Xwiki Remote Code Execution Flaw Actively Weaponized For Coinmining

Xwiki Remote Code Execution Flaw Actively Weaponized For Coinmining A critical security vulnerability in xwiki collaboration software is being actively exploited by threat actors to deploy cryptocurrency mining malware on vulnerable systems. the flaw, tracked as cve 2025 24893, represents a serious threat to organizations running unpatched xwiki installations. A critical security vulnerability in xwiki collaboration software is being actively exploited by threat actors to deploy cryptocurrency mining malware.
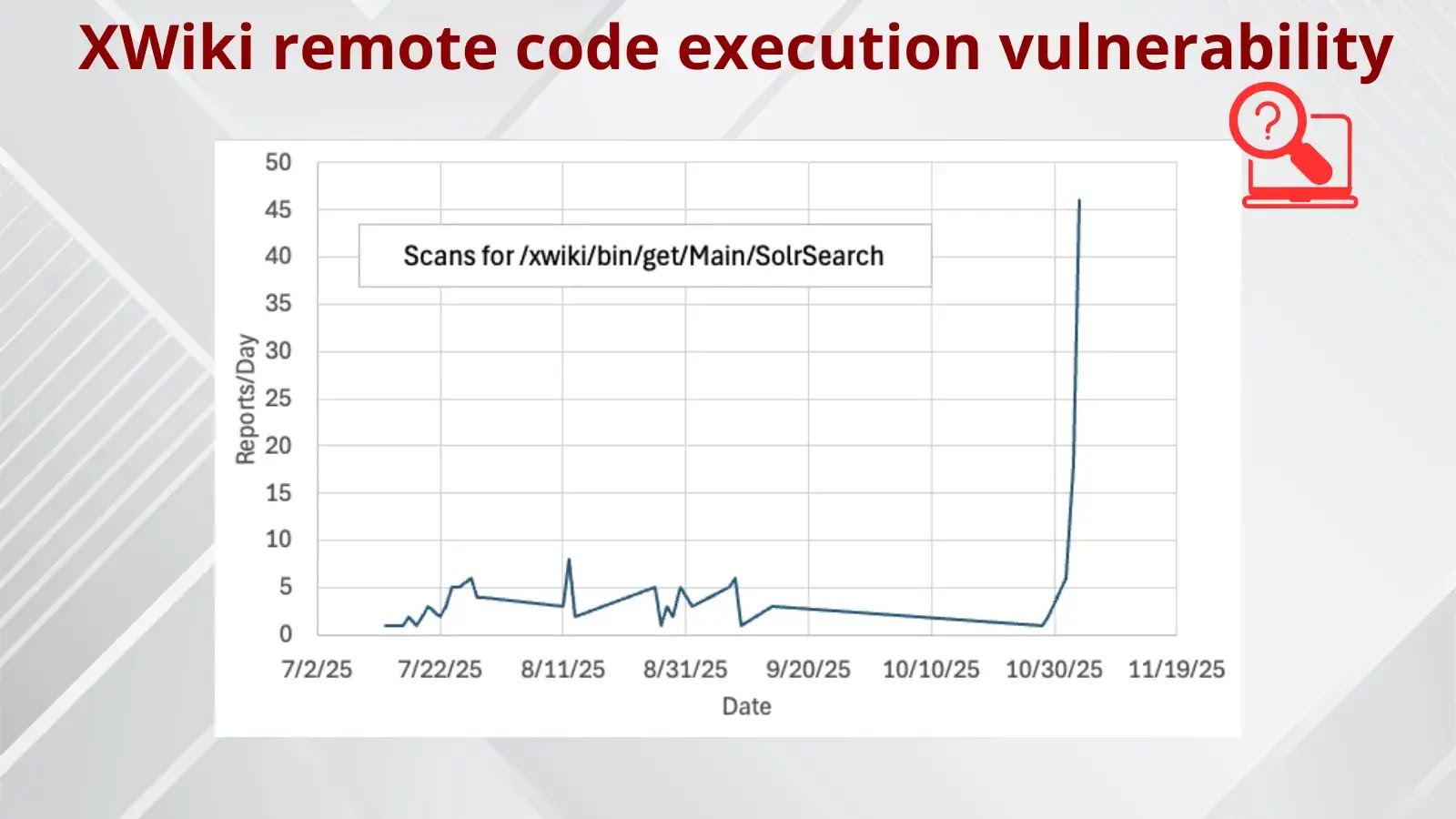
Hackers Actively Scanning Internet To Exploit Xwiki Remote Code Execution A critical remote code execution (rce) flaw in xwiki, a popular open source wiki platform, was exploited in the wild to deploy cryptocurrency mining malware on compromised servers. Cve 2025 24893 is an unauthenticated, remote template injection vulnerability in xwiki that is being actively exploited in the wild. it does not appear in cisa kev. An unauthenticated remote code execution vulnerability in xwiki is being actively exploited in the wild to deliver cryptocurrency mining malware, according to threat intelligence findings from vulncheck. Executive summary: a critical remote code execution vulnerability in the xwiki platform, tracked as cve 2025 24893, was observed being exploited to deploy cryptocurrency miners.
