What Is Vulnerability Next Lvl Programming
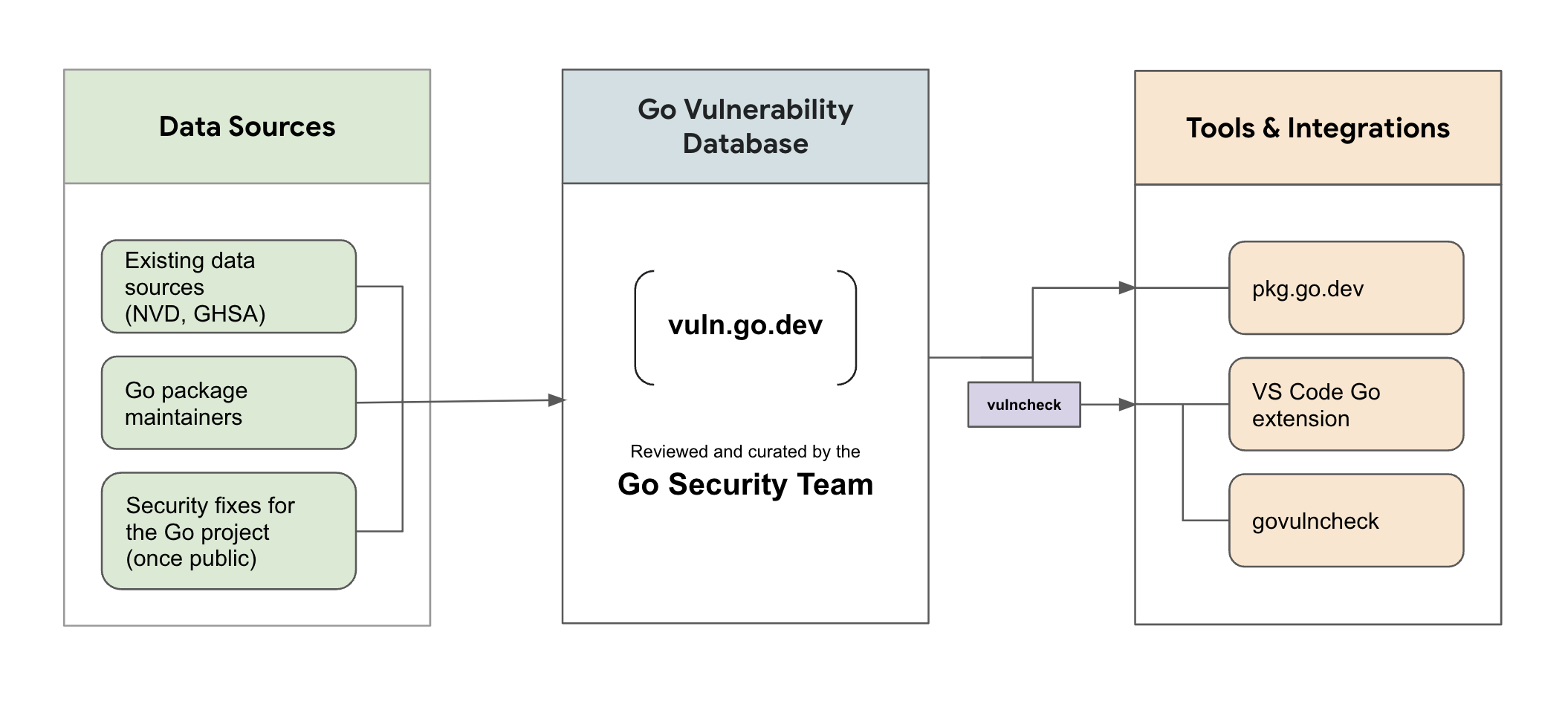
Vulnerability Management For Go The Go Programming Language Open In this informative video, we’ll dive into the concept of vulnerability within the realm of programming. understanding vulnerabilities is essential for anyone involved in software. Can't hold it back! the most powerful claude mythos 5.0 has suddenly started its internal test. its programming and reasoning abilities are incredibly strong, sending shivers down one's spine. an engineer with three week work experience self reports: they don't write a single line of code.
Vulnerability Concept With Random Parts Of Program Code Vulnerability Cve 2025 33248 nvidia megatron lm contains a vulnerability in the hybrid conversion script where an attacker may cause an rce by convincing a user to load a maliciously crafted file. This article aims to bridge that gap by systematically examining widely used programming languages, levels of program representation, categories of vulnerabilities, and mainstream detection techniques. What is a vulnerability? a vulnerability is a hole or a weakness in the application, which can be a design flaw or an implementation bug, that allows an attacker to cause harm to the stakeholders of an application. In computer security, vulnerabilities are flaws or weaknesses in a system's design, implementation, or management that can be exploited by a malicious actor to compromise its security.
