Zero Day Vulnerability Explained

Zero Day Vulnerability Explained Microtime A zero day vulnerability is the underlying security flaw, present in code or hardware, that has not yet been discovered or addressed by the vendor. it exists in the wild, potentially for a prolonged period, until someone identifies and reports it. A zero day vulnerability is a software or hardware flaw that has been discovered and for which no patch exists.

Zero Day Exploit Alert Protect Your Systems Now A zero day (also known as a 0 day) is a vulnerability or security hole in a computer system unknown to its developers or anyone capable of mitigating it. [1] until the vulnerability is remedied, threat actors can exploit it in a zero day exploit, or zero day attack. [2][3]. A zero day vulnerability is a software flaw that the vendor does not yet know about or has not yet patched, giving defenders zero days to prepare before attackers can exploit it. What is a zero day vulnerability? a zero day vulnerability is a previously unknown flaw in code or system design that can be leveraged by attackers to gain unauthorized access, escalate privileges, execute arbitrary code, or disrupt normal operations. A zero day vulnerability refers to an undisclosed flaw in software or hardware that is actively exploited by attackers before a patch or fix is available. unlike typical vulnerabilities that vendors can address through updates, zero days are exploited in secrecy, leaving systems wide open to attack.
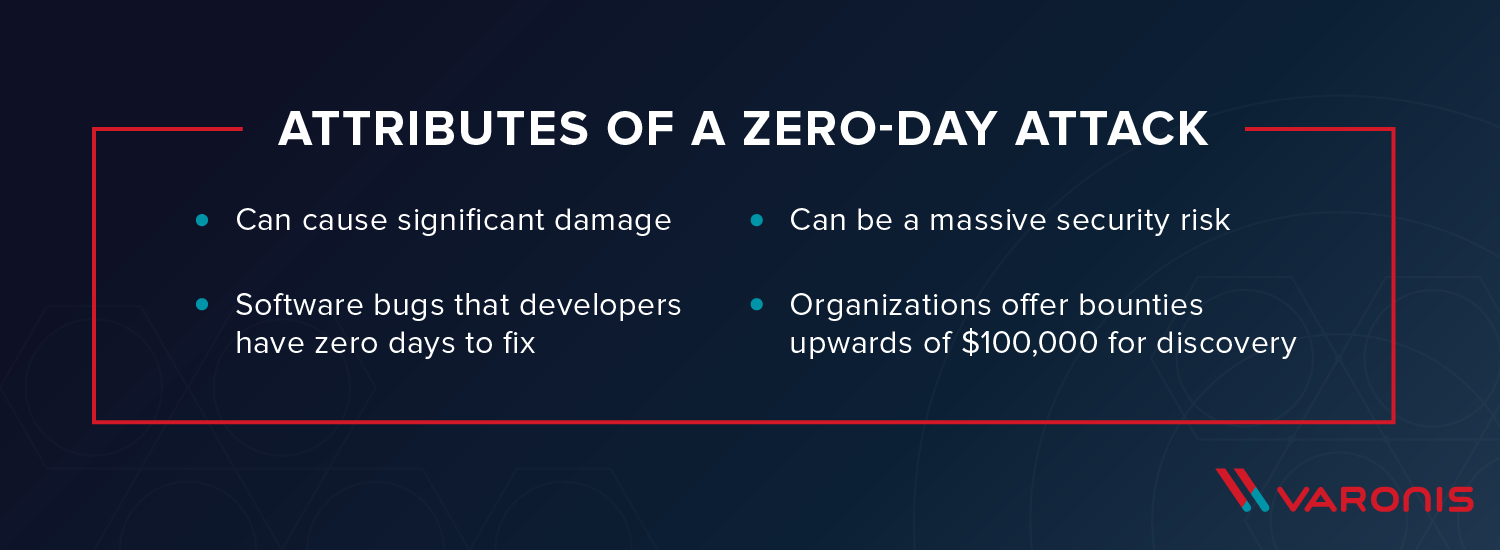
Zero Day Vulnerability Explained What is a zero day vulnerability? a zero day vulnerability is a previously unknown flaw in code or system design that can be leveraged by attackers to gain unauthorized access, escalate privileges, execute arbitrary code, or disrupt normal operations. A zero day vulnerability refers to an undisclosed flaw in software or hardware that is actively exploited by attackers before a patch or fix is available. unlike typical vulnerabilities that vendors can address through updates, zero days are exploited in secrecy, leaving systems wide open to attack. What is a zero day vulnerability? a zero day vulnerability is a security flaw in a piece of software, firmware, or hardware that isn’t known to the vendor or the general public. the developer hasn't created a patch or update to fix it yet, so attackers can exploit it without warning. A zero day vulnerability is a hidden flaw or weakness in software that the developer or vendor doesn’t yet know about. because they don’t know it exists, there is no patch or fix available —and that’s what makes it so dangerous. Learn what zero day vulnerabilities are, why they’re dangerous, and how exploits are developed. discover responsible disclosure practices and famous attacks. Understanding zero day risk organizations face zero day risk when new vulnerabilities are actively exploited in the wild before security vendors can issue patches. for example, a zero day exploit might target a popular operating system or web browser, allowing attackers to gain unauthorized access or install malware. mitigating this risk involves advanced threat detection systems, behavioral.

Zero Day Vulnerability Explained What is a zero day vulnerability? a zero day vulnerability is a security flaw in a piece of software, firmware, or hardware that isn’t known to the vendor or the general public. the developer hasn't created a patch or update to fix it yet, so attackers can exploit it without warning. A zero day vulnerability is a hidden flaw or weakness in software that the developer or vendor doesn’t yet know about. because they don’t know it exists, there is no patch or fix available —and that’s what makes it so dangerous. Learn what zero day vulnerabilities are, why they’re dangerous, and how exploits are developed. discover responsible disclosure practices and famous attacks. Understanding zero day risk organizations face zero day risk when new vulnerabilities are actively exploited in the wild before security vendors can issue patches. for example, a zero day exploit might target a popular operating system or web browser, allowing attackers to gain unauthorized access or install malware. mitigating this risk involves advanced threat detection systems, behavioral.
What Is Zero Day Vulnerability A Threat You Need To Be Aware Of Learn what zero day vulnerabilities are, why they’re dangerous, and how exploits are developed. discover responsible disclosure practices and famous attacks. Understanding zero day risk organizations face zero day risk when new vulnerabilities are actively exploited in the wild before security vendors can issue patches. for example, a zero day exploit might target a popular operating system or web browser, allowing attackers to gain unauthorized access or install malware. mitigating this risk involves advanced threat detection systems, behavioral.
Comments are closed.