Why Adding More Security Controls Can Increase Risk

Risk Analysis Vs Security Controls Pdf Risk Risk Management We highlighted key factors that influence the selection and identification of security controls, including user group considerations, risk management practices, and organizational requirements. In practice, introducing overly complex or misaligned security controls can reduce resilience, reduce productivity, increase hidden risk, and erode operational efficiency, without.

Security Risk Of Access Controls In my experience, redesigning controls is less about adding new ones and more about removing or consolidating existing layers. i have previously worked with cfos to reduce the total number of formal approvals while improving clarity around decision rights. To mitigate these risks, organizations must implement effective security controls that protect their assets from potential threats. in this article, we will explore the concept of security controls in risk management, their types, and how to implement them effectively. Mitigating risks: effective security controls help identify and mitigate potential security threats before they can cause significant harm. the concept of security controls has evolved significantly over time. There are three common ways that businesses can unintentionally open themselves up to security risks through complexity: by adding systems, adding people, and adding complexity. let’s explore each of these in more detail. the more business systems you have, the greater the attack surface.

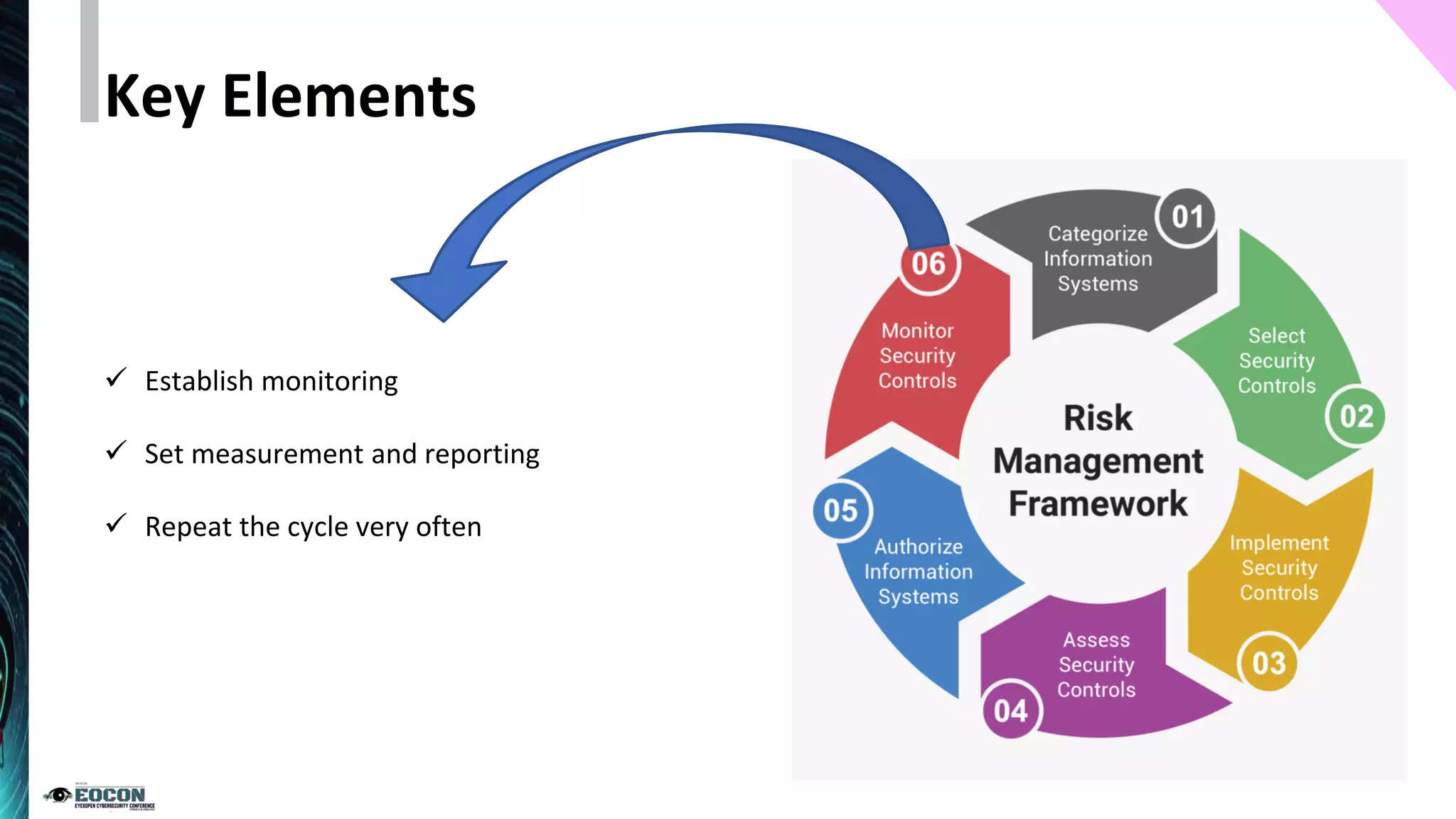
Implementing Security Controls For Comprehensive Risk Mitigation Mitigating risks: effective security controls help identify and mitigate potential security threats before they can cause significant harm. the concept of security controls has evolved significantly over time. There are three common ways that businesses can unintentionally open themselves up to security risks through complexity: by adding systems, adding people, and adding complexity. let’s explore each of these in more detail. the more business systems you have, the greater the attack surface. Security control enhancement is critical for ensuring that an organization’s security controls are relevant and effective in addressing current and emerging cyber threats. it also helps organizations to comply with regulatory requirements, industry standards, and best practices. Security controls can also help you limit the risk of data loss or breach. they can also help you enforce policies and best practices to protect your networks, hardware, software, and sensitive information, ultimately avoiding potential fines and penalties in case of data breaches. Based on a review of the literature and practical experience in the area, the chapter presents a broad overview of various challenges related to cyber security and specifically highlights the importance of implementing effective cyber security controls for active cyber security risk management. Environments are packed with controls across email, identity, endpoint, and cloud, yet risk stays high because those tools aren't fully configured, enforced, or validated.
Top Security Controls To Reduce Your Risk Lmg Security Security control enhancement is critical for ensuring that an organization’s security controls are relevant and effective in addressing current and emerging cyber threats. it also helps organizations to comply with regulatory requirements, industry standards, and best practices. Security controls can also help you limit the risk of data loss or breach. they can also help you enforce policies and best practices to protect your networks, hardware, software, and sensitive information, ultimately avoiding potential fines and penalties in case of data breaches. Based on a review of the literature and practical experience in the area, the chapter presents a broad overview of various challenges related to cyber security and specifically highlights the importance of implementing effective cyber security controls for active cyber security risk management. Environments are packed with controls across email, identity, endpoint, and cloud, yet risk stays high because those tools aren't fully configured, enforced, or validated.

The Importance Of Risk Controls In Cyber Security Huntsman Based on a review of the literature and practical experience in the area, the chapter presents a broad overview of various challenges related to cyber security and specifically highlights the importance of implementing effective cyber security controls for active cyber security risk management. Environments are packed with controls across email, identity, endpoint, and cloud, yet risk stays high because those tools aren't fully configured, enforced, or validated.
Effective Information Security Risk And Controls Management Pdf
Comments are closed.