What Is The Secure Shell Ssh Protocol Ssh Academy
What Is The Secure Shell Ssh Protocol Ssh Academy The ssh protocol (also referred to as secure shell) is a method for secure remote login from one computer to another. it provides several alternative options for strong authentication, and it protects communications security and integrity with strong encryption. The secure shell (ssh) protocol sets up encrypted connections for remote logins and file transfers between computers. ssh also enables tunneling. learn how ssh works.

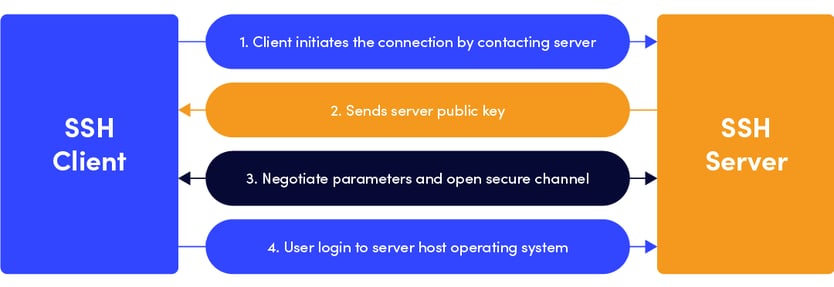
What Is The Secure Shell Ssh Protocol Ssh Academy The secure shell protocol (ssh protocol) is a cryptographic network protocol for operating network services securely over an unsecured network. [1] its most notable applications are remote login and command line execution. The ssh protocol uses encryption to secure the connection between a client and a server. all user authentication, commands, output, and file transfers are encrypted to protect against attacks in the network. Ssh (secure shell) is the standard way to remotely manage linux servers. it encrypts all traffic between your machine and the server — commands, file transfers, and even forwarded ports are all secured. this guide covers everything from basic connections to advanced tunneling and security. Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network.
What Is The Secure Shell Ssh Protocol Ssh Academy Ssh (secure shell) is the standard way to remotely manage linux servers. it encrypts all traffic between your machine and the server — commands, file transfers, and even forwarded ports are all secured. this guide covers everything from basic connections to advanced tunneling and security. Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. Ssh is a cryptographic protocol that enables secure communication over an unsecured network. it protects data confidentiality, integrity, and authenticity, making it indispensable for system administration, file transfer, and tunneling. The secure shell (ssh) protocol secures remote access, file transfers, tunneling and more. learn how it works and its common use cases. Every time you type ssh user@host, you trigger a cryptographic ceremony that involves at least 6 distinct protocol phases, 3 layers of encryption negotiation and a minimum of 8 tcp round trips i.e., before a single byte of your shell session is transmitted. let's tear it apart. Openssh is the premier connectivity tool for remote login with the ssh protocol. it encrypts all traffic to eliminate eavesdropping, connection hijacking, and other attacks. in addition, openssh provides a large suite of secure tunneling capabilities, several authentication methods, and sophisticated configuration options.
Comments are closed.