Why Mfa Isn T Enough Saas Alerts
Saas Mfa Multi Factor Authentication Jumpcloud Download the infographic to learn why mfa alone isn’t enough, where it falls short and how saas alerts user can fill the security gaps. Most mfa deployments are: strong in saas and cloud environments inconsistent across legacy and on prem systems dependent on passwords and phishable factors this creates a dangerous mismatch between perception and reality. top mfa blind spots 1. legacy systems without mfa coverage modern iam platforms excel at securing cloud applications.

Phishing Stopped Mfa And Saas Security At Work Virtual Sprout For years, multi factor authentication (mfa) was the golden standard for identity security. it absolutely raised the bar, but attackers evolve faster than your security baseline. today, mfa is necessary but tragically insufficient. Mfa is designed to enhance security, but weak implementations can create vulnerabilities that sophisticated attackers can exploit. here are five risks that can stem from an inadequate mfa deployment. This article explains why mfa alone leaves blind spots that attackers routinely exploit, and what a newer layer of defense called identity threat detection and response (itdr) does to close those gaps. Many organizations claim to have implemented multifactor authentication (mfa), but the actual implementation can differ significantly. for some organizations, mfa might consist of a simple.
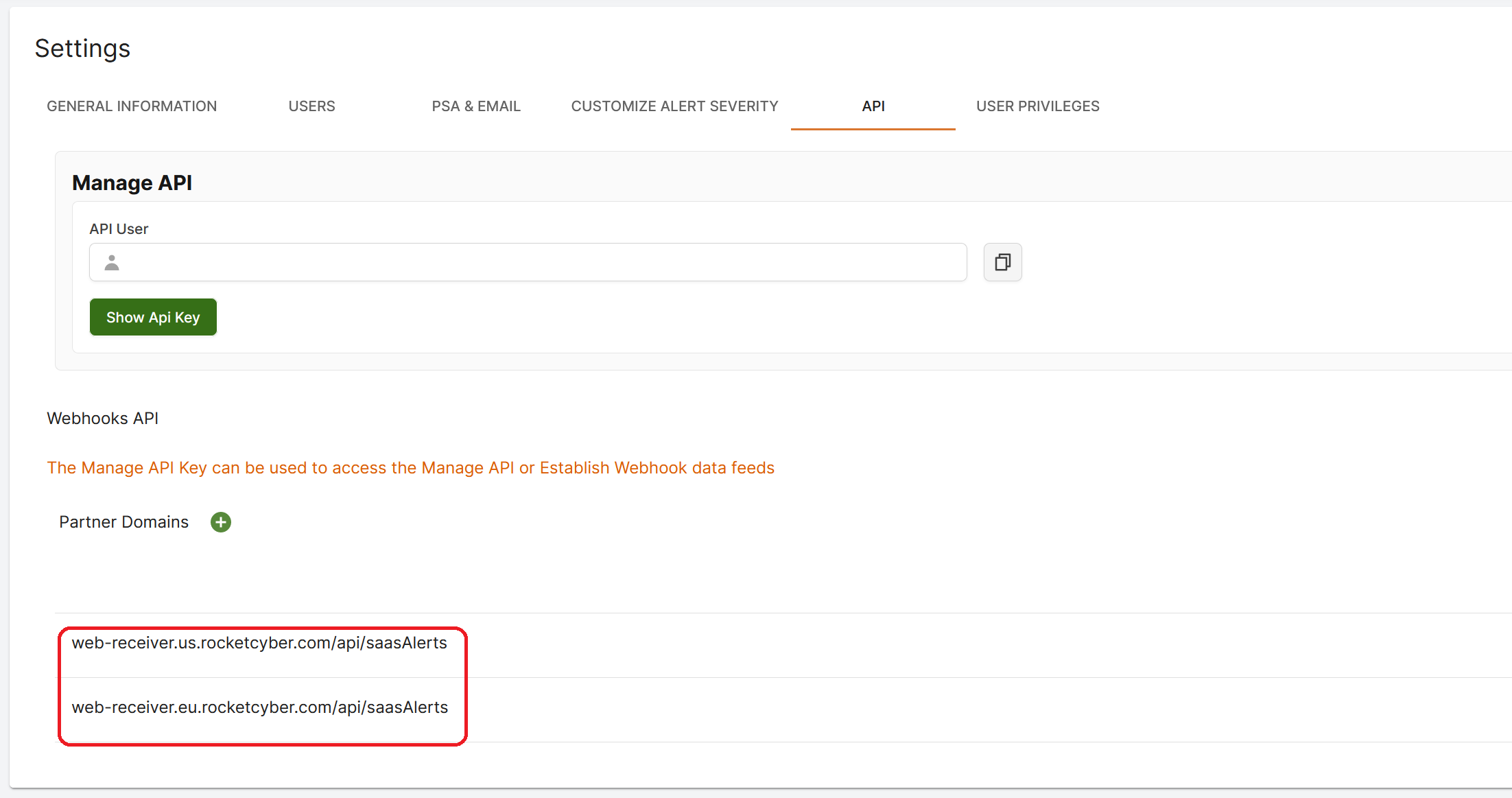
Configuring Saas Alerts This article explains why mfa alone leaves blind spots that attackers routinely exploit, and what a newer layer of defense called identity threat detection and response (itdr) does to close those gaps. Many organizations claim to have implemented multifactor authentication (mfa), but the actual implementation can differ significantly. for some organizations, mfa might consist of a simple. Sure, strong passwords and multi factor authentication (mfa) are critical tools — but just having them isn’t enough anymore. we need to use them the right way and stay alert to the risks. Some organizations still fall back on common excuses to delay or avoid implementing mfa, often citing reasons such as cost, user inconvenience, or a belief that their existing security measures are good enough. Our practicing cybersecurity expert in australia looks at the different types of mfa and how you can use them in a microsoft context, dives deep into "in the middle" schemes and relates a successful client breach, though "we dodged a bullet.". The era of relying on mfa for access based security is coming to a close. 96% of cisos are signaling it can’t keep up, and they’re shifting their strategies accordingly.
Comments are closed.