What Is Zero Trust The Cybersecurity Model Explained
Zero Trust Security Model Explained Principles Architectu Blog Learn what zero trust is, how the security model works, its core pillars, the nist framework, and how to implement a zero trust architecture step by step. Unlike traditional security models that rely on a defined network perimeter, zero trust operates on the principle that no user or system should be automatically trusted. instead, continuous authentication, authorization, and validation of security configurations are required before access is granted to applications and data.
Zero Trust Security Model Explained Principles Architectu Blog What is zero trust? zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data. Zero trust differs from conventional security models that take users within the network as secured, instead adopting a strict policy of "never trust, always verify". no user, device, or app gets access without proving their legitimacy—no exceptions. Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources.
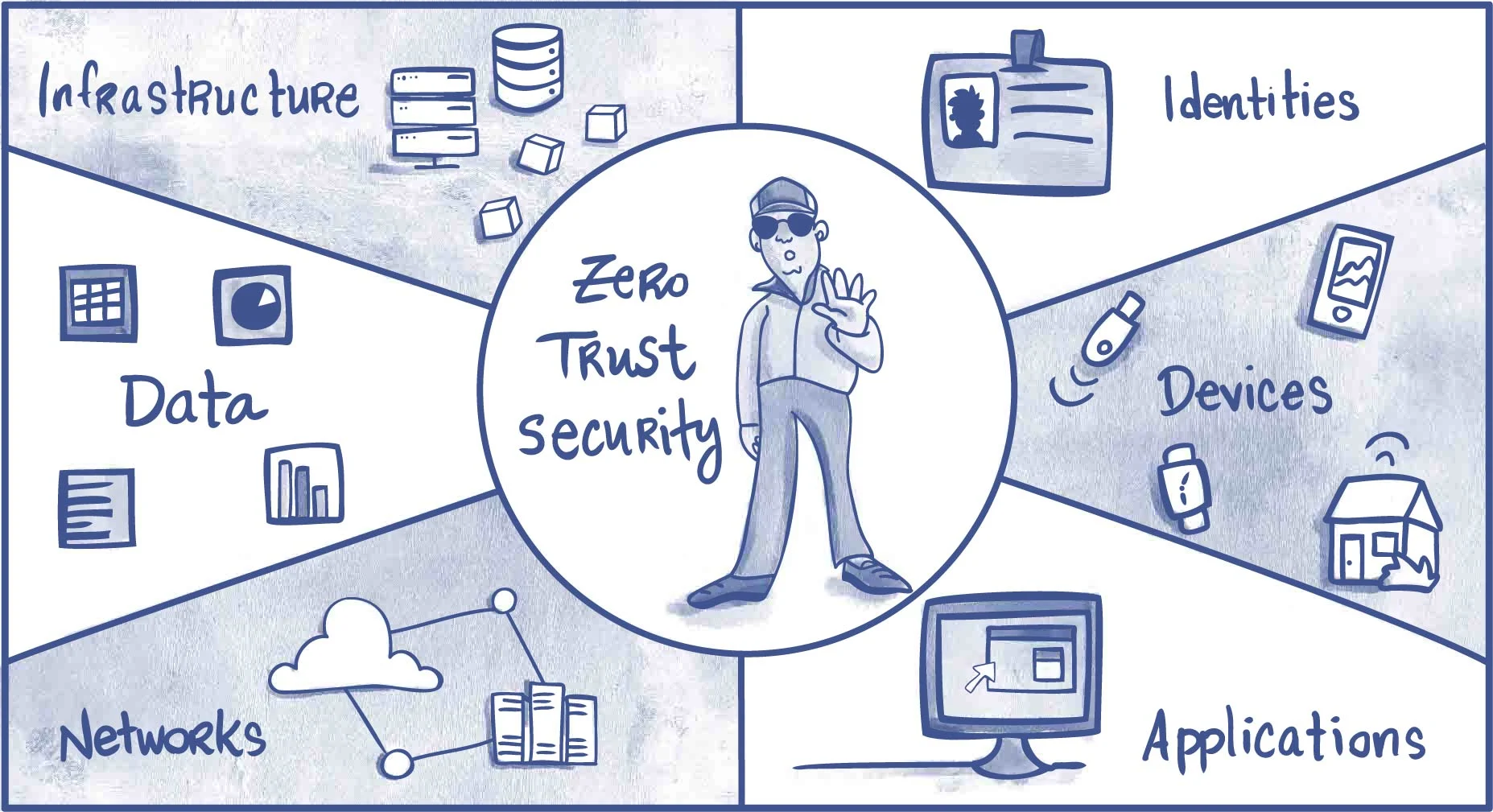
Zero Trust Explained How To Implement Zero Trust Architecture Reduce Zero trust is a security model based on “never trust, always verify.” learn how it enforces continuous authentication, least privilege access, and micro segmentation. Zero trust is a robust security model that works on the principle of “never trust, always verify” to ensure secure connections. understanding what is zero trust and implementing it can help organizations safeguard their crucial applications, devices, data, and resources. This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. Zero trust security: key principles explained learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence.

