What The Tech Router Attacks
Four Faith Industrial Router Vulnerability Exploited In Attacks Nattytech We show you how the most dangerous wi fi network attacks work and how you can protect yourself against them: this means you immediately have the right answer to hacker attacks at hand and can. From the fbi’s list of end‑of‑life routers to sophisticated backdoor campaigns on asus and four‑faith devices, the threat landscape is evolving daily. by updating firmware, changing passwords, disabling unnecessary services, and segmenting your network, you can dramatically reduce the risk.

4 Dangerous Router Attacks To Watch Out For Tci Technologies Now, the fbi has issued a warning that 13 routers are vulnerable to a cybercriminal proxy service attack. The fbi has warned that more than a dozen old router models are vulnerable to attacks from cybercriminals. We provide advice for network defenders and small office home office (soho) network administrators to scan their routers for indications of them being used by nation state threat actors and cybercriminals. From january to february 2025, researchers observed a sharp increase in attack campaigns targeting network infrastructure. routers alone account for more than half of the devices associated with critical vulnerabilities and exploitation risks.

How To Prevent Your Home Router From Being Targeted By Hackers We provide advice for network defenders and small office home office (soho) network administrators to scan their routers for indications of them being used by nation state threat actors and cybercriminals. From january to february 2025, researchers observed a sharp increase in attack campaigns targeting network infrastructure. routers alone account for more than half of the devices associated with critical vulnerabilities and exploitation risks. In the age of ransomware attacks and other data breaches, securing your network is more important than ever—and that includes wi fi. watch out for these common router attacks that can put a company offline relatively easily. Eclypsium emphasizes that backdoored juniper networking devices are at the center of the recent attacks. in january 2025, the first attack campaign was revealed and dubbed j magic, involving attackers dropping a backdoor onto carrier grade juniper routers. Most concerning for home users and businesses alike is the concentration of attacks targeting iot devices and consumer grade routers. the report indicates that a full 42% of all identified cve related traffic specifically targeted these devices. Home routers, the unsung heroes of modern connectivity, are increasingly becoming favorite targets for cybercriminals. these devices are the gateway to our digital lives, managing everything from emails and streaming to smart home devices.
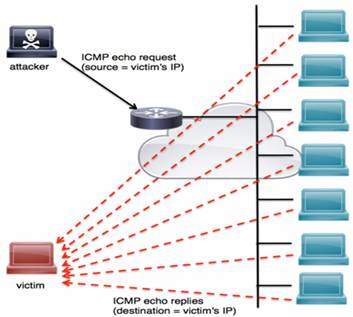
Router Attacks Tutorial In the age of ransomware attacks and other data breaches, securing your network is more important than ever—and that includes wi fi. watch out for these common router attacks that can put a company offline relatively easily. Eclypsium emphasizes that backdoored juniper networking devices are at the center of the recent attacks. in january 2025, the first attack campaign was revealed and dubbed j magic, involving attackers dropping a backdoor onto carrier grade juniper routers. Most concerning for home users and businesses alike is the concentration of attacks targeting iot devices and consumer grade routers. the report indicates that a full 42% of all identified cve related traffic specifically targeted these devices. Home routers, the unsung heroes of modern connectivity, are increasingly becoming favorite targets for cybercriminals. these devices are the gateway to our digital lives, managing everything from emails and streaming to smart home devices.
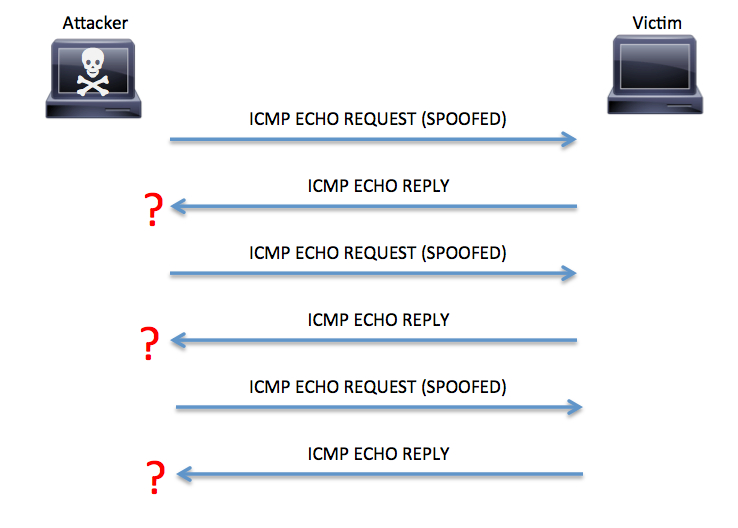
Router Attacks Tutorial Most concerning for home users and businesses alike is the concentration of attacks targeting iot devices and consumer grade routers. the report indicates that a full 42% of all identified cve related traffic specifically targeted these devices. Home routers, the unsung heroes of modern connectivity, are increasingly becoming favorite targets for cybercriminals. these devices are the gateway to our digital lives, managing everything from emails and streaming to smart home devices.
Comments are closed.