Xwiki Remote Code Execution Vulnerability
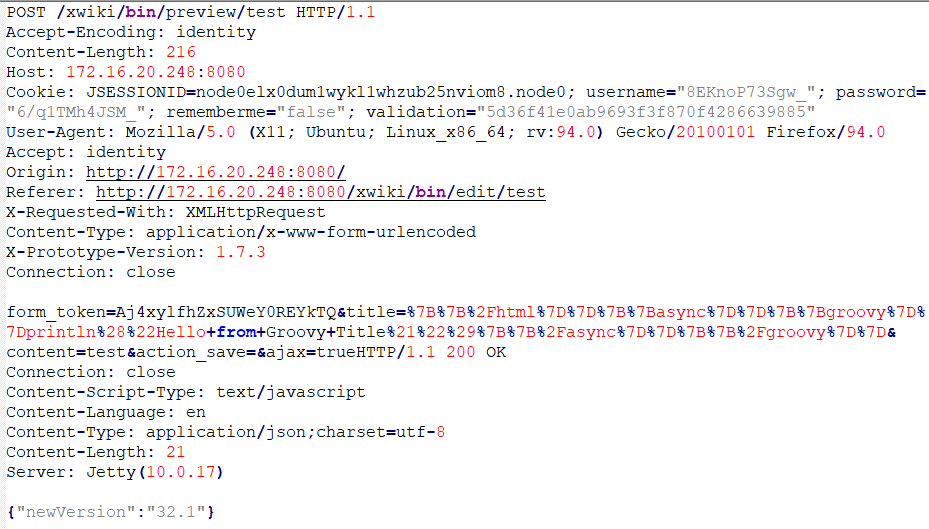
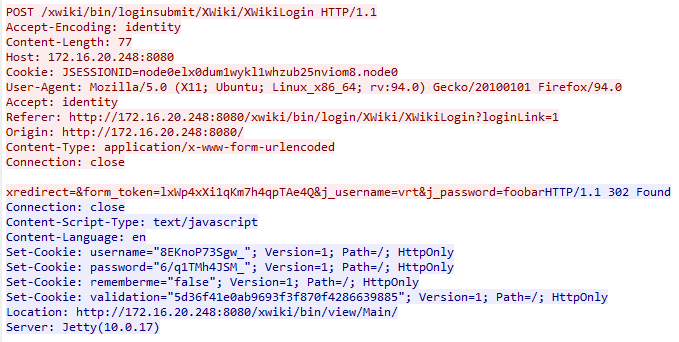
Xwiki Remote Code Execution Vulnerability A newly discovered critical vulnerability in the xwiki platform, tracked as cve 2025 24893, allows unauthenticated remote code execution (rce) through the solrsearch macro. Cve 2025 24893 is a critical unauthenticated remote code execution (rce) vulnerability in xwiki, a popular open source enterprise wiki platform. the flaw resides in how the solrsearch macro improperly handles groovy expressions inside search queries.
Xwiki Remote Code Execution Vulnerability Patches the vulnerability has been patched in xwiki 17.4.8 and 17.10.1 by requiring programming right to access the affected scripting api. Vulnerability details : cve 2026 33229 xwiki platform affected by remote code execution with script right through unprotected velocity scripting api. Cve 2026 33229 xwiki vulnerable to remote code execution with script right through unprotected velocity scripting api: an improperly protected scripting api allows any user with script right to bypass the sandboxing of the velocity scripting api and …. Xwiki platform is a generic wiki platform offering runtime services for applications built on top of it. prior to 17.4.8 and 17.10.1, an improperly protected scripting api allows any user with script right to bypass the sandboxing of the velocity scripting api and execute, e.g., arbitrary python scripts, allowing full ….
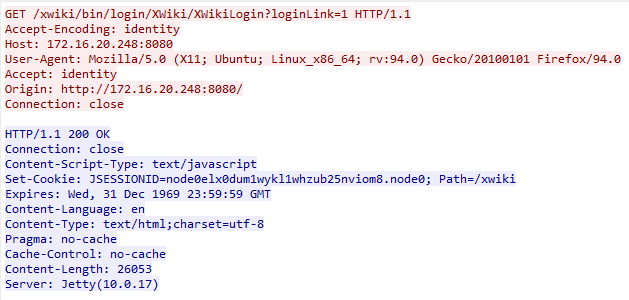
Xwiki Remote Code Execution Vulnerability Cve 2026 33229 xwiki vulnerable to remote code execution with script right through unprotected velocity scripting api: an improperly protected scripting api allows any user with script right to bypass the sandboxing of the velocity scripting api and …. Xwiki platform is a generic wiki platform offering runtime services for applications built on top of it. prior to 17.4.8 and 17.10.1, an improperly protected scripting api allows any user with script right to bypass the sandboxing of the velocity scripting api and execute, e.g., arbitrary python scripts, allowing full …. Any guest can perform arbitrary remote code execution through a request to solrsearch. this impacts the confidentiality, integrity, and availability of the whole xwiki installation. this vulnerability has been patched in xwiki 15.10.11, 16.4.1, and. A critical remote code execution vulnerability affecting xwiki’s solrsearch component has become the target of widespread exploitation attempts, prompting cybersecurity authorities to add it to their watchlist. What makes this issue especially severe is that any guest user (even without logging in) can achieve remote code execution (rce) on the xwiki server, simply by crafting a malicious request to the solrsearch endpoint. The vulnerability, carrying a devastating cvss score of 9.8 out of 10, allows completely unauthenticated attackers to execute arbitrary groovy code on xwiki servers through a single malformed http request.
Comments are closed.