Xss Vs Sql Injection Injection Attacks Explained Nextdoorsec
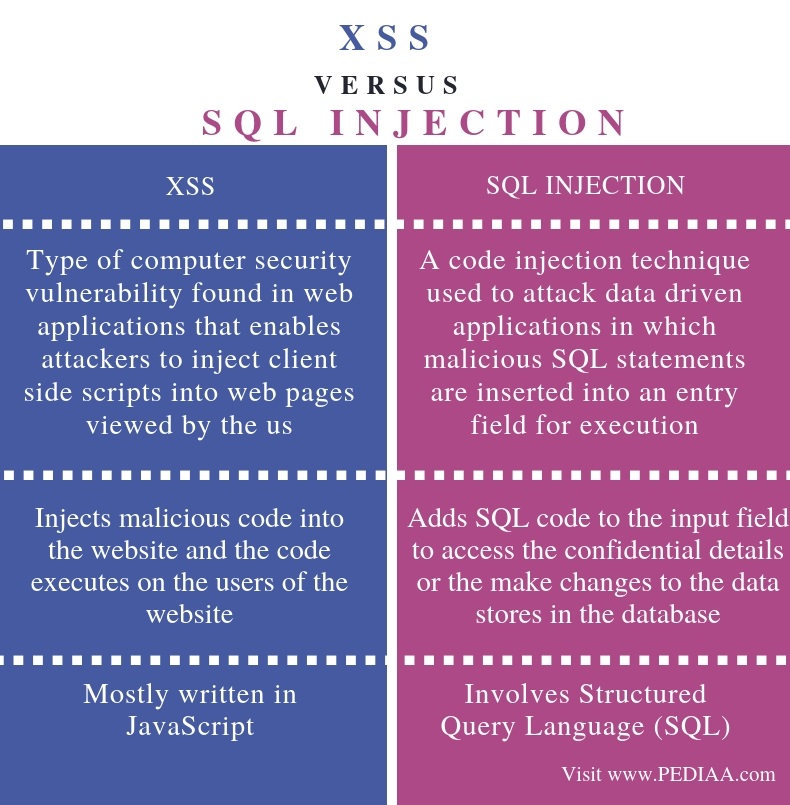
What Is The Difference Between Xss And Sql Injection Pediaa Com While xss and sql injection are distinct attack methods, one vulnerability can indirectly lead to another. for example, if an xss attack gains access to a user’s session token and the application does not properly handle it, it can potentially be exploited in a sql injection attack. Different types of vulnerabilities can be found in any software or system if proper security measures were not taken so we will compare the two most common vulnerabilities which are xss and sql injection to understand the problem and their mitigation.
Xss Vs Sql Injection Injection Attacks Explained Nextdoorsec Learn about cross site scripting (xss) and sql injection attacks, two of the most common web vulnerabilities, and discover best practices for preventing them. Learn the attack anatomy and differences between two of the most popular and common attack vectors sql injection and cross site scripting attack. Confused about xss vs. sql injection? 🧠 dive into our expert guide explaining their core differences, impacts, and prevention strategies. secure your web apps now!. While both xss and sql injection are injection attacks that target web applications, they differ significantly in their attack vectors, targets, and consequences.
