Why Encrypted Visibility Engine Eve Is Essential For Network Security

Why Encrypted Visibility Engine Eve Is Essential For Network Security Eve is a new means of identifying client applications and processes utilizing tls encryption. it enables visibility and allows administrators to take actions and enforce policy within their environments. eve works by fingerprinting the client hello packet in the tls handshake. Encrypted visibility engine (eve) uses transport layer security (tls) encryption to identify client apps and processes. without decryption, eve offers greater insight into the encrypted sessions. administrators can impose policy actions on the traffic in their settings based on the results of eve.
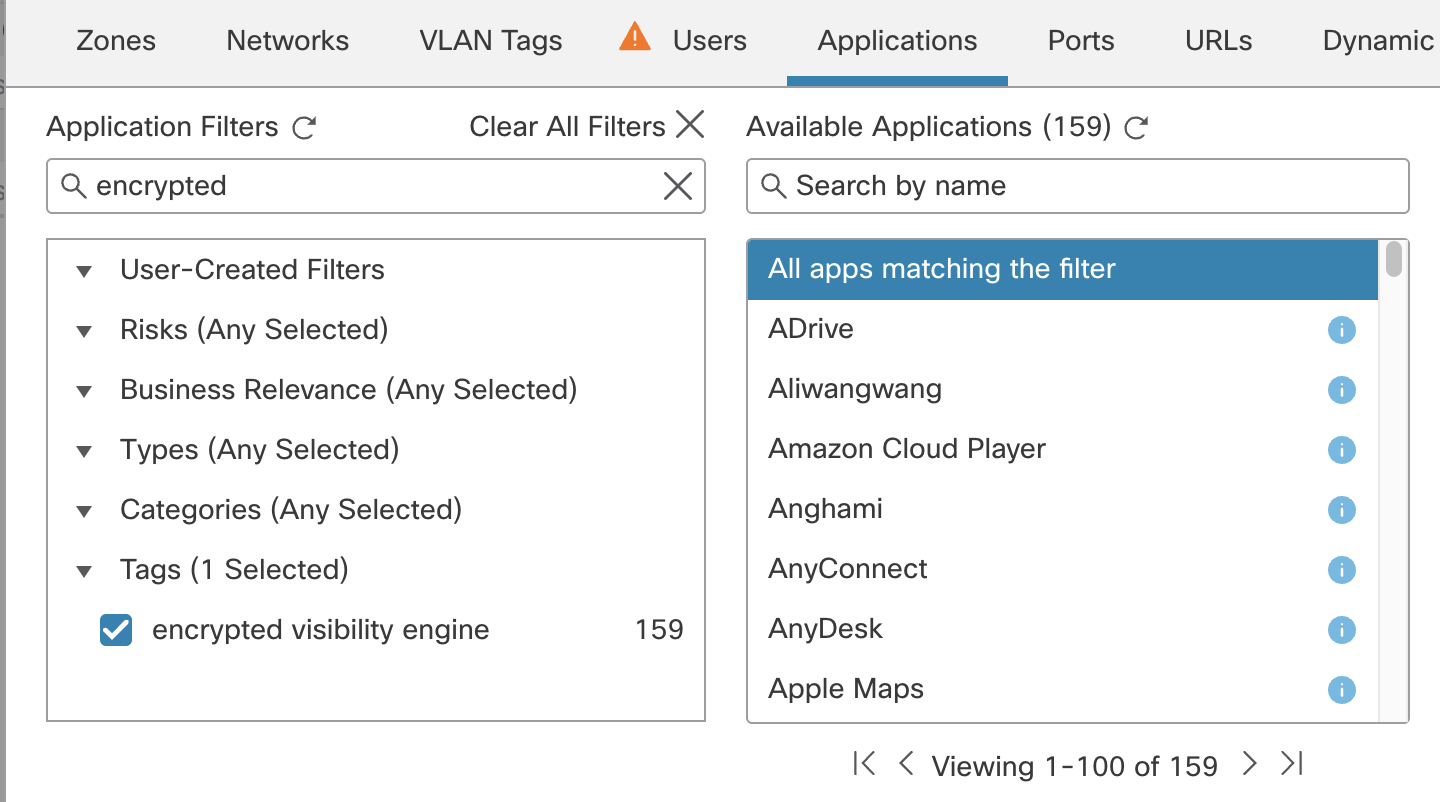
Encrypted Visibility Engine Encryption is here to stay — and attackers hide inside it. cisco secure firewall’s eve brings visibility back, without breaking, decrypting, or touching user content. The enhanced cisco encrypted visibility engine (eve) is part of the 7.4 version of the secure firewall operating system. version 7.4 also includes zero trust capabilities and improved. This session will explain decryption logic on the cisco secure firewall in detail, along with examples and demonstrations. we will also look at how to gain visibility into secured traffic without decryption using the machine learning empowered encrypted visibility engine. This article breaks down how eve currently works, where ech disrupts visibility, and what defenders can still rely on in a world where encryption continues to harden.

Encrypted Visibility Engine Pdf Transport Layer Security Computing This session will explain decryption logic on the cisco secure firewall in detail, along with examples and demonstrations. we will also look at how to gain visibility into secured traffic without decryption using the machine learning empowered encrypted visibility engine. This article breaks down how eve currently works, where ech disrupts visibility, and what defenders can still rely on in a world where encryption continues to harden. In summary, cisco’s **eve** leverages metadata from encrypted traffic, including tls 1.3, to provide administrators with visibility and control over their network security, without the need for resource heavy decryption. Encrypted visibility engine (eve) does traffic analysis through metadata inspection and behavior analysis as the main mechanism. by examining packet headers, flow patterns, and statistical anomalies, eve can discover any suspicious activities, even if the data itself is still encrypted. In an era where encryption is the norm, eve ensures security teams maintain critical visibility without compromising privacy or performance. eve detected malicious activity across encrypted quic and tls connections, without decryption. Learn how the encrypted visibility engine (eve) uses ml ai to identify encrypted malware communication even when it is destined to trustworthy cloud services.
Comments are closed.