Windows Api Exploitation Writeprocessmemory
Exploiting Windows Api For Red Teaming Writeprocessmemory copies the data from the specified buffer in the current process to the address range of the specified process. any process that has a handle with process vm write and process vm operation access to the process to be written to can call the function. In this blog, we’ll discuss how we can bypass these protections in a vulnerable executable (quotedb.exe) using a technique that leverages the writeprocessmemory api to patch our target process’s memory at runtime.
Demystifying Physical Memory Primitive Exploitation On Windows Windows api exploitation for red blue teams: pentesteracademy course?id=31pentester academy is the world’s leading online cyber security educa. How writeprocessmemory api really writes? while i’m preparing a video in arabic explaining the exploit development process for bof in syncbreeze and part of that exploit is bypassing dep. Exploitation with writeprocessmemory. github gist: instantly share code, notes, and snippets. Learn how win32 apis enable process and memory manipulation for windows evasion. explore openprocess, virtualallocex, writeprocessmemory, and advanced techniques with real command examples.
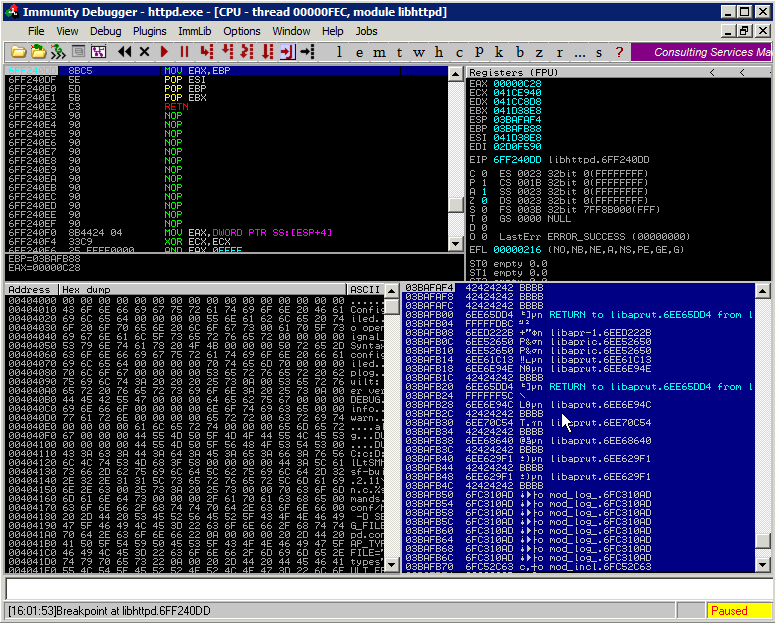
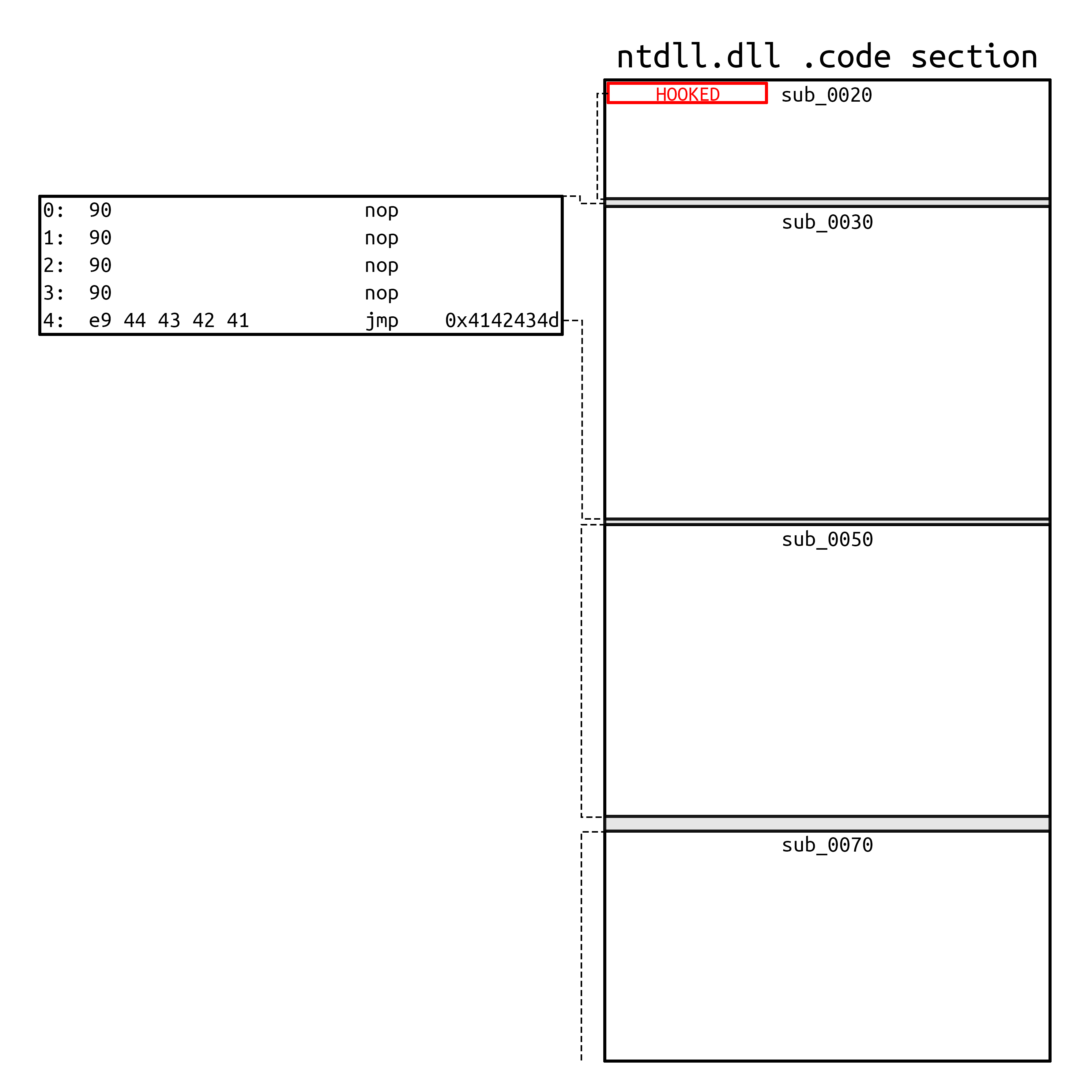
Advanced Windows Exploitation Rop Exploit Exploitation with writeprocessmemory. github gist: instantly share code, notes, and snippets. Learn how win32 apis enable process and memory manipulation for windows evasion. explore openprocess, virtualallocex, writeprocessmemory, and advanced techniques with real command examples. In short writeprocessmemory will write to page execute or page execute read pages if you have sufficient rights (process vm operation) to change its permissions to page execute readwrite. Writeprocessmemory function writes data to an area of memory in a specified process. the entire area to be written to must be accessible or the operation fails. The writeprocessmemory() function to write to itself. using writeprocessmemory() to patch itself removes the requirement of finding a location in a thread to patch, as the destination address is now offset from the known address of writeprocessmemory(). it also removes the need for a second jmp call to the patched location, as the natural flow of. This is the flowchart of the code, and it gives enough understanding of how writeprocessmemory works. before explaning how it works, let me just explain the parameters first.

Windows Api What Is It When Is It Used How To Use By Gc Medium In short writeprocessmemory will write to page execute or page execute read pages if you have sufficient rights (process vm operation) to change its permissions to page execute readwrite. Writeprocessmemory function writes data to an area of memory in a specified process. the entire area to be written to must be accessible or the operation fails. The writeprocessmemory() function to write to itself. using writeprocessmemory() to patch itself removes the requirement of finding a location in a thread to patch, as the destination address is now offset from the known address of writeprocessmemory(). it also removes the need for a second jmp call to the patched location, as the natural flow of. This is the flowchart of the code, and it gives enough understanding of how writeprocessmemory works. before explaning how it works, let me just explain the parameters first.