The Zero Trust Cybersecurity Model Explained This awareness level course introduces the basic tenets of the federal zero trust (zt) security concepts, provides a high level overview of federal zt strategy, and highlights how a properly executed zt approach can improve security. What it is: zero trust architecture (zta) is a cybersecurity framework built on the principle of “never trust, always verify.” it assumes every user, device, and application is untrusted until verified, enforcing strict identity, access, and policy controls. Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. Zero trust security: key principles explained learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence.
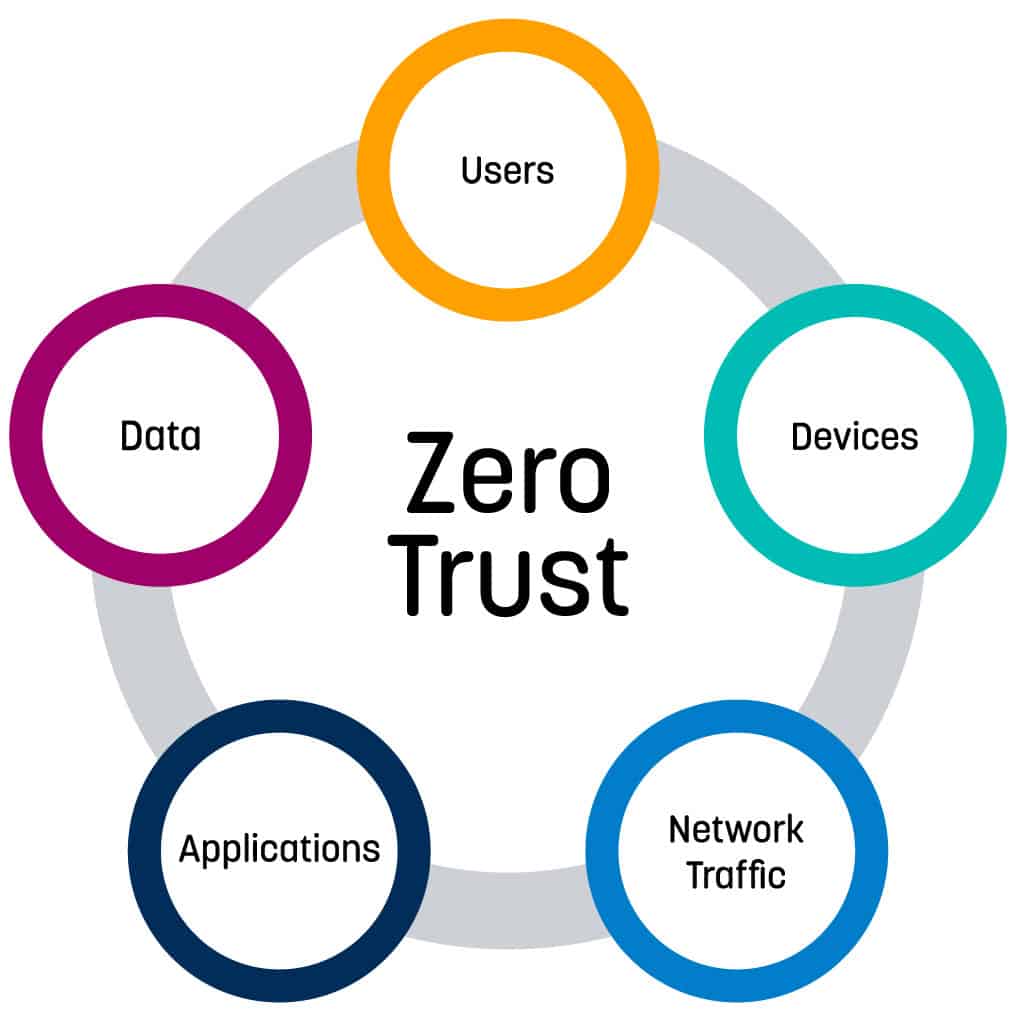
Embracing A Zero Trust Security Model Logrhythm Zero trust cybersecurity is a security model that eliminates implicit trust, requiring continuous verification for every access request. learn how zero trust strengthens defenses against cyber threats by enforcing strict authentication, least privilege access, and micro segmentation. Zero trust security: key principles explained learn how zero trust security reduces attack surface, enforces continuous verification, and integrates iam with attack surface intelligence.
Comments are closed.