What Is Twofish Algorithm Next Lvl Programming
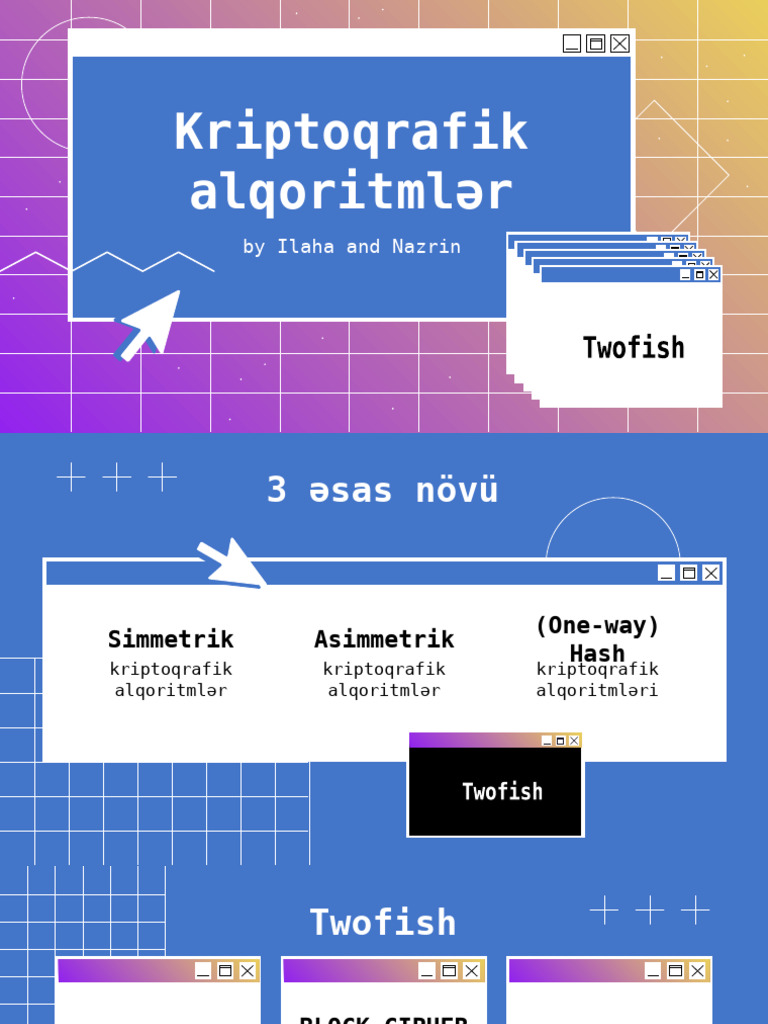
Twofish Algorithm Pdf Twofish is a symmetric key block cipher designed by bruce schneier and his team at counterpane systems. it is a block cipher variant, always operating compounding blocks of data, usually 128 bits. What is twofish algorithm? in this informative video, we will dive into the twofish algorithm, a notable encryption method that plays a significant role in securing data.

Twofish Pdf In cryptography, twofish is a symmetric key block cipher with a block size of 128 bits and key sizes up to 256 bits. it was one of the five finalists of the advanced encryption standard contest, but it was not selected for standardization. twofish is related to the earlier block cipher blowfish. The twofish encryption algorithm is an open source symmetric key block cipher developed for the 1997 national institute of standards and technology (nist) competition to determine the successor to the aging data encryption standard (des). Twofish is a symmetric encryption algorithm that uses a single key to encrypt and decrypt data and information. it accepts the key along with the plaintext information. this key then turns the information into ciphertext, which cannot be understood without decoding. In this guide, we’ll break down what the twofish encryption algorithm actually is, how it works without drowning you in math, where it’s used today, and what “secure” really means in 2026.
Github Java Hacker Twofish Algorithm Twofish Is A Symmetric Key Twofish is a symmetric encryption algorithm that uses a single key to encrypt and decrypt data and information. it accepts the key along with the plaintext information. this key then turns the information into ciphertext, which cannot be understood without decoding. In this guide, we’ll break down what the twofish encryption algorithm actually is, how it works without drowning you in math, where it’s used today, and what “secure” really means in 2026. Twofish is an advanced encryption standard (aes) blockcypher algorithm. twofish is not vulnerable to a simple brute force attack and is not inherently insecure against side channel attacks. let’s explore twofish here. in 1997, twofish was entered into a nist competition to replace the des algorithm. Twofish is ideal if you want to take security to the next level and encrypt highly confidential information. it's also desirable if you like to base your own encryption algorithm on an existing one or simply if you wish to use something less mainstream to encrypt your data. Twofish is one of the most secure encryption algorithms today. in this article, we examine how twofish works and how it compares to other ciphers like aes. One of the most secure encryption algorithms currently available is the twofish algorithm. in this article, we will explore everything you need to know about the twofish encryption algorithm.

Twofish Secure And Efficient Encryption Algorithm Twofish is an advanced encryption standard (aes) blockcypher algorithm. twofish is not vulnerable to a simple brute force attack and is not inherently insecure against side channel attacks. let’s explore twofish here. in 1997, twofish was entered into a nist competition to replace the des algorithm. Twofish is ideal if you want to take security to the next level and encrypt highly confidential information. it's also desirable if you like to base your own encryption algorithm on an existing one or simply if you wish to use something less mainstream to encrypt your data. Twofish is one of the most secure encryption algorithms today. in this article, we examine how twofish works and how it compares to other ciphers like aes. One of the most secure encryption algorithms currently available is the twofish algorithm. in this article, we will explore everything you need to know about the twofish encryption algorithm.

Twofish Algorithm And Working Of This Algorithm Abdul Wahab Junaid Twofish is one of the most secure encryption algorithms today. in this article, we examine how twofish works and how it compares to other ciphers like aes. One of the most secure encryption algorithms currently available is the twofish algorithm. in this article, we will explore everything you need to know about the twofish encryption algorithm.

Twofish Encryption Algorithm Pdf Cryptanalysis Cryptography
Comments are closed.