What Is Zero Trust Security

Zero Trust Security Models Overview Pdf Zero trust is a security model based on maintaining strict access controls and not trusting anyone by default. learn more about zero trust. Learn how zero trust security works on the principle of strict identity verification and authorization for every access request, regardless of location. explore the history, evolution, and measures of zero trust network security, such as segmentation gateways, mfa, endpoint verification, and microsegmentation.

Zero Trust Security Model Derek S Blog Zero trust is a security strategy for modern multicloud networks. instead of focusing on the network perimeter, a zero trust security model enforces security policies for each individual connection between users, devices, applications and data. Zero trust security, also known as a zero trust architecture or perimeterless security, assumes no one and no device or application is universally trusted, whether inside or outside the network. Zero trust is a security framework that verifies the identity and security posture of every user and device before granting access to resources. learn how zero trust works, its key concepts, industry standards, and how it differs from traditional network security. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds.
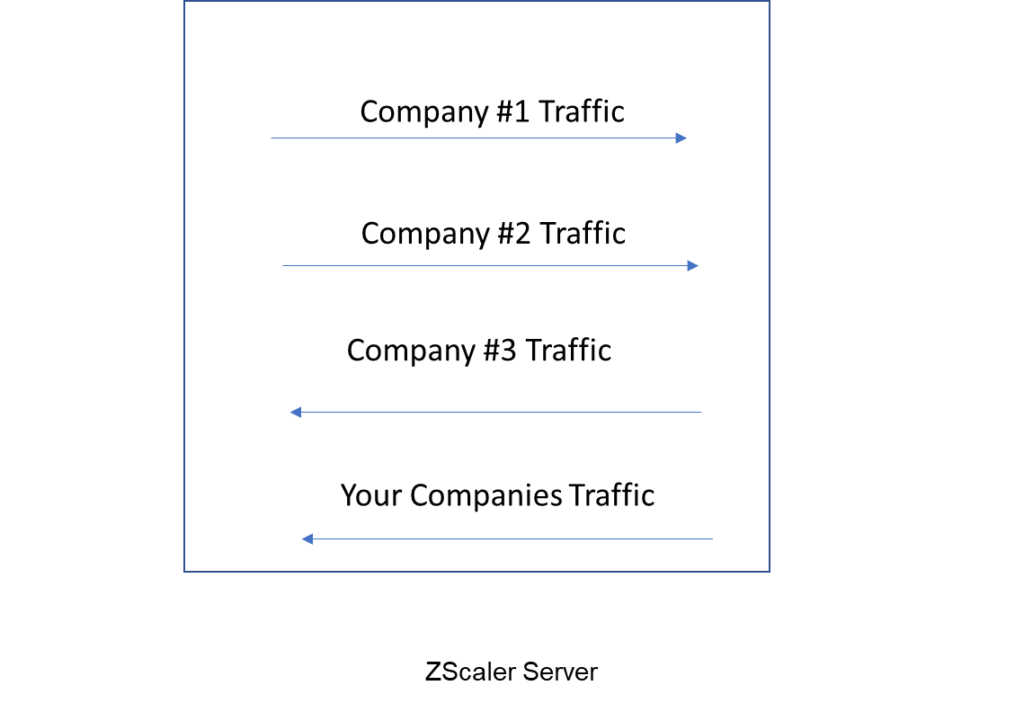
Zero Trust Security Model Derek S Blog Zero trust is a security framework that verifies the identity and security posture of every user and device before granting access to resources. learn how zero trust works, its key concepts, industry standards, and how it differs from traditional network security. What is zero trust? the zero trust security model uses identity and context information to continually verify trust before granting least privilege access for users, devices, apps, networks, and clouds. Zero trust is a cybersecurity strategy that removes implicit trust, treating all traffic as potentially risky – even if it’s already inside the network. rather than assuming internal traffic is trustworthy, zero trust assumes breach. Zero trust security is a strategic model that eliminates the concept of implicit trust in any user, device or network, whether internal or external. under this approach, every access request is thoroughly verified based on identity, device health and contextual risk before being granted. Zero trust architecture (zta) is a design and implementation strategy of it systems. the principle is that users and devices should not be trusted by default, even if they are connected to a privileged network such as a corporate lan and even if they were previously verified. the principle is also known as or perimeterless security or formerly de perimeterization. zta is implemented by. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. the goal is to prevent unauthorized access to data and services and make access control.

