What Should I Do%e6%88%91%e8%af%a5%e6%80%8e%e4%b9%88%e5%8a%9efunny Moviedailylife
Should A Patient With Leukopenia White Blood Cell Count Of 3 6 And Url encoding converts characters into a format that can be transmitted over the internet. urls can only be sent over the internet using the ascii character set. since urls often contain characters outside the ascii set, the url has to be converted into a valid ascii format. What is url encoding? percent encoding, also known as url encoding, is a mechanism for encoding information in a uniform resource identifier (uri) under certain circumstances.
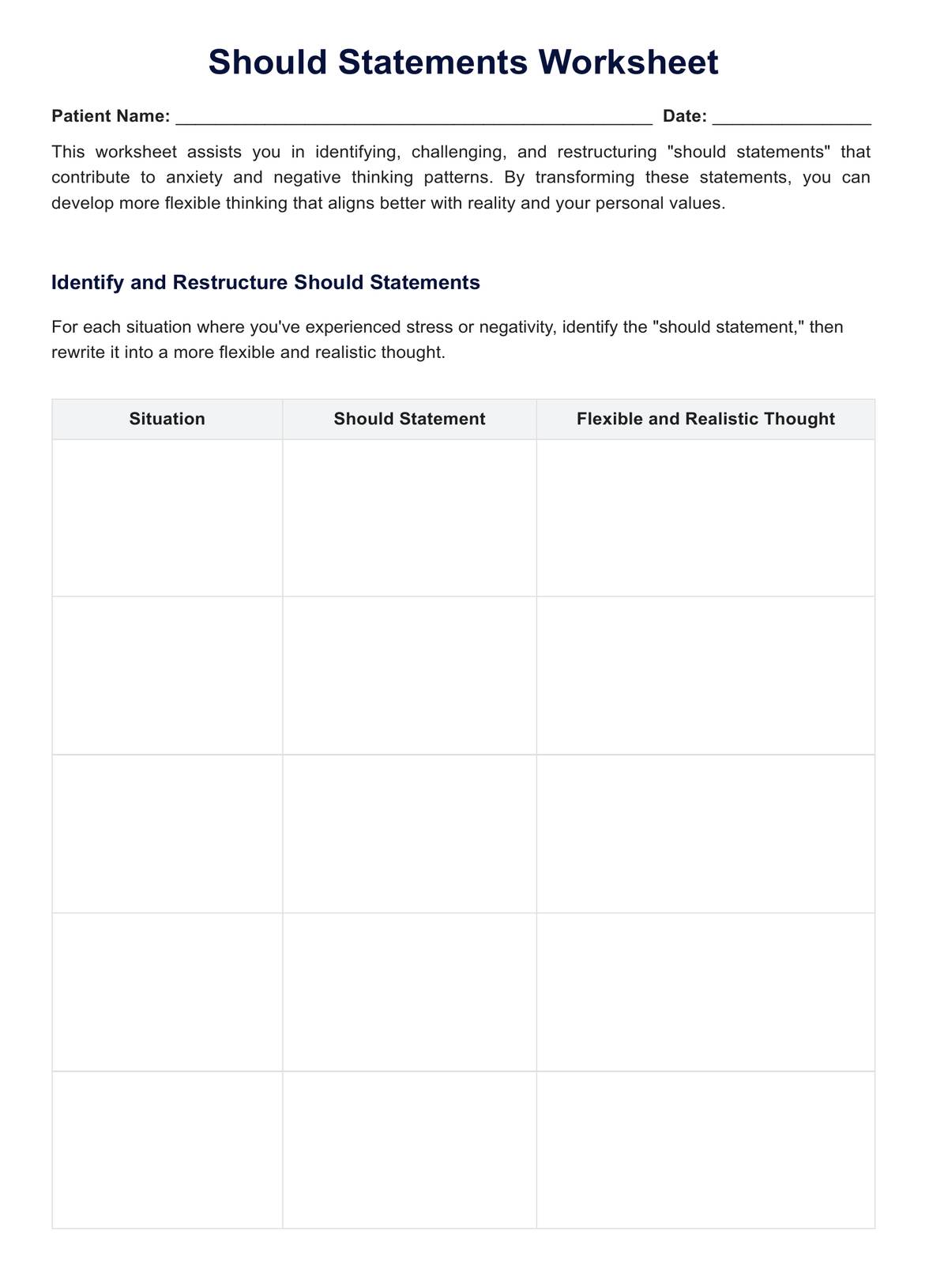
Should Statements Worksheet Example Free Pdf Download It is an acronym for uniform resource locator. a url is an address that browsers probe in order to connect to a web server. two example url's could be: url's strictly use the ascii character set to send data across the internet. they, therefore, must be encoded before being sent. Learn how to do anything with wikihow, the world's most popular how to website. easy, well researched, and trustworthy instructions for everything you want to know. Use a proper html parsing library, like beautifulsoup. from bs4 import beautifulsoup; from urllib import unquote; result = beautifulsoup(unquote(special text)).get text('\n', strip=true) produces very clean unicode output without having to do a lot of regular expression work. There two steps in which url escape online works. in first step the all characters in the string separated using utf 8 encoding. convert each character that are not ascii letters into hexadecimal values. please check the table below to find out the backend key code against each charset.

What Should I Do R Antivirus Use a proper html parsing library, like beautifulsoup. from bs4 import beautifulsoup; from urllib import unquote; result = beautifulsoup(unquote(special text)).get text('\n', strip=true) produces very clean unicode output without having to do a lot of regular expression work. There two steps in which url escape online works. in first step the all characters in the string separated using utf 8 encoding. convert each character that are not ascii letters into hexadecimal values. please check the table below to find out the backend key code against each charset. Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for. Kamidummies are hostile npcs encountered in the second wave of uncertified, added in v0.9.0 along with their exclusive map. kamidummies appear to be typical uncertified dummies, harboring no differences in appearance but are armed with a bobm as their weapon. In this paper,based on the method of generalized = binomial=20 series,the probability that a random lattice point touches a given = boundary line=20 is obtained. 1. graham r = l.knuth d=20 e.patashnik o concrete=20 mathematics:a foundation for computer science 1994 () 2. =e6=9c=ac=e6=96=87=e5=8c=85=e5=90=ab=e4=bb=a5=e4=b8=8b=e4=b8=bb=e9=a2=98= =ef=bc=9a.

What Should You Do If Your Infant Has Dengue Search the world's information, including webpages, images, videos and more. google has many special features to help you find exactly what you're looking for. Kamidummies are hostile npcs encountered in the second wave of uncertified, added in v0.9.0 along with their exclusive map. kamidummies appear to be typical uncertified dummies, harboring no differences in appearance but are armed with a bobm as their weapon. In this paper,based on the method of generalized = binomial=20 series,the probability that a random lattice point touches a given = boundary line=20 is obtained. 1. graham r = l.knuth d=20 e.patashnik o concrete=20 mathematics:a foundation for computer science 1994 () 2. =e6=9c=ac=e6=96=87=e5=8c=85=e5=90=ab=e4=bb=a5=e4=b8=8b=e4=b8=bb=e9=a2=98= =ef=bc=9a.
Comments are closed.