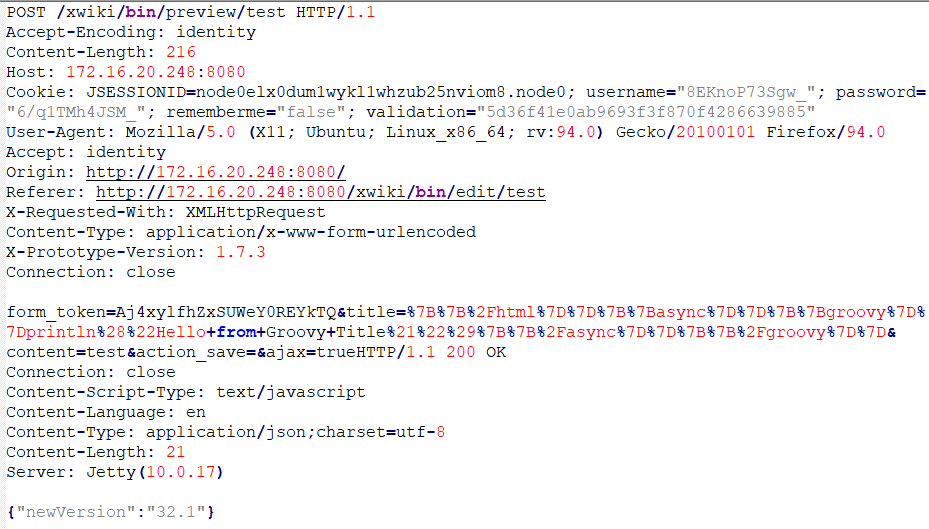
Xwiki Remote Code Execution Vulnerability An unauthenticated remote code execution vulnerability in xwiki is being actively exploited in the wild to deliver cryptocurrency mining malware, according to threat intelligence findings from vulncheck. Executive summary: a critical remote code execution vulnerability in the xwiki platform, tracked as cve 2025 24893, was observed being exploited to deploy cryptocurrency miners. In late october, vulncheck warned that a threat actor was exploiting cve 2025 24893 as part of a cryptocurrency mining operation, and the us cybersecurity agency cisa added the bug to its known exploited vulnerabilities (kev) catalog two days later. The vulnerability, carrying a devastating cvss score of 9.8 out of 10, allows completely unauthenticated attackers to execute arbitrary groovy code on xwiki servers through a single malformed http request. A newly discovered critical vulnerability in the xwiki platform, tracked as cve 2025 24893, allows unauthenticated remote code execution (rce) through the solrsearch macro. An rce vulnerability in xwiki was found allowing unauthenticated attackers to execute arbitrary groovy code remotely without authentication or prior access.
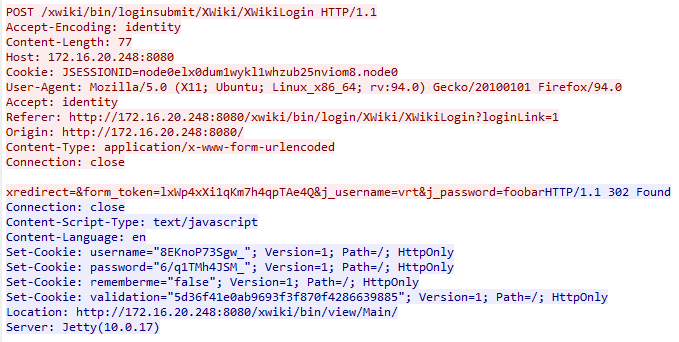
Xwiki Remote Code Execution Vulnerability In late october, vulncheck warned that a threat actor was exploiting cve 2025 24893 as part of a cryptocurrency mining operation, and the us cybersecurity agency cisa added the bug to its known exploited vulnerabilities (kev) catalog two days later. The vulnerability, carrying a devastating cvss score of 9.8 out of 10, allows completely unauthenticated attackers to execute arbitrary groovy code on xwiki servers through a single malformed http request. A newly discovered critical vulnerability in the xwiki platform, tracked as cve 2025 24893, allows unauthenticated remote code execution (rce) through the solrsearch macro. An rce vulnerability in xwiki was found allowing unauthenticated attackers to execute arbitrary groovy code remotely without authentication or prior access.
Comments are closed.