Windows Stack Based Buffer Overflow Tutorial Full Eng

Stack Based Windows Buffer Overflow Pdf Computer Engineering This guide will walk you through the fundamentals of stack based buffer overflows on x64 windows, what they are, why they work, and how to set up your environment to start exploring them yourself. Q.how can a buffer overflow be used to control the execution flow of a program? ans a buffer overflow controls a program’s execution flow by overwriting the return address on the program’s.

What Is Stack Based Buffer Overflow In binary exploitation, our primary goal is to subvert the binary's execution in a way that benefits us. a buffer overflow occurs when a program receives data that is longer than expected, such that it overwrites the entire buffer memory space on the stack. When a buffer on the stack overflows, the term stack based overflow or stack buffer overflow is used. when you are trying to write past the end of the stack frame, the term stack overflow is used. don’t mix those two up, as they are entirely different. the next step is to determining the buffer size to write exactly into eip. What is buffer overflow? buffer overflow may happen when a program writes more data to a buffer (user inputs) beyond it can hold. this will lead to memory corruption which mean our buffer can overwrite some important datas of the program in memory. Buffer overflow steps 1. fuzzing parameters 2. controlling eip 3. identifying bad characters 4. finding a return instruction.

What Is Stack Based Buffer Overflow What is buffer overflow? buffer overflow may happen when a program writes more data to a buffer (user inputs) beyond it can hold. this will lead to memory corruption which mean our buffer can overwrite some important datas of the program in memory. Buffer overflow steps 1. fuzzing parameters 2. controlling eip 3. identifying bad characters 4. finding a return instruction. This tutorial is part one of a two part series that focuses on binary exploitation, in particular on x86 stack based windows buffer overflows. this part of the series focuses on the theory behind memory, processors and buffer overflows. This document provides a tutorial on how to recreate a simple stack based buffer overflow in the windows application minishare 1.4.1 for educational purposes. it explains the required knowledge, system setup, and steps to exploit the vulnerability. For this blog, we will be using a simple application vulnerable to stack based buffer overflow. this application does not have any protection mechanisms, such as dep, aslr, cfg, etc. don’t worry if this is your first time exploiting a windows based application. this tutorial will cover most of it. Cnd applied learning walkthroughs htb academy 05.stack based buffer overflows on windows x86 practical exercises skills assessment previous skills assssment.
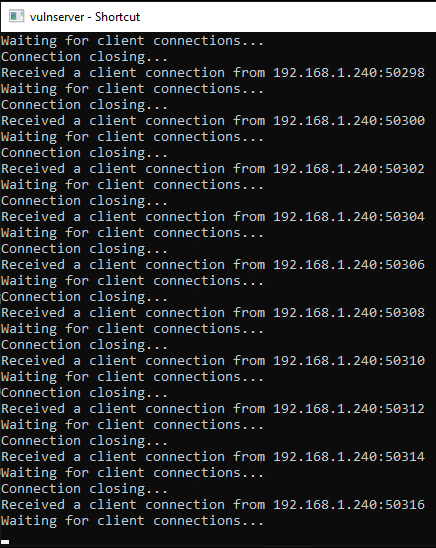
Windows Stack Based Buffer Overflow X86 Swepstopia This tutorial is part one of a two part series that focuses on binary exploitation, in particular on x86 stack based windows buffer overflows. this part of the series focuses on the theory behind memory, processors and buffer overflows. This document provides a tutorial on how to recreate a simple stack based buffer overflow in the windows application minishare 1.4.1 for educational purposes. it explains the required knowledge, system setup, and steps to exploit the vulnerability. For this blog, we will be using a simple application vulnerable to stack based buffer overflow. this application does not have any protection mechanisms, such as dep, aslr, cfg, etc. don’t worry if this is your first time exploiting a windows based application. this tutorial will cover most of it. Cnd applied learning walkthroughs htb academy 05.stack based buffer overflows on windows x86 practical exercises skills assessment previous skills assssment.
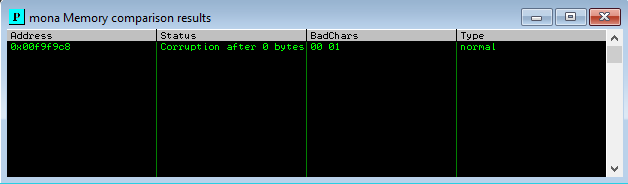
Windows Stack Based Buffer Overflow X86 Swepstopia For this blog, we will be using a simple application vulnerable to stack based buffer overflow. this application does not have any protection mechanisms, such as dep, aslr, cfg, etc. don’t worry if this is your first time exploiting a windows based application. this tutorial will cover most of it. Cnd applied learning walkthroughs htb academy 05.stack based buffer overflows on windows x86 practical exercises skills assessment previous skills assssment.
Comments are closed.