Windows Access Control Part 1
Lecture 2 Access Control Part 2 Pdf Access Control Computer So, in this article, i will discuss all the details of how windows allow deny certain user from doing an operation based on the user token that is generated after successful authentication. Windows access control is a fundamental security mechanism in windows operating systems that regulates who or what can view or use resources. by understandin.

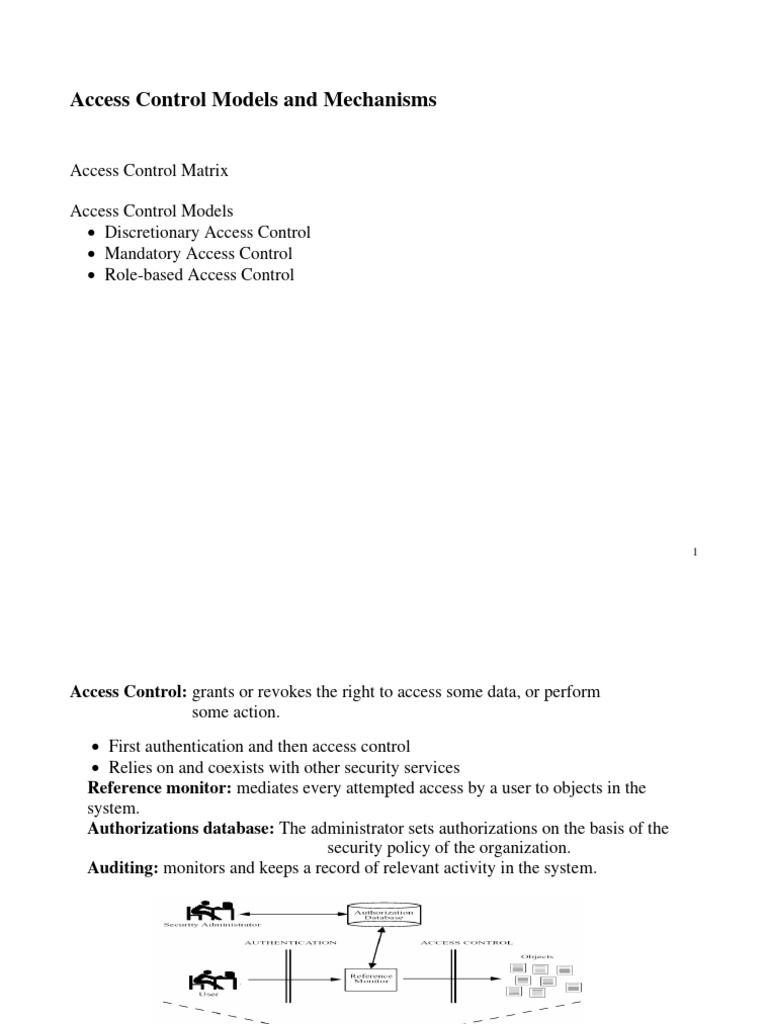
Access Control 2011 Pdf Computer Access Control Access Control This article describes access control in windows, which is the process of authorizing users, groups, and computers to access objects on the network or computer. Access control is one of the important and fundamental topics in windows sdk platform from security category. we will start with the access control model used by windows oses and then dig deeper the details of every component in the model. These are the foundations of understanding how windows users, permissions, and system utilities work, which is essential for both system administration and cybersecurity. Explain how cia can be achieved down to the folder and data file access level for departments and users using active directory and windows server 2012 r2 access control.

Bài 5 Access Control Pdf Access Control Computer Access Control These are the foundations of understanding how windows users, permissions, and system utilities work, which is essential for both system administration and cybersecurity. Explain how cia can be achieved down to the folder and data file access level for departments and users using active directory and windows server 2012 r2 access control. The document outlines lab 1 for implementing access controls using windows active directory, including a lecture presentation and associated worksheet. participants must follow the provided instructions and submit a lab report with screen captures from specific steps. This document provides an overview of access controls in microsoft windows, focusing on authentication models, particularly in standalone workstations versus domain environments using active directory (ad). Unprivileged users will hold limited access, including their files and folders only, and have no means to perform administrative tasks on the host, preventing you from having complete control over your target. Throughout this lab, we will work through a series of exercises that will help you understand how to apply access control in a windows environment. we will start by exploring the basics of access control and then move on to more advanced topics, such as inheritance and advanced permissions.

Windows Access Control System Its Design And Implementation The document outlines lab 1 for implementing access controls using windows active directory, including a lecture presentation and associated worksheet. participants must follow the provided instructions and submit a lab report with screen captures from specific steps. This document provides an overview of access controls in microsoft windows, focusing on authentication models, particularly in standalone workstations versus domain environments using active directory (ad). Unprivileged users will hold limited access, including their files and folders only, and have no means to perform administrative tasks on the host, preventing you from having complete control over your target. Throughout this lab, we will work through a series of exercises that will help you understand how to apply access control in a windows environment. we will start by exploring the basics of access control and then move on to more advanced topics, such as inheritance and advanced permissions.

Lecture3 Accesscontrol Download Free Pdf Password Fingerprint Unprivileged users will hold limited access, including their files and folders only, and have no means to perform administrative tasks on the host, preventing you from having complete control over your target. Throughout this lab, we will work through a series of exercises that will help you understand how to apply access control in a windows environment. we will start by exploring the basics of access control and then move on to more advanced topics, such as inheritance and advanced permissions.
Access Control In Information Security Pdf Computer Access Control
Comments are closed.