Why C2 Frameworks Are Perfect For Pros Stealthy Operations
Github 0xsojalsec C2 Frameworks Awesome Command Control C2 In this blog, we explained how powerful c2 frameworks can be in maintaining stealthy operations for both red teams and cybercriminals. we highlighted examples where advanced persistent threats (apts) leverage trusted applications and networks to conceal post exploitation activity. Despite new c2 frameworks appearing every year, these five still form the backbone of real world offensive operations. whether you’re defending networks, threat hunting, or running red team campaigns, understanding how these frameworks function—and why they continue to dominate is essential.

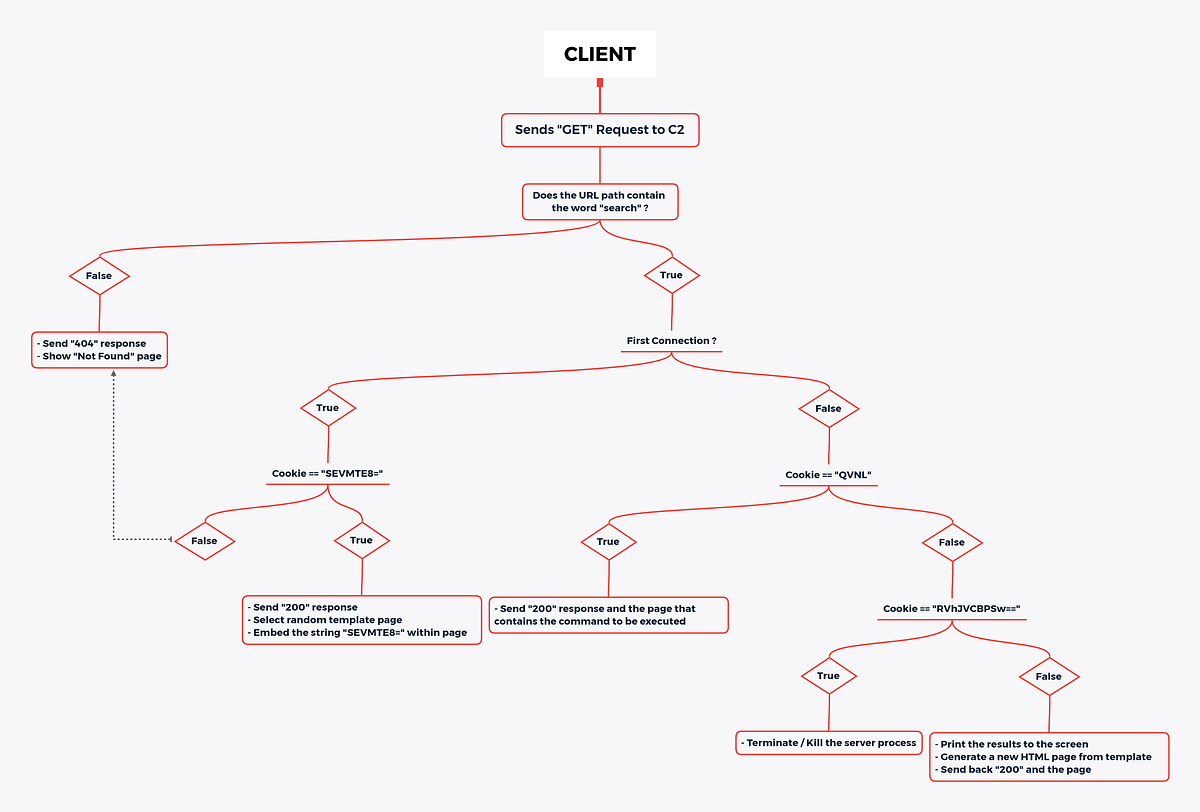
How C2 Frameworks Work Learn what c2 frameworks are, how they work, the most widely used tools like cobalt strike, metasploit, and sliver, and how red teams and defenders use them in modern cybersecurity operations. Attackers are rapidly shifting to modular, cloud integrated c2 frameworks—sliver, havoc, mythic, brute ratel c4, and cobalt strike—blurring lines between apt and cybercrime. these tools’ stealth, automation, and cloud api abuse are outpacing legacy detection, demanding urgent defensive adaptation. In this video i will show how hackers leverage c2 frameworks for stealthy tactics using staged payloads. i will use sliver framework as an example and i will also show some basic. Post exploitation frameworks consist of tools and techniques that attackers can use after gaining initial access to a system. these frameworks are specifically designed to maintain.

Introduction To C2 Frameworks In this video i will show how hackers leverage c2 frameworks for stealthy tactics using staged payloads. i will use sliver framework as an example and i will also show some basic. Post exploitation frameworks consist of tools and techniques that attackers can use after gaining initial access to a system. these frameworks are specifically designed to maintain. Learn how command and control (c2) attacks work, including emerging stealth techniques, real world examples, and modern detection using ai and behavioral analysis. Discover common c2 frameworks used by attackers and learn how knowing them helps boost your cybersecurity defense. Benefits of c2 frameworks stealth: they can incorporate various evasion techniques, including using ssl certificates, to encrypt data and hide malicious activities, masquerading as legitimate network traffic, and hiding the ip addresses of an attacker through c2 redirectors. In this article, we examine the fundamentals of command and control (c2) operations, their role in the attack lifecycle, the tools and techniques attackers use to maintain covert access, and evade detection while remotely executing their objectives.

Open Source C2 Frameworks Used In Red Teaming Vulnerable To Rce Attacks Learn how command and control (c2) attacks work, including emerging stealth techniques, real world examples, and modern detection using ai and behavioral analysis. Discover common c2 frameworks used by attackers and learn how knowing them helps boost your cybersecurity defense. Benefits of c2 frameworks stealth: they can incorporate various evasion techniques, including using ssl certificates, to encrypt data and hide malicious activities, masquerading as legitimate network traffic, and hiding the ip addresses of an attacker through c2 redirectors. In this article, we examine the fundamentals of command and control (c2) operations, their role in the attack lifecycle, the tools and techniques attackers use to maintain covert access, and evade detection while remotely executing their objectives.
Comments are closed.