Wireless Transport Layer Security Wtls
Wireless Transport Layer Security Wtls What is wireless transport layer security (wtls)? wireless transport layer security (wtls) is a security level for the wireless application protocol (wap), specifically for the applications that use wap. Wireless transport layer security (wtls) is a security protocol, part of the wireless application protocol (wap) stack. [1] it sits between the wtp and wdp layers in the wap communications stack.
Wireless Transport Layer Security Wtls The primary job of wtls is to provide privacy, data integrity and authentication between applications communicating using wap. wtls is based on and provides similar functionality to the transport layer security (tls) protocol but is optimized for low bandwidth mobile devices. Wtls is based on the industry standard transport layer security (tls) protocol,3 which is a refinement of the secure sockets layer (ssl) protocol. tls is the standard security protocol used between web browsers and web servers. wtls is more efficient that tls, requiring fewer message exchanges. Wireless transport layer security (wtls) was developed for this purpose as a replacement for the flawed wep 802.11b security. it works by performing client and server authentication to confirm the identity of the sender and his or her message. Security layer: this layer contains wireless transport layer security (wtls). it offers data integrity, privacy and authentication. transport layer: this layer contains wireless datagram protocol. it presents consistent data format to higher layers of wap protocol stack. why use wap?.
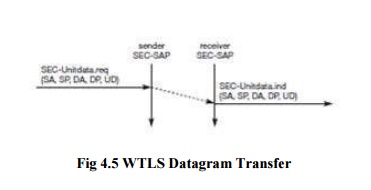
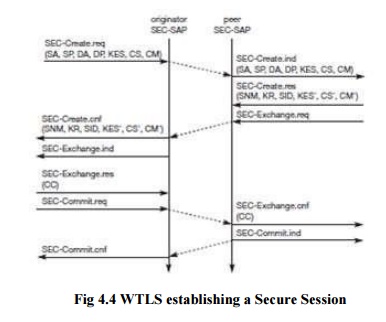
Wireless Transport Layer Security Wtls Wireless transport layer security (wtls) was developed for this purpose as a replacement for the flawed wep 802.11b security. it works by performing client and server authentication to confirm the identity of the sender and his or her message. Security layer: this layer contains wireless transport layer security (wtls). it offers data integrity, privacy and authentication. transport layer: this layer contains wireless datagram protocol. it presents consistent data format to higher layers of wap protocol stack. why use wap?. Wtls provides the upper level layer of wap with a secure transport service interface that preserves the transport service interface below it. in addition, wtls provides an interface for managing (eg, creating and terminating) secure connections. Communication between layers is accomplished by means of service primitives. service primitives represent, in an abstract way, the logical exchange of information and control between the security layer and adjacent layers. Wtls can provide different level of security for privacy data integrity and authentication and has been optimized for low bandwidth high delay network. wtls takes into account low processing power and very limited memory capacity of mobile devices for cryptographic algorithms. Wireless transport layer security (wtls) wireless transport layer service is an optional protocol which provides bearer level security, in a way similar to tls for end to end security.

Wireless Transport Layer Security Wtls Protocol Download Scientific Wtls provides the upper level layer of wap with a secure transport service interface that preserves the transport service interface below it. in addition, wtls provides an interface for managing (eg, creating and terminating) secure connections. Communication between layers is accomplished by means of service primitives. service primitives represent, in an abstract way, the logical exchange of information and control between the security layer and adjacent layers. Wtls can provide different level of security for privacy data integrity and authentication and has been optimized for low bandwidth high delay network. wtls takes into account low processing power and very limited memory capacity of mobile devices for cryptographic algorithms. Wireless transport layer security (wtls) wireless transport layer service is an optional protocol which provides bearer level security, in a way similar to tls for end to end security.
Comments are closed.