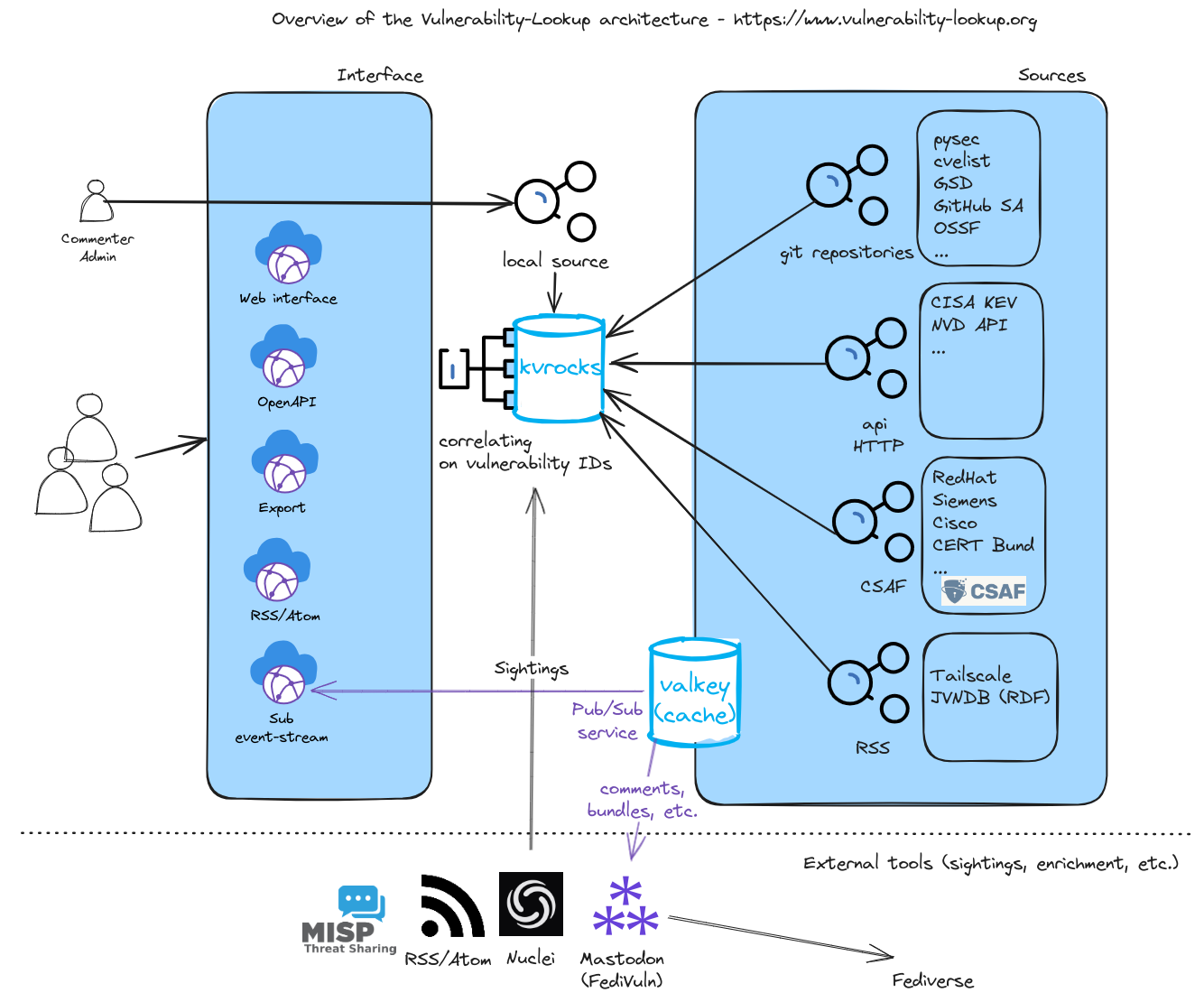
High Level Architecture Vulnerability Lookup What is a vulnerability? a vulnerability is a hole or a weakness in the application, which can be a design flaw or an implementation bug, that allows an attacker to cause harm to the stakeholders of an application. In computer security, vulnerabilities are flaws or weaknesses in a system's design, implementation, or management that can be exploited by a malicious actor to compromise its security. Learn what vulnerability management is and why it's important for organizations to effectively manage vulnerabilities as part of cybersecurity programs. A vulnerability is a weakness that can be exploited by cybercriminals to gain unauthorized access to a computer system. after exploiting a vulnerability, a cyberattack can run malicious code, install malware, and even steal sensitive data. Explore the latest news and expert commentary on vulnerabilities & threats, brought to you by the editors of dark reading. In this article, versprite’s vs labs research team highlights common security vulnerabilities found across different programming languages and explain what developers should to consider when choosing a language as the basis for their product.
