Wpa Decryption Using Wireshark
Ppt Wireless Security Using Wep Wpa And Wpa2 Powerpoint Capturing the 4 way handshake and knowing the network password is not enough to decrypt packets; you must obtain the pmk from either the client or access point (typically by enabling logging in wpa supplicant or hostapd with the d k flags) and use this as the decryption key in wireshark. It is required to provide the wi fi password in the wireshark sniffer tool to decrypt the wep and wpa wpa2 in pre shared (or personal) mode. wpa wpa2 enterprise mode decryption is not yet supported.

Decrypt Wpa2 Psk Using Wireshark Mrn Cciew Follow the steps below to capture the client's pmk. 1. before the client connects to the ap, start packet sniffing on the correct radio interface. 2. enable logging on both the client. This latter case is complicated by the fact that most wi fi traffic is encrypted at layer two using wpa2. fortunately, with a few pieces of information, we can decrypt wpa2 traffic directly in wireshark using a built in decoder. In this post we will see how to decrypt wpa2 psk traffic using wireshark. this is useful when you study (my case for cwsp studies) different security protocols used in wireless.here is the basic topology for this post. Wireshark, a leading network protocol analyzer, offers capabilities to decrypting wpa traffic, enabling deep inspection and analysis of wireless communications. this article serves as a comprehensive guide, detailing the steps and considerations involved in decrypting wpa traffic using wireshark.

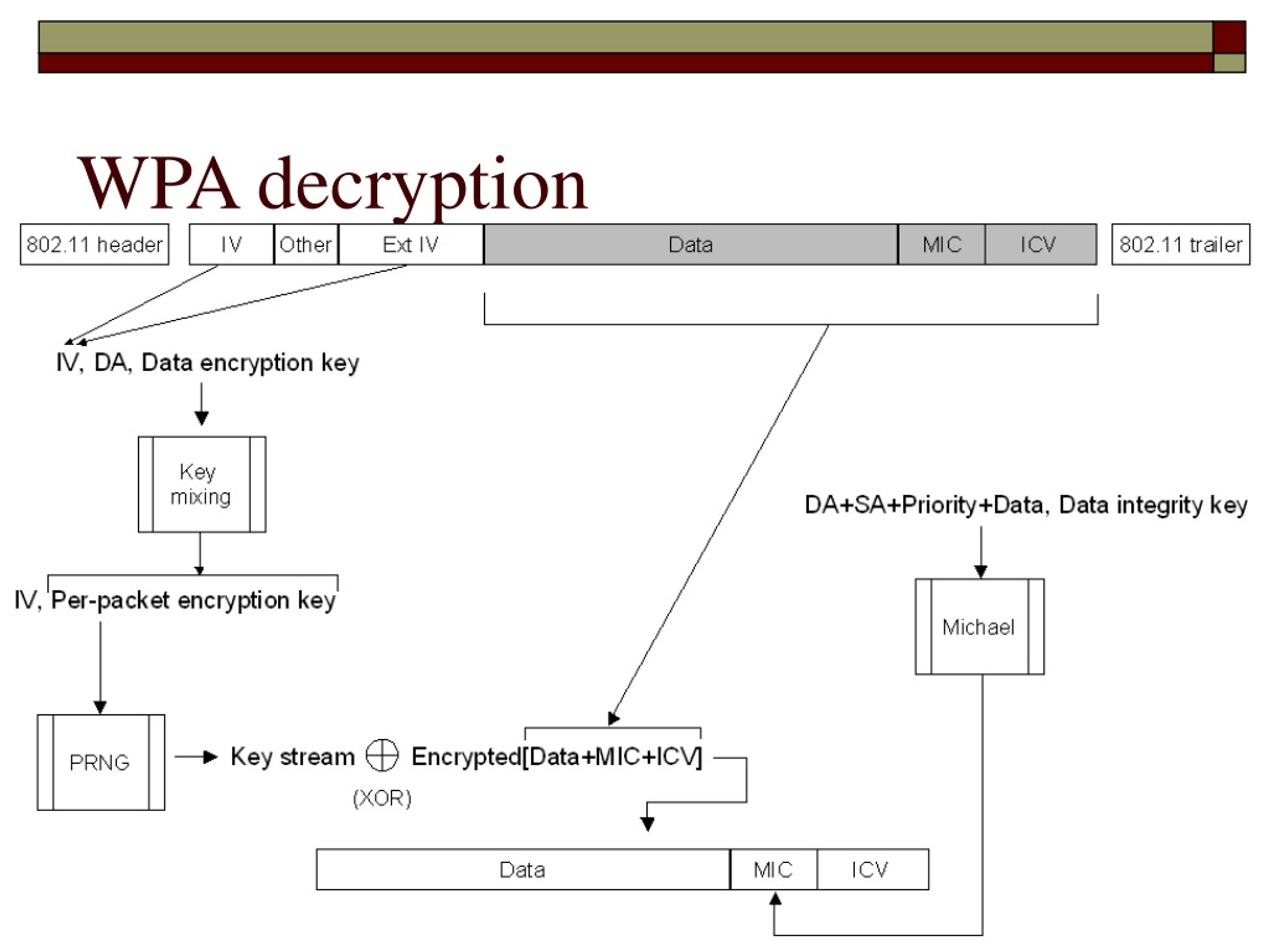
Decrypt Wpa2 Psk Using Wireshark Mrn Cciew In this post we will see how to decrypt wpa2 psk traffic using wireshark. this is useful when you study (my case for cwsp studies) different security protocols used in wireless.here is the basic topology for this post. Wireshark, a leading network protocol analyzer, offers capabilities to decrypting wpa traffic, enabling deep inspection and analysis of wireless communications. this article serves as a comprehensive guide, detailing the