Why Is Unauthenticated Encryption Insecure
Why Is Unauthenticated Encryption Insecure But not authenticating your encryption can lead to worse issues. a type of attack called padding oracle attacks can let an attacker obtain the plaintext by sending a large number of specially crafted packets. If insecure cryptographic methods or cryptographic configurations are used, the risk of information leakage and compromising (privileged) accounts is high. this significantly raises the chances of a devastating cyberattack and its impact.
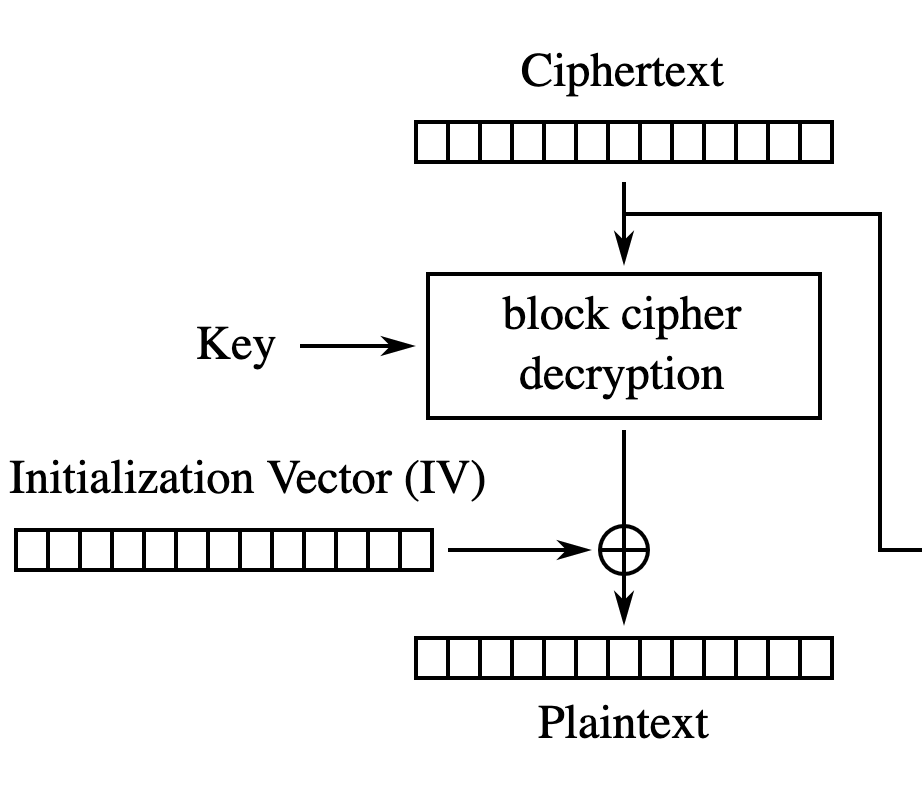
Why Is Unauthenticated Encryption Insecure At first glance you might consider this setup reasonably secure but if authenticated encryption is not used a mitm can modify the ciphertext to cause predictable modifications to the plain text, preserving the user and password but changing the command or its parameters. But what exactly is insecure deserialization? how does it work, and why is it so dangerous?. Because ipsec originally offered encryption without authentication as a recommended and supported option, security researchers have studied this configuration extensively, and they have found it to be insecure. Plicitly identify an important assump tion: nonmalleability. the unauthenticated encryption used in version 4 constitutes lack of nonmalleability, leading to the attack we describe. if a protocol requires nonmalleable encryption, which is more likely than not, clearly state so in the specification, and ensure t.
Authenticated Vs Unauthenticated Vulnerability Scanning Stern Security Because ipsec originally offered encryption without authentication as a recommended and supported option, security researchers have studied this configuration extensively, and they have found it to be insecure. Plicitly identify an important assump tion: nonmalleability. the unauthenticated encryption used in version 4 constitutes lack of nonmalleability, leading to the attack we describe. if a protocol requires nonmalleable encryption, which is more likely than not, clearly state so in the specification, and ensure t. If encryption strength is insecure, attackers may be able to decrypt and access sensitive information, which can lead to data breaches and information disclosure. Learn how to prevent insecure communication through ssl tls, strong cipher suites, and certificate validation. explore example attack scenarios and best practices. this article explains the concept of insecure communication, its impact on security, and how to prevent it. The term “encryption” means reversible encryption, used to protect data at rest and in transit. these applications of encryption are frequently littered with the unexploded ordnance of poor practice and obsolete (or simply bad) algorithms, waiting to explode data upon hackers’ prodding. Therefore, it is vulnerable to various security attacks, such as data tampering or replay attacks, where an attacker can intercept and modify the encrypted data without being detected.

Penetration Testing Approaches And Comparison Between Unauthenticated If encryption strength is insecure, attackers may be able to decrypt and access sensitive information, which can lead to data breaches and information disclosure. Learn how to prevent insecure communication through ssl tls, strong cipher suites, and certificate validation. explore example attack scenarios and best practices. this article explains the concept of insecure communication, its impact on security, and how to prevent it. The term “encryption” means reversible encryption, used to protect data at rest and in transit. these applications of encryption are frequently littered with the unexploded ordnance of poor practice and obsolete (or simply bad) algorithms, waiting to explode data upon hackers’ prodding. Therefore, it is vulnerable to various security attacks, such as data tampering or replay attacks, where an attacker can intercept and modify the encrypted data without being detected.
Comments are closed.