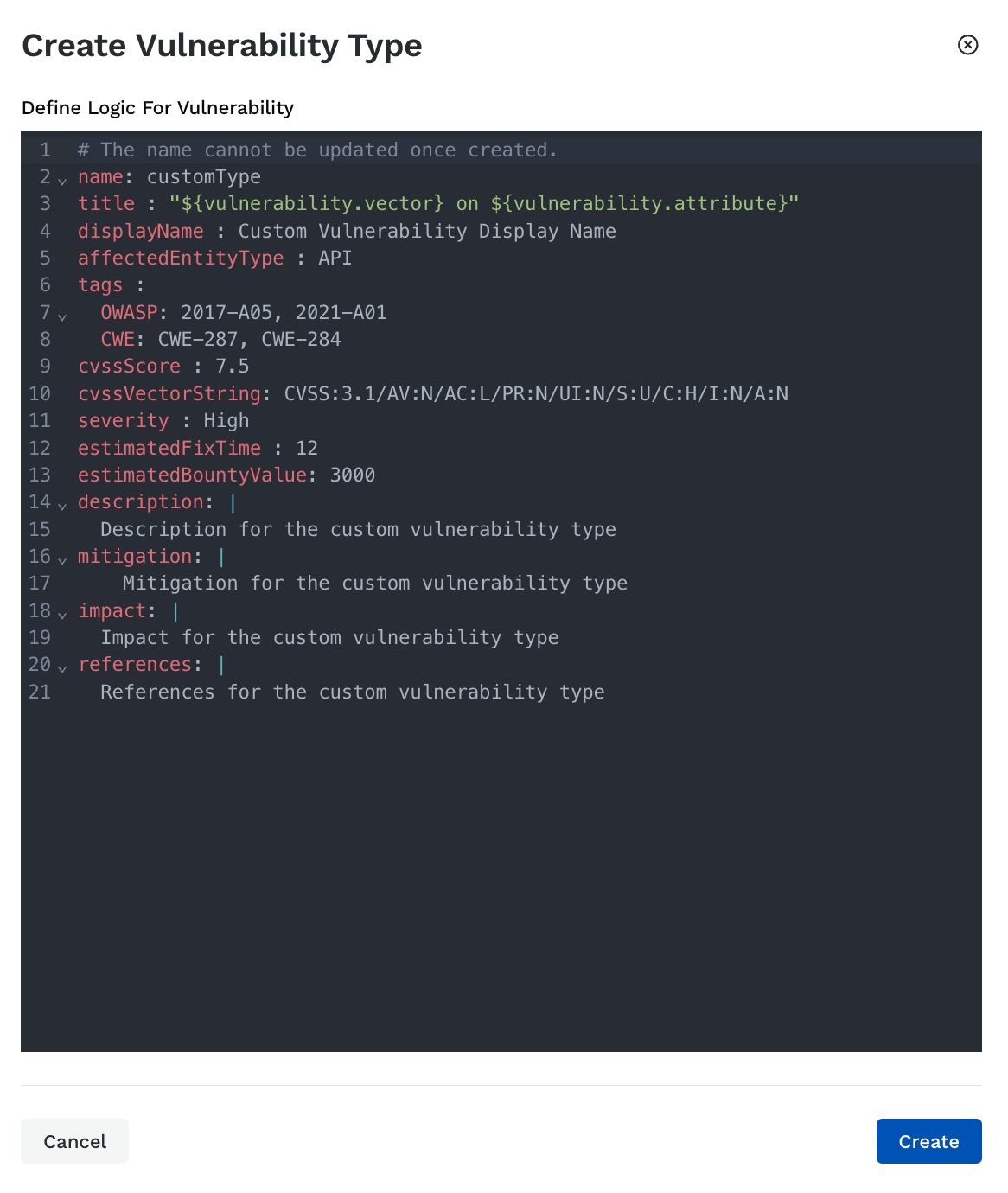
Vulnerability Types Learn what vulnerability management is and why it's important for organizations to effectively manage vulnerabilities as part of cybersecurity programs. A vulnerability is a weakness that can be exploited by cybercriminals to gain unauthorized access to a computer system. after exploiting a vulnerability, a cyberattack can run malicious code, install malware, and even steal sensitive data. Explore the latest news and expert commentary on vulnerabilities & threats, brought to you by the editors of dark reading. In this article, versprite’s vs labs research team highlights common security vulnerabilities found across different programming languages and explain what developers should to consider when choosing a language as the basis for their product.
Comments are closed.