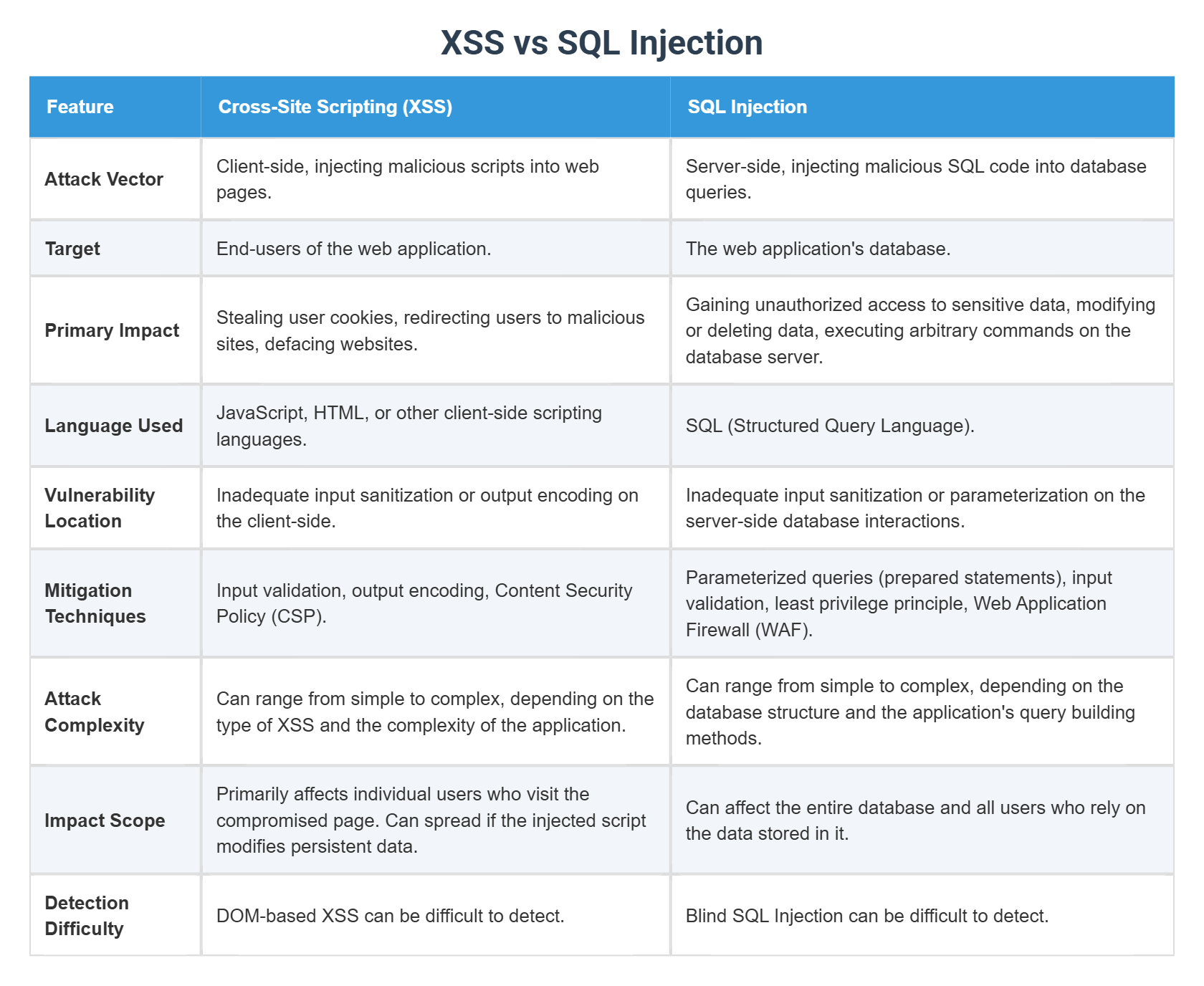
Xss Vs Sql Injection Confused about xss vs. sql injection? 🧠 dive into our expert guide explaining their core differences, impacts, and prevention strategies. secure your web apps now!. While both xss and sql injection are injection attacks that target web applications, they differ significantly in their attack vectors, targets, and consequences. While sql injection targets the application's database layer, xss attacks exploit the trust between the application and its users. both vulnerabilities can lead to severe consequences, including unauthorized access, data breaches, and financial losses. This article will explore the key differences between xss and sql injection, covering how they work, their impacts, and how they can be mitigated to protect web application s from malicious exploitation. It explains what cross site scripting (xss) is, why it’s important, and how it differs from sql injection, while also touching on how these attacks work. the post details methods for preventing xss and sql injection, best practices, and available tools. In this article, we thoroughly examined cross site scripting (xss) and sql injection, two of the most dangerous web application vulnerabilities. we outlined their exploitation workflows and provided several attack examples with url samples, code snippets, and flow diagrams.

Xss Sql Injection English Vocabulary Security Internet Website While sql injection targets the application's database layer, xss attacks exploit the trust between the application and its users. both vulnerabilities can lead to severe consequences, including unauthorized access, data breaches, and financial losses. This article will explore the key differences between xss and sql injection, covering how they work, their impacts, and how they can be mitigated to protect web application s from malicious exploitation. It explains what cross site scripting (xss) is, why it’s important, and how it differs from sql injection, while also touching on how these attacks work. the post details methods for preventing xss and sql injection, best practices, and available tools. In this article, we thoroughly examined cross site scripting (xss) and sql injection, two of the most dangerous web application vulnerabilities. we outlined their exploitation workflows and provided several attack examples with url samples, code snippets, and flow diagrams.
