Your Docker Containers Data Is Not Safe

Persisting Container Data Docker Docs While docker secrets generally provide a secure way to manage sensitive data in docker environments, this approach is not recommended for kubernetes, where secrets are stored in plaintext by default. Learn 14 docker best practices to ensure that your deployments are robust, resilient, and ready to meet the challenges of modern security threats.
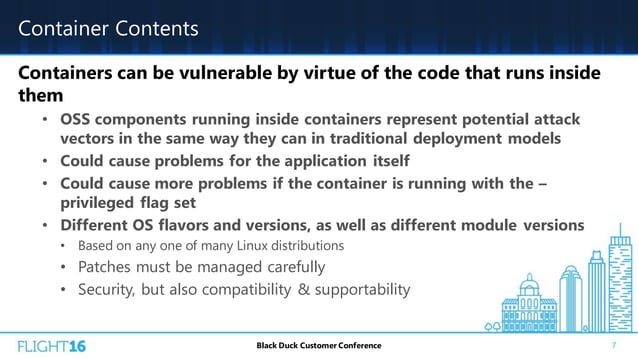
Securing Docker Containers Ppt Running containers as root, exposing ports, ignoring updates: these docker security mistakes are common and avoidable. here's how to fix them. Docker security best practices ensure the safe running of container systems. discover how to avoid the most common docker container vulnerabilities here. Docker containers are lightweight, portable, and awesome for deploying apps. but let’s be real—security is a big deal, and encryption is a key piece of keeping your containers safe. whether it’s sensitive data, api keys, or user info, you don’t want it floating around unencrypted. Understand the basics of docker security, and learn about key risks facing your containers and simple best practices you can use today to improve container security.

How To Secure Your Docker Containers With Zero Trust Networking Docker containers are lightweight, portable, and awesome for deploying apps. but let’s be real—security is a big deal, and encryption is a key piece of keeping your containers safe. whether it’s sensitive data, api keys, or user info, you don’t want it floating around unencrypted. Understand the basics of docker security, and learn about key risks facing your containers and simple best practices you can use today to improve container security. Exposing the daemon api over http without tls is not permitted, and such a configuration causes the daemon to fail early on startup, see unauthenticated tcp connections. From container runtime vulnerabilities to cves that affect critical gpu workloads, this article breaks down nine of the most vital and commonly overlooked docker container vulnerabilities. This document serves as a comprehensive guide to docker container security, detailing the risks associated with docker, common misconfigurations, and best practices for securing containerized environments. Container security involves implementing a robust set of practices and tools to protect the entire container lifecycle, from the underlying infrastructure to the applications running within them. it focuses on ensuring the integrity, confidentiality, and availability of containerized environments.
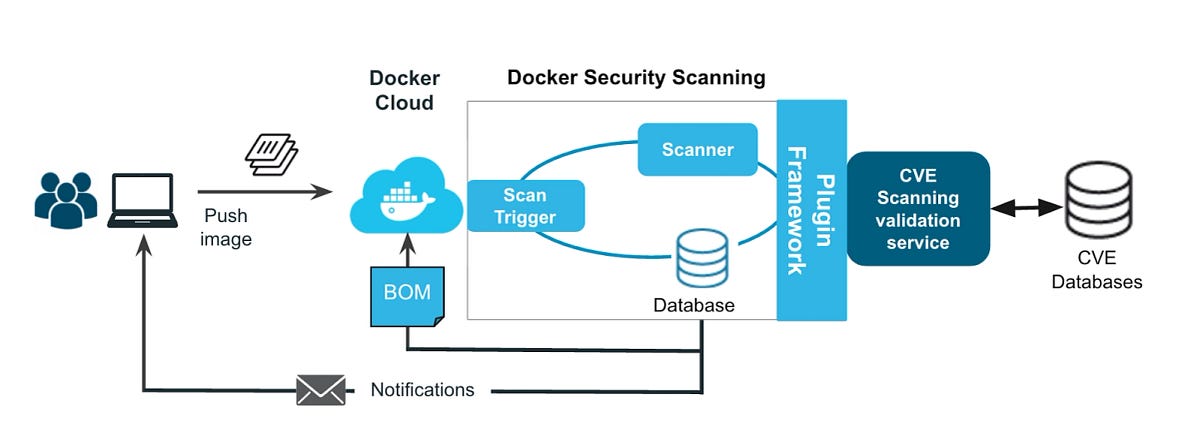
Docker Security Keeping Your Containers Safe And Sound By Paritosh Exposing the daemon api over http without tls is not permitted, and such a configuration causes the daemon to fail early on startup, see unauthenticated tcp connections. From container runtime vulnerabilities to cves that affect critical gpu workloads, this article breaks down nine of the most vital and commonly overlooked docker container vulnerabilities. This document serves as a comprehensive guide to docker container security, detailing the risks associated with docker, common misconfigurations, and best practices for securing containerized environments. Container security involves implementing a robust set of practices and tools to protect the entire container lifecycle, from the underlying infrastructure to the applications running within them. it focuses on ensuring the integrity, confidentiality, and availability of containerized environments.

How Secure Are Docker Containers Ppt This document serves as a comprehensive guide to docker container security, detailing the risks associated with docker, common misconfigurations, and best practices for securing containerized environments. Container security involves implementing a robust set of practices and tools to protect the entire container lifecycle, from the underlying infrastructure to the applications running within them. it focuses on ensuring the integrity, confidentiality, and availability of containerized environments.
Comments are closed.