Write Your First Exploit Educational
Homepage One Exploit Exercises Join my new ctf platform: go.lowlevel.tv c630ttqlyhi in this video we explore the dangers of buffer overflows and learn how to write an exploit for the vulnerability ourselves. Exploit.education provides a variety of resources that can be used to learn about vulnerability analysis, exploit development, software debugging, binary analysis, and general cyber security issues.

Talk Writing My First Exploit Speaker Deck In this repository, you'll find detailed explanations, strategies, likewise code samples for solving various levels of security challenges. the repository is organized in ascending order of difficulty, starting from the basic concepts & progressing to more advanced scenarios. Writing custom exploits is a powerful skill that sets ethical hackers apart in the cybersecurity landscape. by following this safe beginner guide, you’ve learned the essentials of exploit development—from legal considerations and lab setup to hands on coding and best practices. At this point, you should be ready to try out your exploit. after running your exploit script, your meterpreter handler should tell you that you have an open meterpreter session. As a general rule of thumb, when you want to attack anything, the first step is to understand how it works. an assembly language. this is a tricky one that newcomers sometimes take the wrong path on. you don't need to be able to program in assembly, and you shouldn't follow tutorials for programmers about writing assembly.
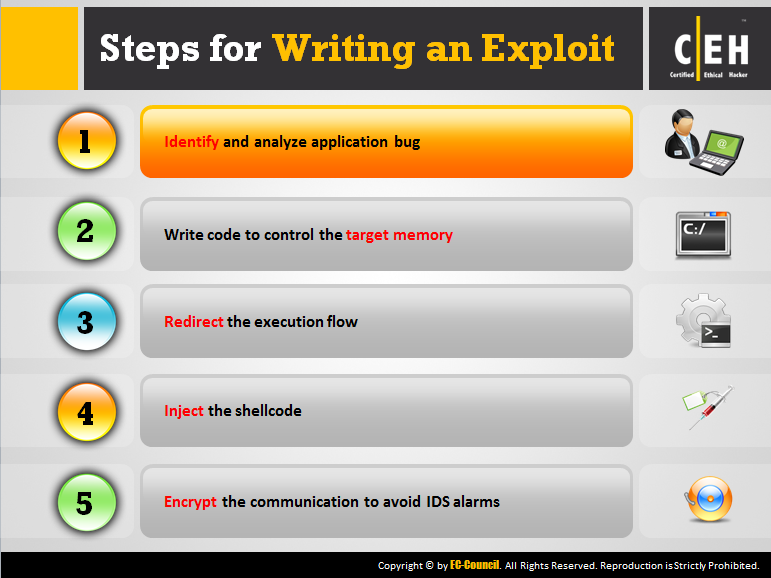
Exploit Writing Ec Council Store At this point, you should be ready to try out your exploit. after running your exploit script, your meterpreter handler should tell you that you have an open meterpreter session. As a general rule of thumb, when you want to attack anything, the first step is to understand how it works. an assembly language. this is a tricky one that newcomers sometimes take the wrong path on. you don't need to be able to program in assembly, and you shouldn't follow tutorials for programmers about writing assembly. The file will first contain a basic command that we will use to verify that the exploit has worked. then we are going to read the contents of a file located on the vulnerable machine. The primary goal of this exercise is to make you familiar to overwrite function pointer with your own function pointer and therefore redirecting the program flow to achieve code execution within the binary program. In this repository, you'll find detailed explanations, strategies, likewise code samples for solving various levels of security challenges. the repository is organized in ascending order of difficulty, starting from the basic concepts & progressing to more advanced scenarios. Learn exploit development fundamentals, including memory corruption, shellcode, debugging, and vulnerability research techniques.
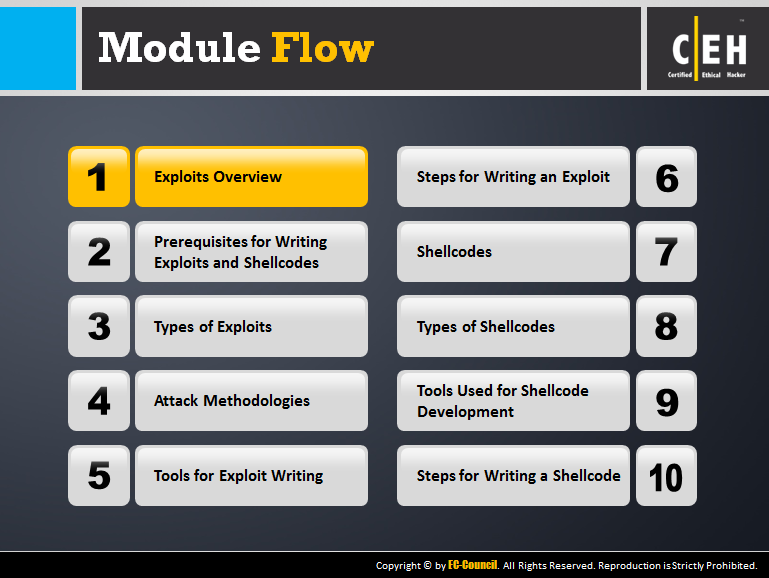
Exploit Writing Ec Council Store The file will first contain a basic command that we will use to verify that the exploit has worked. then we are going to read the contents of a file located on the vulnerable machine. The primary goal of this exercise is to make you familiar to overwrite function pointer with your own function pointer and therefore redirecting the program flow to achieve code execution within the binary program. In this repository, you'll find detailed explanations, strategies, likewise code samples for solving various levels of security challenges. the repository is organized in ascending order of difficulty, starting from the basic concepts & progressing to more advanced scenarios. Learn exploit development fundamentals, including memory corruption, shellcode, debugging, and vulnerability research techniques.