Principles Of Zero Trust Security Cwsi Zero trust is a cybersecurity strategy that removes implicit trust, treating all traffic as potentially risky – even if it’s already inside the network. rather than assuming internal traffic is trustworthy, zero trust assumes breach. Zero trust security is a strategic model that eliminates the concept of implicit trust in any user, device or network, whether internal or external. under this approach, every access request is thoroughly verified based on identity, device health and contextual risk before being granted. Zero trust architecture (zta) is a design and implementation strategy of it systems. the principle is that users and devices should not be trusted by default, even if they are connected to a privileged network such as a corporate lan and even if they were previously verified. the principle is also known as or perimeterless security or formerly de perimeterization. zta is implemented by. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. the goal is to prevent unauthorized access to data and services and make access control.
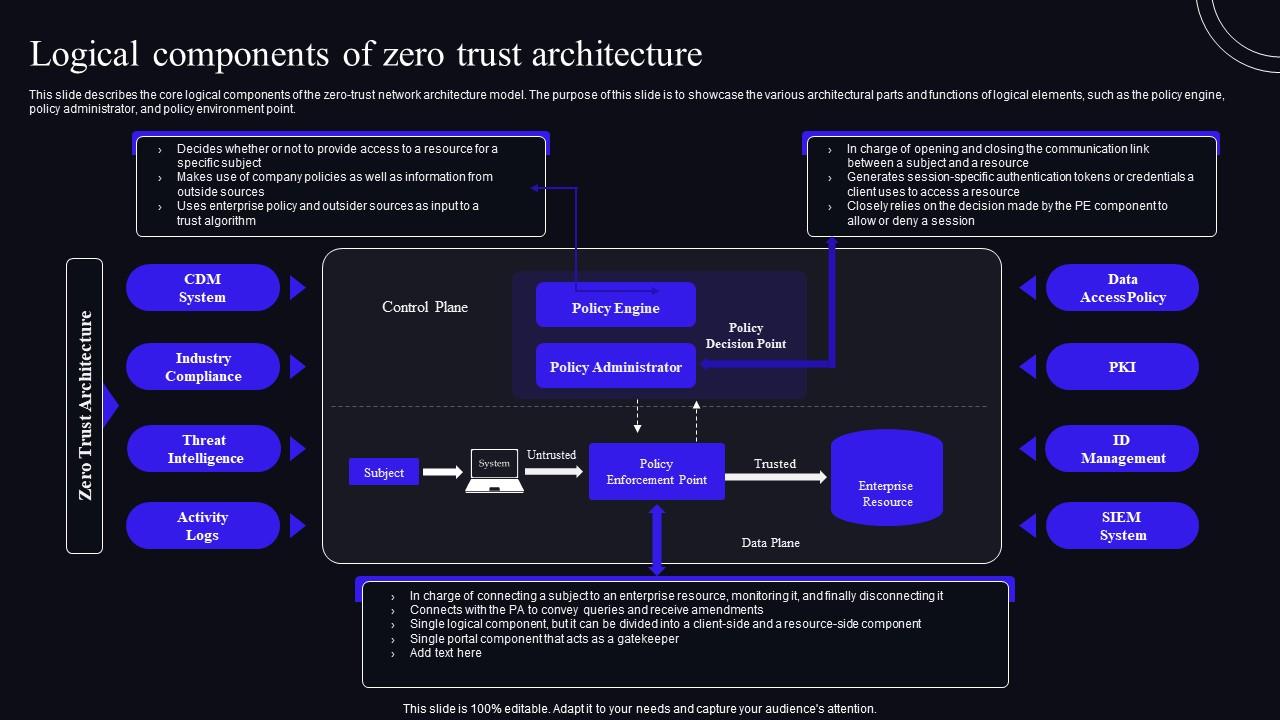
Logical Components Of Zero Trust Architecture Zero Trust Security Model Zero trust architecture (zta) is a design and implementation strategy of it systems. the principle is that users and devices should not be trusted by default, even if they are connected to a privileged network such as a corporate lan and even if they were previously verified. the principle is also known as or perimeterless security or formerly de perimeterization. zta is implemented by. What zero trust means for cybersecurity zt principles assume the entire network is compromised. that point of view provides a collection of concepts and ideas designed to minimize uncertainty by enforcing precise, least privilege per request access decisions within information systems and services. the goal is to prevent unauthorized access to data and services and make access control.

What Is Zero Trust Architecture Zero Trust Security Model
Comments are closed.