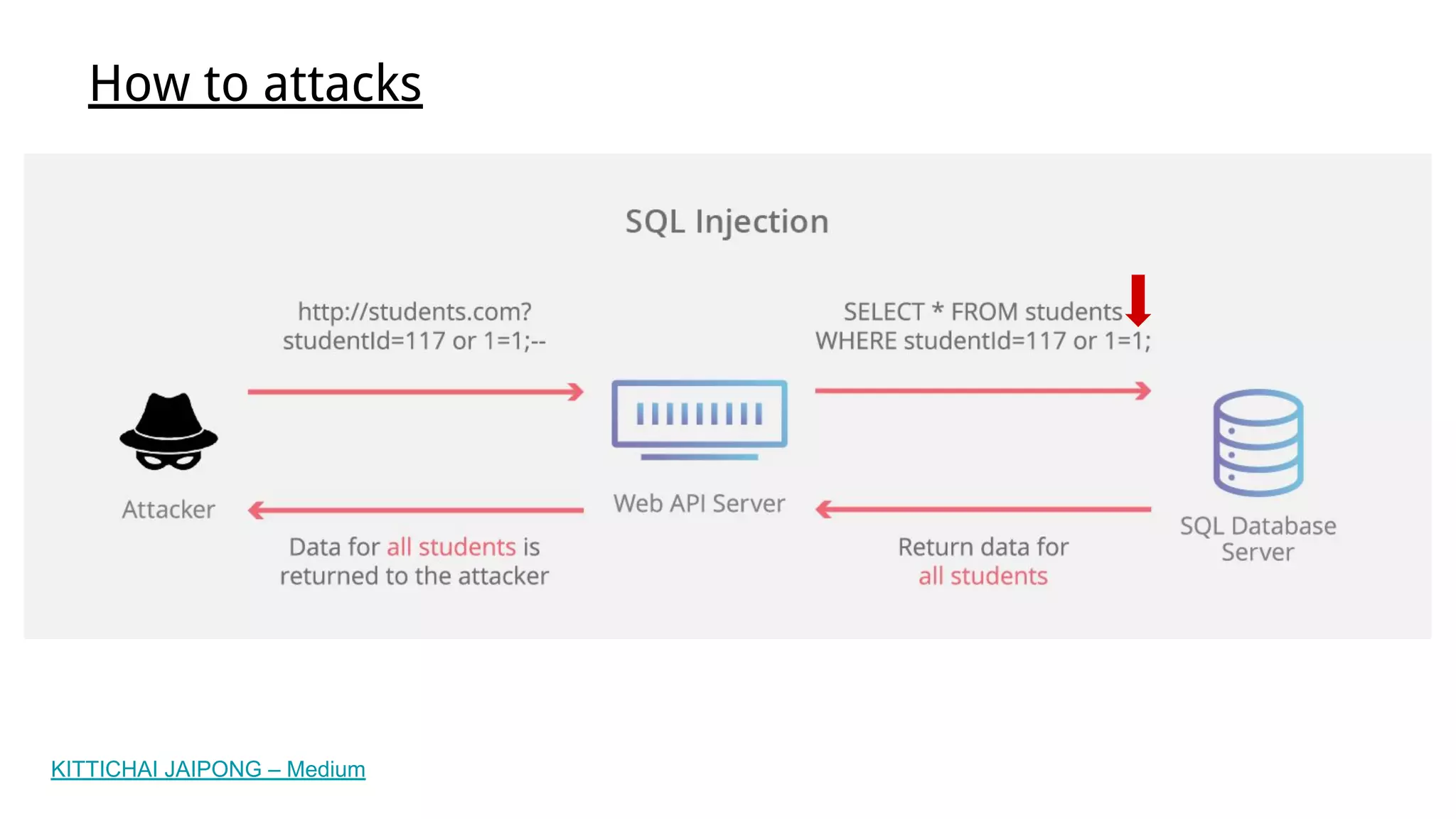
Xss And Sql Injection Pdf It explains what cross site scripting (xss) is, why it’s important, and how it differs from sql injection, while also touching on how these attacks work. the post details methods for preventing xss and sql injection, best practices, and available tools. In this article, we thoroughly examined cross site scripting (xss) and sql injection, two of the most dangerous web application vulnerabilities. we outlined their exploitation workflows and provided several attack examples with url samples, code snippets, and flow diagrams.
Comments are closed.