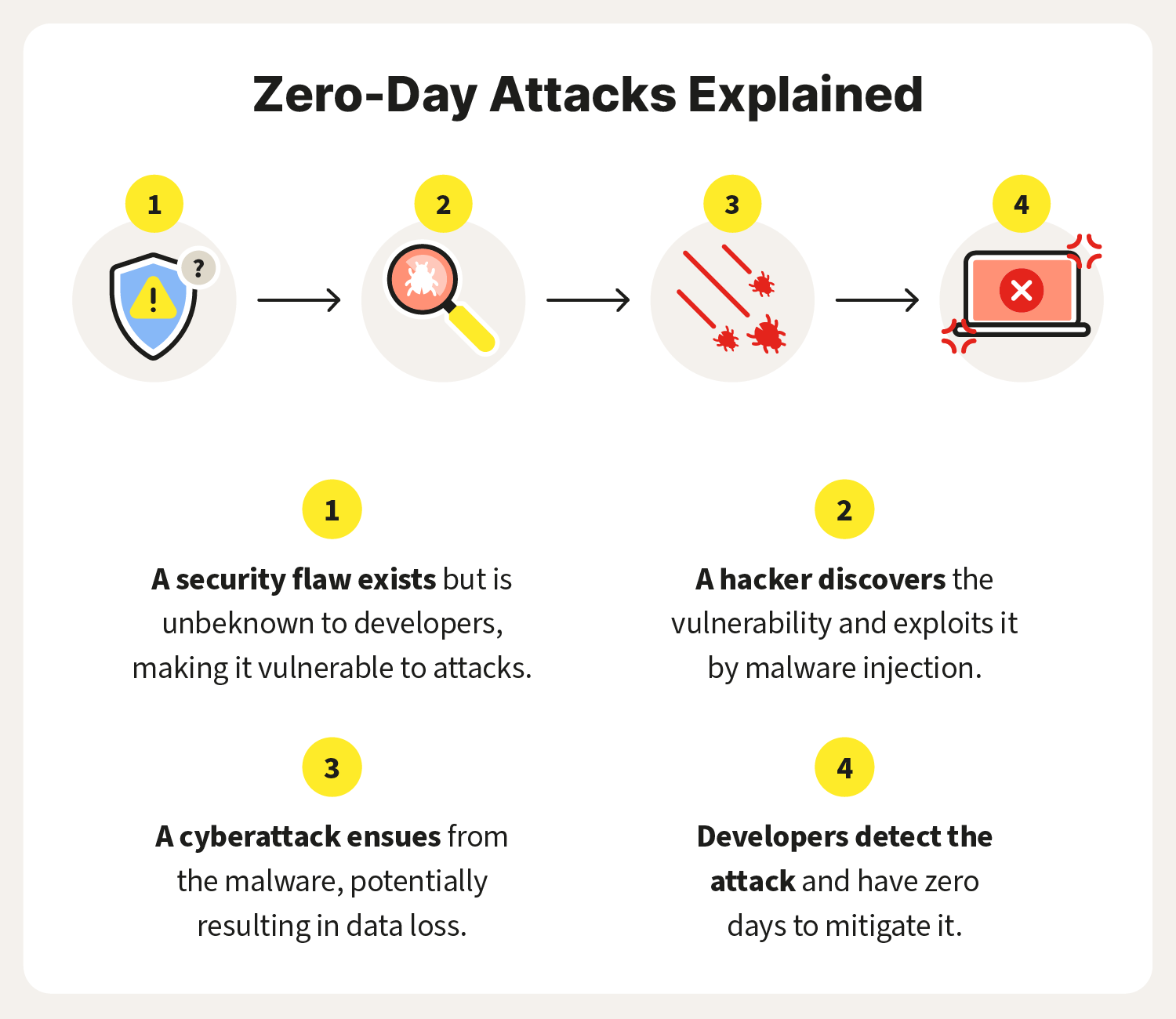
Exploit Definition In this repository, you'll find detailed explanations, strategies, likewise code samples for solving various levels of security challenges. the repository is organized in ascending order of difficulty, starting from the basic concepts & progressing to more advanced scenarios. Learn exploit development fundamentals, including memory corruption, shellcode, debugging, and vulnerability research techniques.

Julian Totzek Hallhuber Let S Write An Exploit Using Ai
Comments are closed.