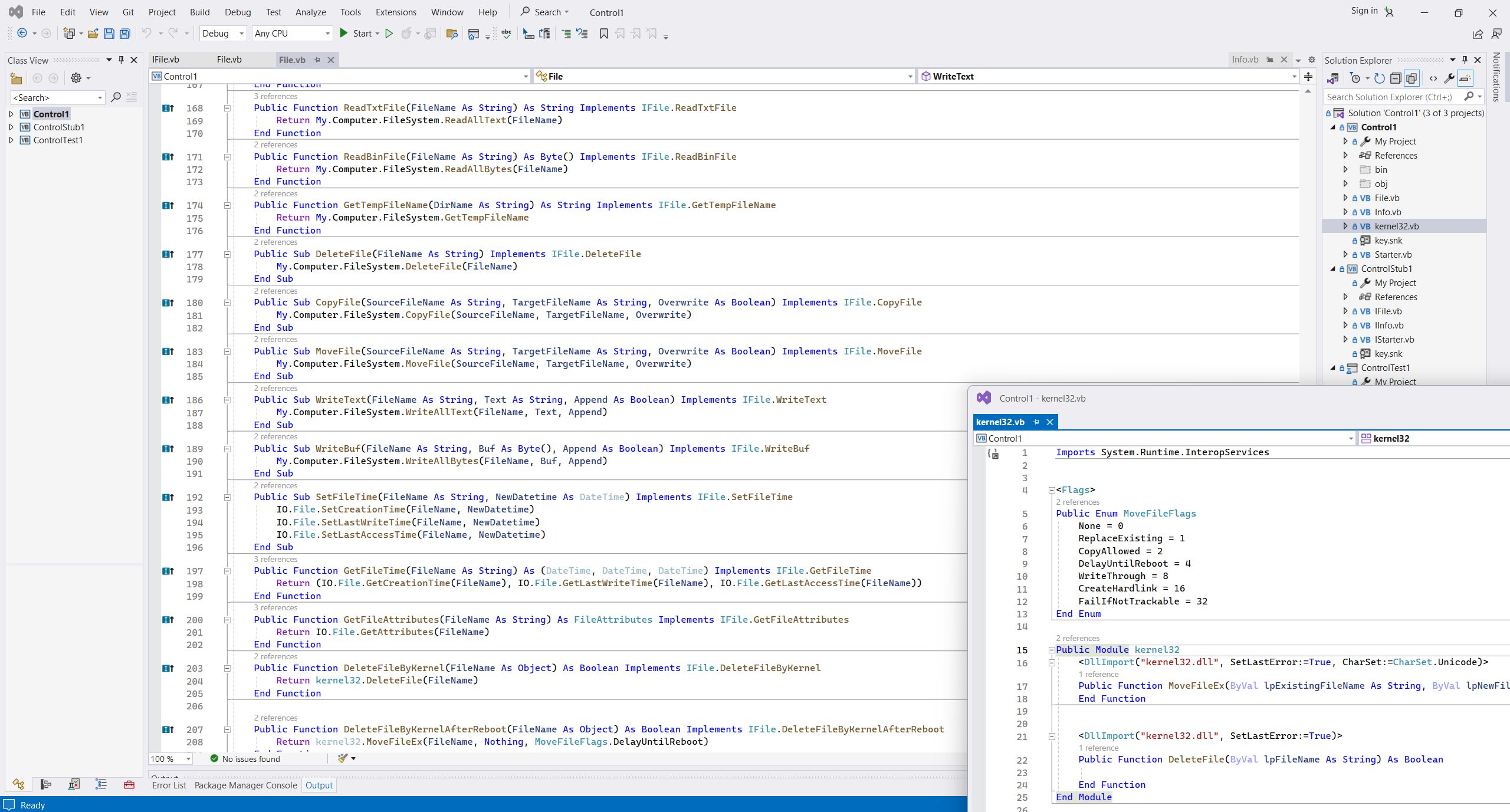
Viacheslav Eremin Rebuilding My Ancient Api Factory On Net 8 0 The writeprocessmemory() function to write to itself. using writeprocessmemory() to patch itself removes the requirement of finding a location in a thread to patch, as the destination address is now offset from the known address of writeprocessmemory(). it also removes the need for a second jmp call to the patched location, as the natural flow of. This is the flowchart of the code, and it gives enough understanding of how writeprocessmemory works. before explaning how it works, let me just explain the parameters first.
Comments are closed.