steps and considerations involved in decrypting wpa traffic using wireshark. This project demonstrates the process of capturing, decrypting, and analyzing encrypted wi fi traffic using wireshark. the goal was to exploit a wpa2 secured wireless network to gain visibility into otherwise encrypted https traffic by leveraging both wpa2 handshake cracking and tls session key extraction. Decrypt captured wpa and wpa2 traffic using airdecap ng and wireshark with a recovered psk on kali linux to analyse plaintext client communications. Wpa and wpa2 use keys derived from an eapol handshake, which occurs when a machine joins a wi fi network, to encrypt traffic. unless all four handshake packets are present for the session you’re trying to decrypt, wireshark won’t be able to decrypt the traffic. If we have “tk (temporal key)” then we can select tk option from drop down and decrypt wpa wpa2 frames. in our example, we have got tk as “a6ece97a4d51b496b001bfb1ad029e01” from any data packet for wpa2 psk security decryption.
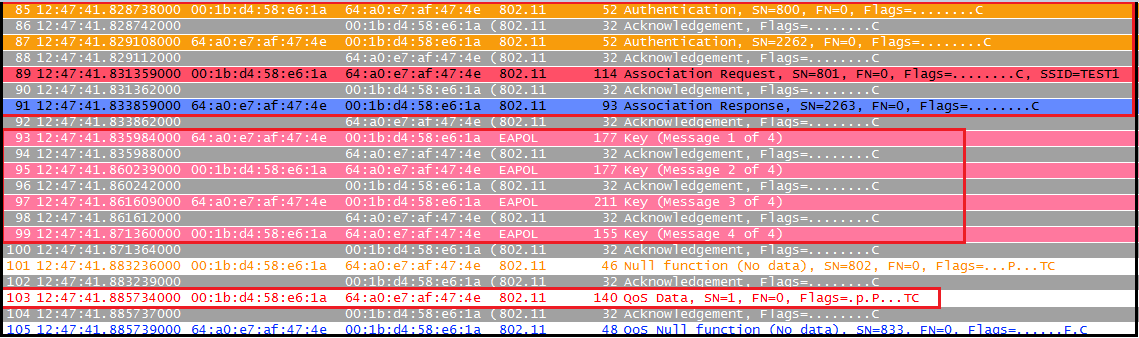
Decrypt Wpa2 Psk Using Wireshark Mrn Cciew This project demonstrates the process of capturing, decrypting, and analyzing encrypted wi fi traffic using wireshark. the goal was to exploit a wpa2 secured wireless network to gain visibility into otherwise encrypted https traffic by leveraging both wpa2 handshake cracking and tls session key extraction. Decrypt captured wpa and wpa2 traffic using airdecap ng and wireshark with a recovered psk on kali linux to analyse plaintext client communications. Wpa and wpa2 use keys derived from an eapol handshake, which occurs when a machine joins a wi fi network, to encrypt traffic. unless all four handshake packets are present for the session you’re trying to decrypt, wireshark won’t be able to decrypt the traffic. If we have “tk (temporal key)” then we can select tk option from drop down and decrypt wpa wpa2 frames. in our example, we have got tk as “a6ece97a4d51b496b001bfb1ad029e01” from any data packet for wpa2 psk security decryption.
Comments are closed.