What Is Kubernetes Runtime Threat Detection
Runtime Threat Detection Kubescape This article explores what kubernetes runtime security actually entails, why it’s essential, and how your team can detect and respond to live threats before they spread, not after. To mitigate these runtime security threats, kubernetes environments require a comprehensive threat detection strategy that combines various techniques and approaches.

What Is Kubernetes Runtime Threat Detection Dynamic threat detection: runtime security focuses on monitoring container behavior during execution to detect and respond to threats that static analysis (image scanning, admission control) cannot catch. it answers the question: "what is this container actually doing right now?". In this section, we will go through the various threat factors that necessitate runtime security for kubernetes. the primary security threats faced by applications in their runtime can be divided into five broad categories. Falco is a cloud native runtime security tool that detects anomalous activity and threats in kubernetes. it monitors system calls, application behavior, and configuration changes to identify security violations and attacks. To help close that gap, this article explains why runtime security in kubernetes is so important and which tools are available for helping to secure kubernetes against runtime threats.
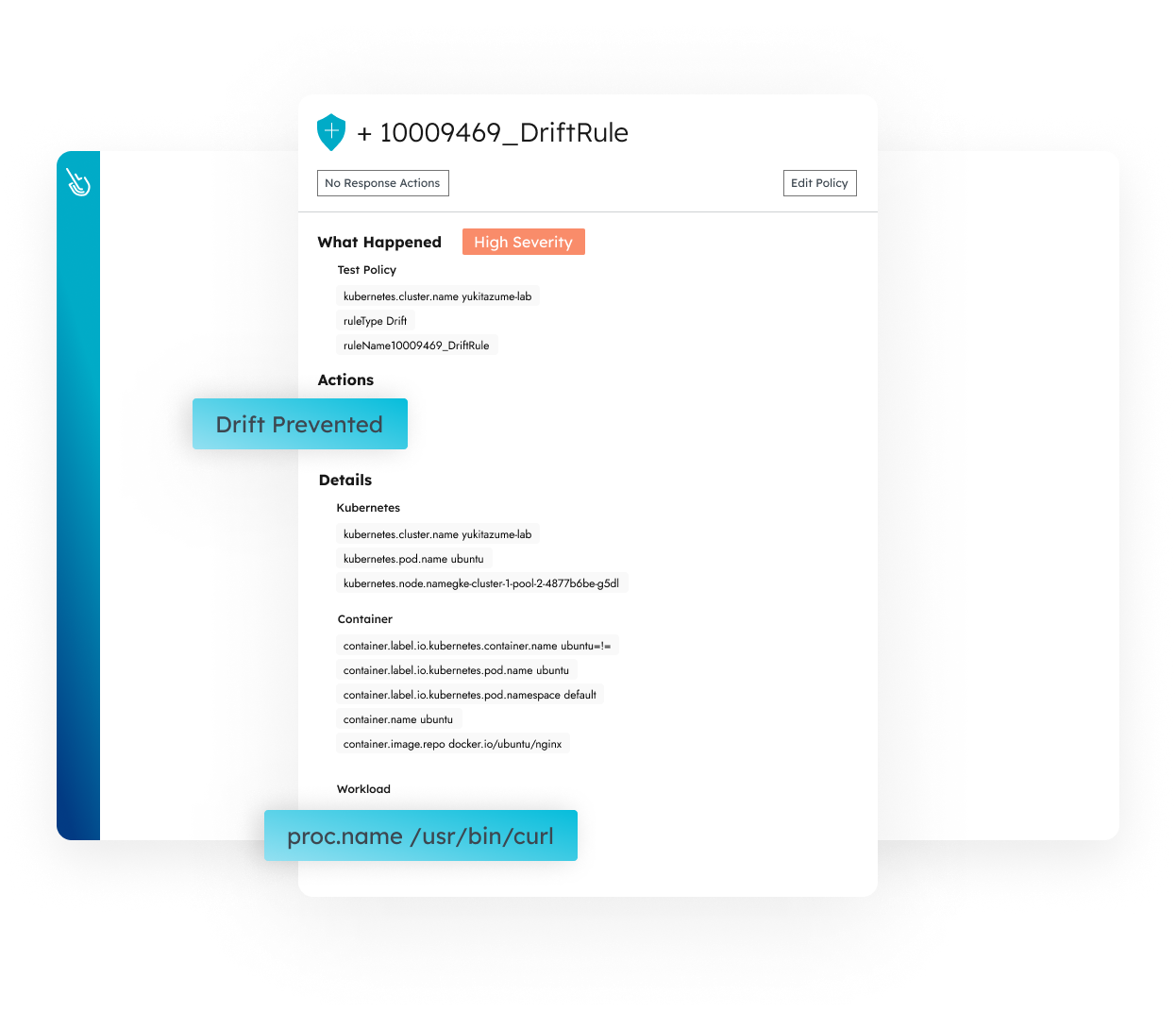
Server Threat Detection Tools Sysdig Falco is a cloud native runtime security tool that detects anomalous activity and threats in kubernetes. it monitors system calls, application behavior, and configuration changes to identify security violations and attacks. To help close that gap, this article explains why runtime security in kubernetes is so important and which tools are available for helping to secure kubernetes against runtime threats. Runtime security is the only way of detecting risks that impact live, running applications. indeed, runtime security is all the more important in kubernetes because kubernetes itself includes no built in controls for detecting and blocking threats. Discover how kubernetes runtime security detects and prevents post deployment threats like privilege escalation, lateral movement, and zero day exploits. Runtime threat detection fills this gap by observing what is actually happening in production, not just what might happen based on code analysis. as organizations run more workloads in containers and kubernetes, runtime has become the primary attack surface. Identifying the baseline for how your application or container functions can help detect threats and vulnerabilities at runtime. you can set up your baselines by tracking configurations, resource utilization, network traffic, or process execution.
.png)
Hardening Kubernetes Security With Falco Runtime Threat Detection Runtime security is the only way of detecting risks that impact live, running applications. indeed, runtime security is all the more important in kubernetes because kubernetes itself includes no built in controls for detecting and blocking threats. Discover how kubernetes runtime security detects and prevents post deployment threats like privilege escalation, lateral movement, and zero day exploits. Runtime threat detection fills this gap by observing what is actually happening in production, not just what might happen based on code analysis. as organizations run more workloads in containers and kubernetes, runtime has become the primary attack surface. Identifying the baseline for how your application or container functions can help detect threats and vulnerabilities at runtime. you can set up your baselines by tracking configurations, resource utilization, network traffic, or process execution.

Kubernetes Threat And Attack Detection Video Course Scanlibs Runtime threat detection fills this gap by observing what is actually happening in production, not just what might happen based on code analysis. as organizations run more workloads in containers and kubernetes, runtime has become the primary attack surface. Identifying the baseline for how your application or container functions can help detect threats and vulnerabilities at runtime. you can set up your baselines by tracking configurations, resource utilization, network traffic, or process execution.
Comments are closed.