What S Hash Hash Function Explained For Cybersecurity

3 Hash Functions Pdf Espionage Techniques Secure Communication From encryption to file verification, hashing plays a foundational role in cybersecurity strategies. in this guide, we’ll answer what’s hash, explore hash function explained, detail hashing in cybersecurity, and break down how hash algorithms work—all in simple, practical terms. Hashing is a one way mathematical function that turns data into a string of nondescript text that cannot be reversed or decoded. in the context of cybersecurity, hashing is a way to keep sensitive information and data — including passwords, messages, and documents — secure.

What Is A Hash Function Simple Guide For Beginners Hashing is a fundamental concept in cryptography and information security. our guide explores the principles of hashing, explaining how cryptographic hash functions work and their importance in protecting sensitive data. Cryptographic hash functions protect data integrity by creating identifying hash values, which enable systems to identify any unauthorized changes to messages or files in real time. Hash functions are crucial in modern cybersecurity, from protecting your credentials to powering blockchain technology. let’s break down hash functions, how they work, and why they matter for everyday internet users. Learn how cryptographic hash functions work, from md5 to sha 256 and sha 512. covers the avalanche effect, collision attacks, password hashing with bcrypt argon2, hmac authentication, and real world applications in blockchain, tls, and git.

Hash Functions Definition Usage And Examples Ionos Hash functions are crucial in modern cybersecurity, from protecting your credentials to powering blockchain technology. let’s break down hash functions, how they work, and why they matter for everyday internet users. Learn how cryptographic hash functions work, from md5 to sha 256 and sha 512. covers the avalanche effect, collision attacks, password hashing with bcrypt argon2, hmac authentication, and real world applications in blockchain, tls, and git. Learn what a hash value is, how it works, and why it's essential for cybersecurity. from passwords to file integrity, hashing is your digital fingerprint. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Discover what a hash function is, how it works, and why it's essential for protecting data, verifying integrity, and strengthening cybersecurity. Learn what hash means, how hashing works, and why it's essential for data integrity, cybersecurity, and encryption strategies.
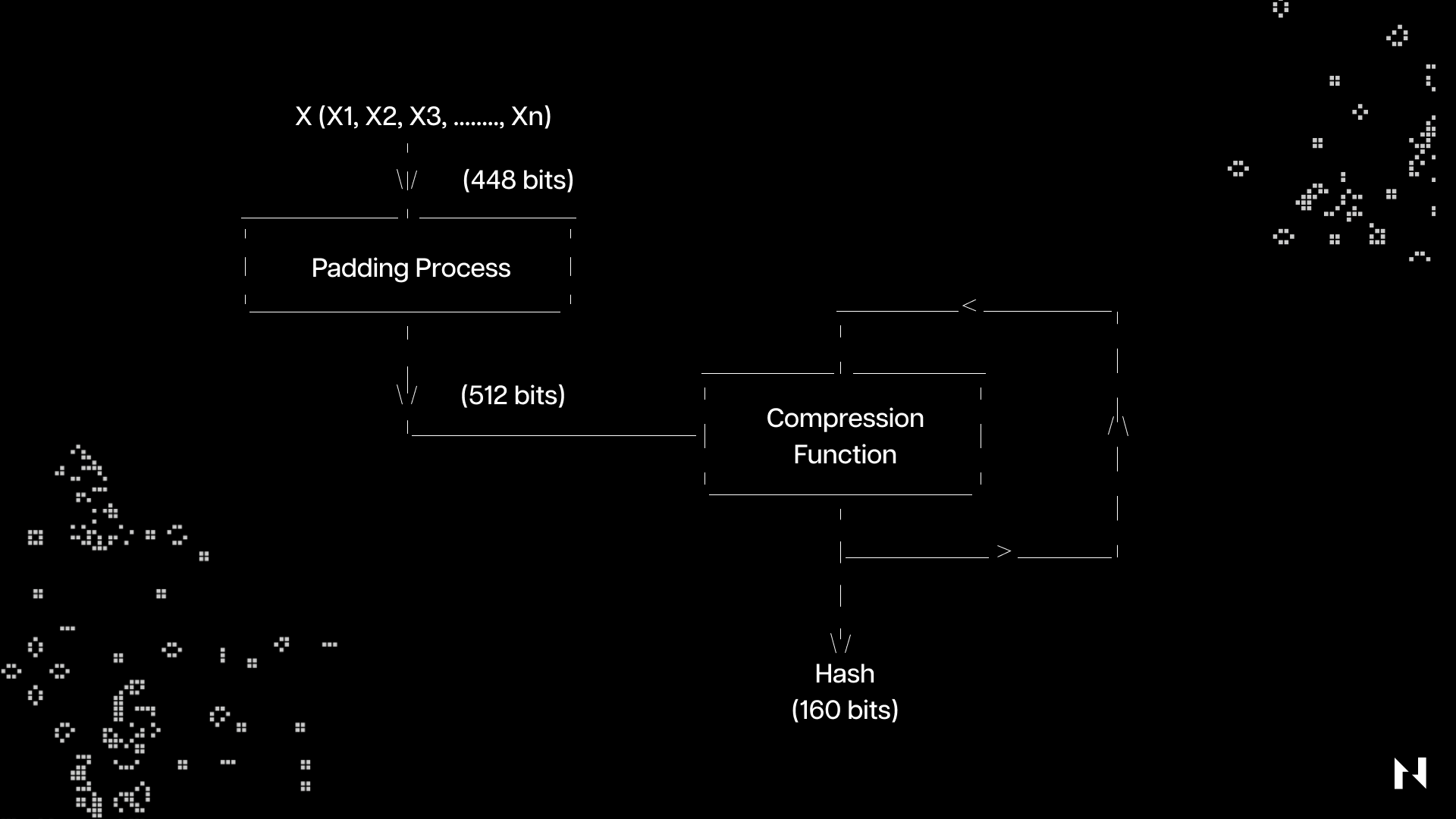
What Is A Hash Function Learn what a hash value is, how it works, and why it's essential for cybersecurity. from passwords to file integrity, hashing is your digital fingerprint. Learn what hashing in cryptography is, how it works, key algorithms like sha 256, real world uses, and best practices to keep your data secure. Discover what a hash function is, how it works, and why it's essential for protecting data, verifying integrity, and strengthening cybersecurity. Learn what hash means, how hashing works, and why it's essential for data integrity, cybersecurity, and encryption strategies.

What Is A Hash Function Discover what a hash function is, how it works, and why it's essential for protecting data, verifying integrity, and strengthening cybersecurity. Learn what hash means, how hashing works, and why it's essential for data integrity, cybersecurity, and encryption strategies.
Comments are closed.