challenges, and future trends, providing a comprehensive guide to leveraging zero trust and ai for fortified cyber defenses. Zero trust automation workflows are built upon several non negotiable security tenets. these principles ensure that automation enhances security without introducing new vulnerabilities or compromising the stringent requirements of a zero trust model.
Comments are closed.