Why Is Hardcoding Sensitive Data Like Usernames Passwords Api Keys
Why Is Hardcoding Sensitive Data Like Usernames Passwords Api Keys Hardcoding sensitive data like usernames, passwords, api keys, or database connection strings in your source code is risky because it can lead to security vulnerabilities. if your. From api keys to database passwords, sensitive information should never be embedded directly into source code. instead, developers should adopt secure practices such as using secret management tools, storing secrets in environment variables, and automating secret detection in ci cd pipelines.

Why Is Hardcoding Sensitive Data Like Usernames Passwords Api Keys Learn why hardcoding credentials like usernames, passwords, and api keys in your app code is a critical security risk. discover the main dangers, consequences, and solutions. Discover why hardcoding secrets in your code is dangerous and how to keep your api keys, tokens, and passwords truly secret. When developers hardcode secret data like api keys into mobile apps, it's easy for unauthorized users to access backend systems and cloud services. In this lesson, you’ll learn why hardcoding secrets is dangerous, and how to properly manage sensitive data using modern, secure tools like environment variables and secrets managers.

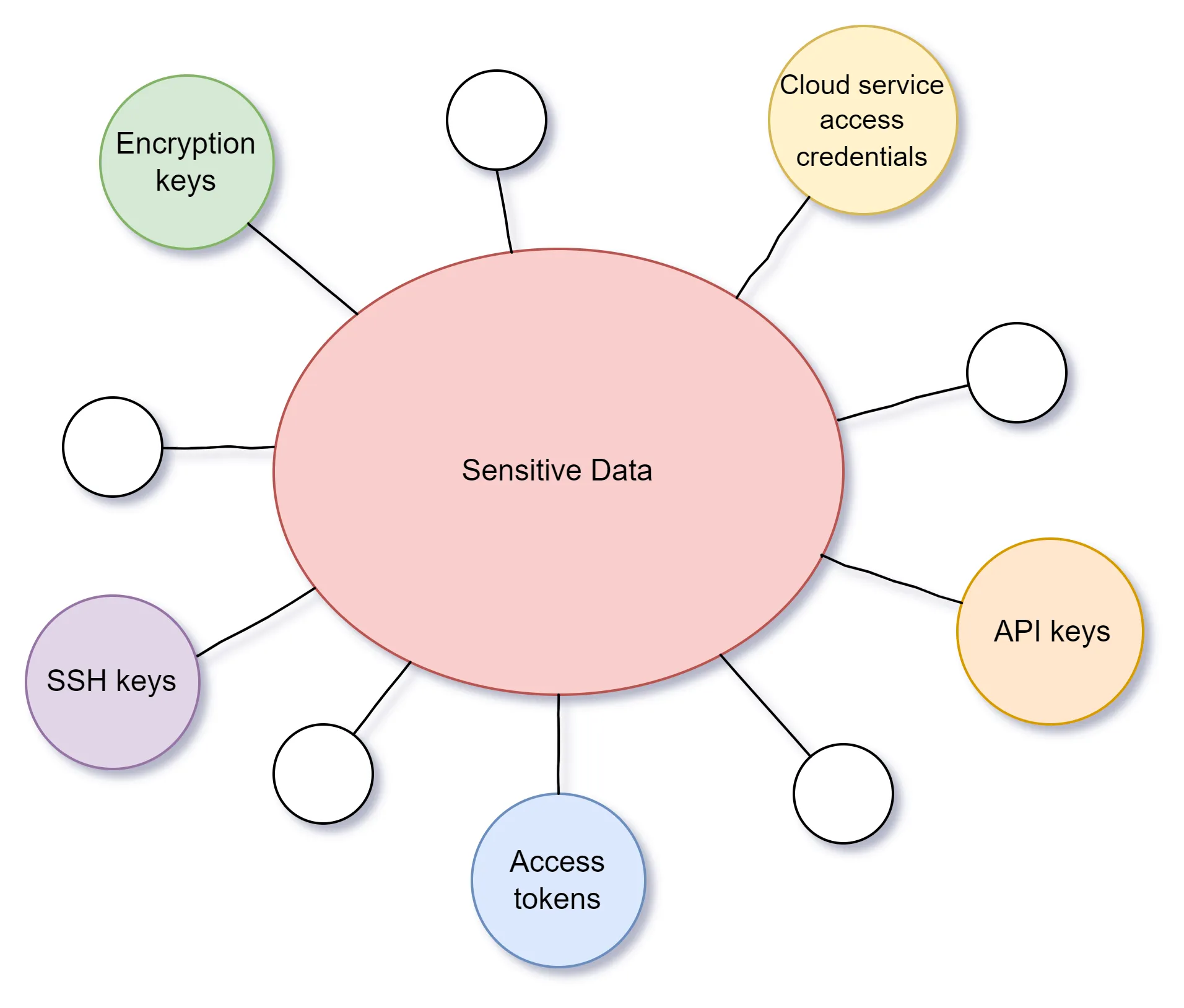
Why Is Hardcoding Sensitive Data Like Usernames Passwords Api Keys When developers hardcode secret data like api keys into mobile apps, it's easy for unauthorized users to access backend systems and cloud services. In this lesson, you’ll learn why hardcoding secrets is dangerous, and how to properly manage sensitive data using modern, secure tools like environment variables and secrets managers. Hard coded secrets can be found in various places within software applications. they often lurk innocuously in source code files, where developers may embed sensitive information like api keys, passwords, or encryption keys directly into the code. However, one such shortcut—hardcoding credentials—can turn into a nightmare for your security team and your entire organization. let’s dive into the world of hardcoded credentials, explore why they are a significant risk, and most importantly, learn how to avoid or manage them safely. With strict standards like soc 2, iso 27001, or gdpr, hardcoding secrets violates regulations, leaving your system vulnerable both in terms of security and compliance. Hardcoded secrets are sensitive credentials, such as api keys, passwords, tokens, and certificates, that are embedded directly into application source code or configuration files.

