What Is Ssh
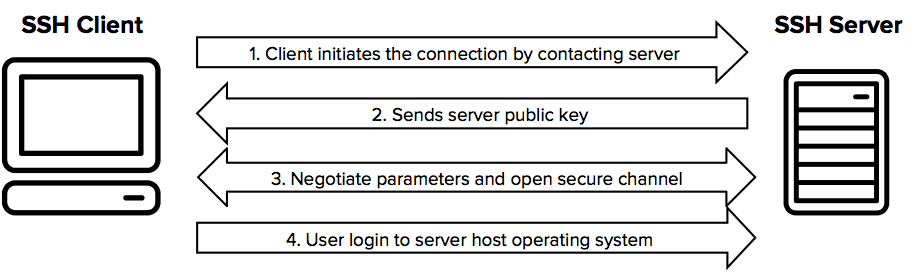
What Is Ssh Secure Shell Ssh Academy Ssh (secure shell) is a network protocol that establishes encrypted connections between computers for secure remote access. it operates on tcp port 22 and provides authentication, encryption, and integrity to protect data transmitted over unsecured networks. Ssh stands for secure shell, and it’s a protocol that allows you to connect to a remote computer securely over an unsecured network. ssh provides a secure channel between two computers, ensuring that data transferred between them is encrypted and protected from attackers.

What Is Secure Shell Ssh Tecadmin Ssh (secure shell or secure socket shell) is a network protocol that gives users particularly systems administrators a secure way to access a computer over an unsecured network. ssh also refers to the suite of utilities that implement the ssh protocol. Ssh, or secure shell protocol, is a remote administration protocol that allows users to access, control, and modify their remote servers over the internet. What is ssh? ssh is a secure means of logging into a remote machine. once logged in, you can run any command you need to work with the server. before you think that using ssh is difficult, fret. Then came secure shell (ssh) —a protocol that revolutionized how we communicate securely over the internet. since its creation in 1995, ssh has been a trusted companion for system administrators, developers, and cybersecurity experts worldwide.
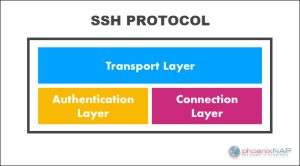
Ssh Vs Ssl What Are The Differences What is ssh? ssh is a secure means of logging into a remote machine. once logged in, you can run any command you need to work with the server. before you think that using ssh is difficult, fret. Then came secure shell (ssh) —a protocol that revolutionized how we communicate securely over the internet. since its creation in 1995, ssh has been a trusted companion for system administrators, developers, and cybersecurity experts worldwide. Learn what ssh is, how it works, and why it is essential for remote access and file transfers. this guide covers ssh history, cryptography, best practices, and use cases with examples. Ssh is a protocol for encrypted communication between remote machines over a network. learn what ssh is, how it works, and how to use it for file transfers, tunneling, and more. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric. Ssh, or secure shell, is used for various purposes, primarily focused on secure communication and management of remote systems. it provides encrypted command line access to remote machines,.
Ssh Protocol Quick Explanation All About Testing Learn what ssh is, how it works, and why it is essential for remote access and file transfers. this guide covers ssh history, cryptography, best practices, and use cases with examples. Ssh is a protocol for encrypted communication between remote machines over a network. learn what ssh is, how it works, and how to use it for file transfers, tunneling, and more. Secure shell, or ssh, is a cryptographic network protocol that operates on the principles of encryption, key exchange, and robust authentication to secure communications over insecure networks. the functionality of ssh largely hinges on two types of encryption: symmetric and asymmetric. Ssh, or secure shell, is used for various purposes, primarily focused on secure communication and management of remote systems. it provides encrypted command line access to remote machines,.
Comments are closed.