Why Is Jwt Popular

All You Need To Know About Jwt Pt 2 Jwt's popularity stems from their compact structure, built in security features, and suitability for modern distributed architectures. when used correctly, they are a powerful tool. One of the most popular methods for handling these concerns is using json web tokens (jwt). in this post, we'll explore why jwts are a great choice for modern applications and how they can enhance your app's security and performance.
The Ultimate Guide To Handling Jwts On Frontend Clients Graphql Jwt has become a popular choice for authentication because of its efficiency and flexibility, making it an essential tool for developers building secure systems. I think that jwt.io does not explain very well why or when to use jwt. it explains other things that could be ok to consider but not critical to decide whether or not to use it or why it will be handy. Jwts are popular because they’re secure, self contained, easy to use, and perfect for scalable applications. they provide a reliable way to handle authentication, authorization, and secure information exchange. Json web tokens, or jwts, are a cornerstone of modern application security and api protection. you've likely encountered them when implementing login flows, securing microservice communication, or working with standards like oauth 2.0 and openid connect.

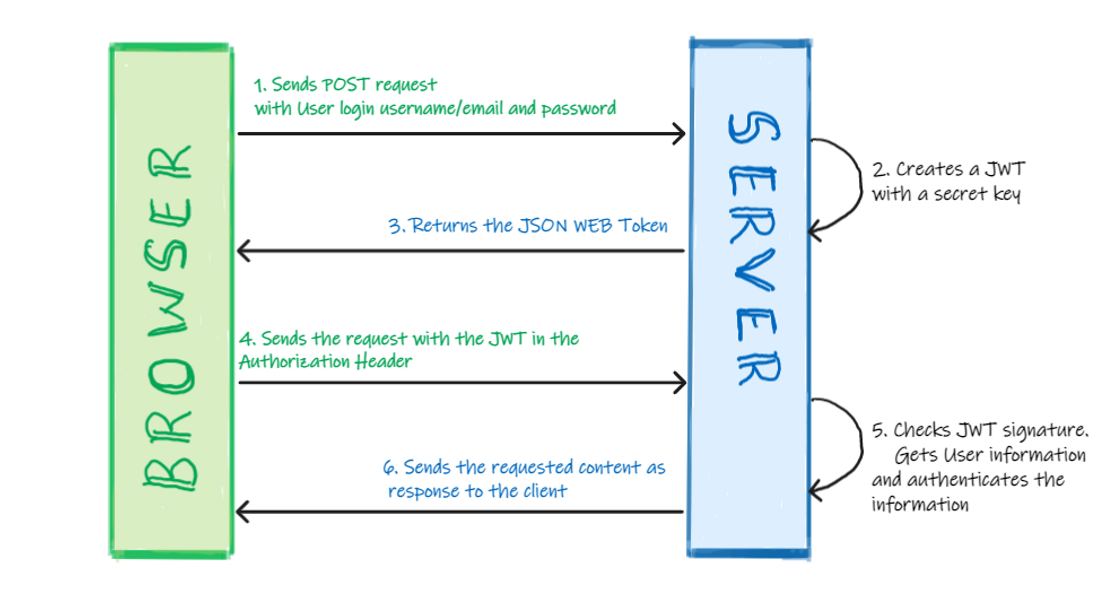
Demystifying Jwt Simi Studio Jwts are popular because they’re secure, self contained, easy to use, and perfect for scalable applications. they provide a reliable way to handle authentication, authorization, and secure information exchange. Json web tokens, or jwts, are a cornerstone of modern application security and api protection. you've likely encountered them when implementing login flows, securing microservice communication, or working with standards like oauth 2.0 and openid connect. The key advantage of jwt authentication is its stateless nature. unlike traditional session based methods, jwts store all the information required for authentication directly in the token itself. this makes it a popular choice for scalable, distributed systems and apis. Jwts are compact, url safe, and widely used for authentication and authorization in modern web applications, apis, and microservices. This article traces jwt’s roots — from its early proposal to its radical adoption — and explores the factors that shaped its rise to becoming an industry default. In this sort of situation, jwt tokens shine because they contain enough information in them to validate the user and their permission set, without having to access a central database. any service can do this independently, locally, and typically very quickly.

Jwt The Key To Secure And Efficient Authentication Codeation Posted The key advantage of jwt authentication is its stateless nature. unlike traditional session based methods, jwts store all the information required for authentication directly in the token itself. this makes it a popular choice for scalable, distributed systems and apis. Jwts are compact, url safe, and widely used for authentication and authorization in modern web applications, apis, and microservices. This article traces jwt’s roots — from its early proposal to its radical adoption — and explores the factors that shaped its rise to becoming an industry default. In this sort of situation, jwt tokens shine because they contain enough information in them to validate the user and their permission set, without having to access a central database. any service can do this independently, locally, and typically very quickly.

What Is Jwt Json Web Token Sre How To This article traces jwt’s roots — from its early proposal to its radical adoption — and explores the factors that shaped its rise to becoming an industry default. In this sort of situation, jwt tokens shine because they contain enough information in them to validate the user and their permission set, without having to access a central database. any service can do this independently, locally, and typically very quickly.
Understanding Json Web Tokens Jwt A Comprehensive Guide Suketa
Comments are closed.