Why Is Hardcoding Sensitive Data Like Usernames Passwords Api Keys Hard coded secrets can be found in various places within software applications. they often lurk innocuously in source code files, where developers may embed sensitive information like api keys, passwords, or encryption keys directly into the code. However, one such shortcut—hardcoding credentials—can turn into a nightmare for your security team and your entire organization. let’s dive into the world of hardcoded credentials, explore why they are a significant risk, and most importantly, learn how to avoid or manage them safely. With strict standards like soc 2, iso 27001, or gdpr, hardcoding secrets violates regulations, leaving your system vulnerable both in terms of security and compliance. Hardcoded secrets are sensitive credentials, such as api keys, passwords, tokens, and certificates, that are embedded directly into application source code or configuration files.
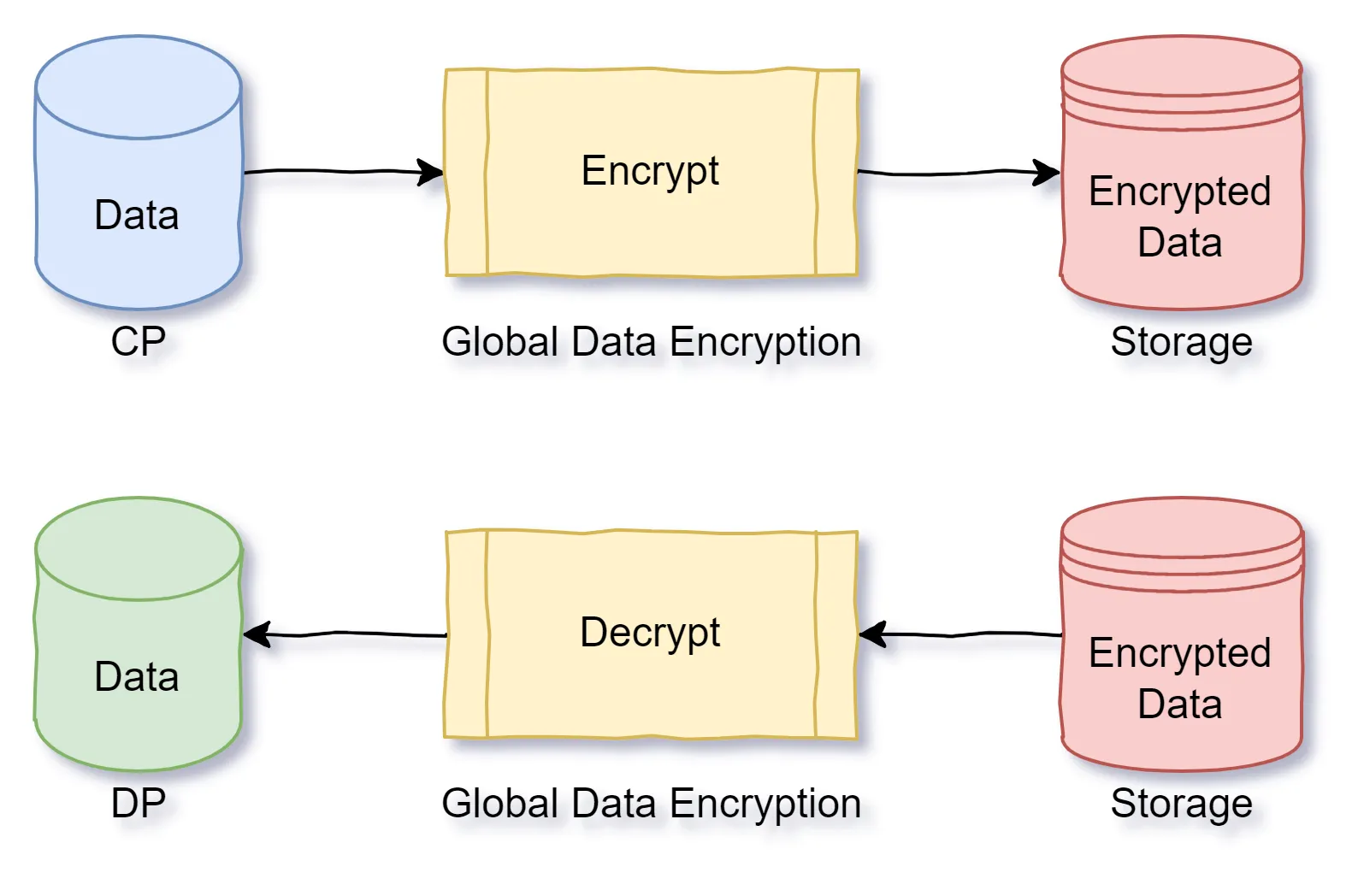
How To Prevent Sensitive Data From Leaking In Api Gateway Api7 Ai With strict standards like soc 2, iso 27001, or gdpr, hardcoding secrets violates regulations, leaving your system vulnerable both in terms of security and compliance. Hardcoded secrets are sensitive credentials, such as api keys, passwords, tokens, and certificates, that are embedded directly into application source code or configuration files.
How To Prevent Sensitive Data From Leaking In Api Gateway Api7 Ai
Comments are closed.