What Is Data Encryption Encryption Algorithms

Top 8 Strongest Data Encryption Algorithms In Cryptography By using encryption keys and mathematical algorithms, the data is scrambled so that anyone intercepting it without the proper key cannot understand the contents. when the intended recipient receives the encrypted data, they use the matching decryption key to return it to its original, readable form. Learn what is data encryption in depth by understanding its types, algorithms, methods & techniques. read on to know why we need data encryption and how does it work.
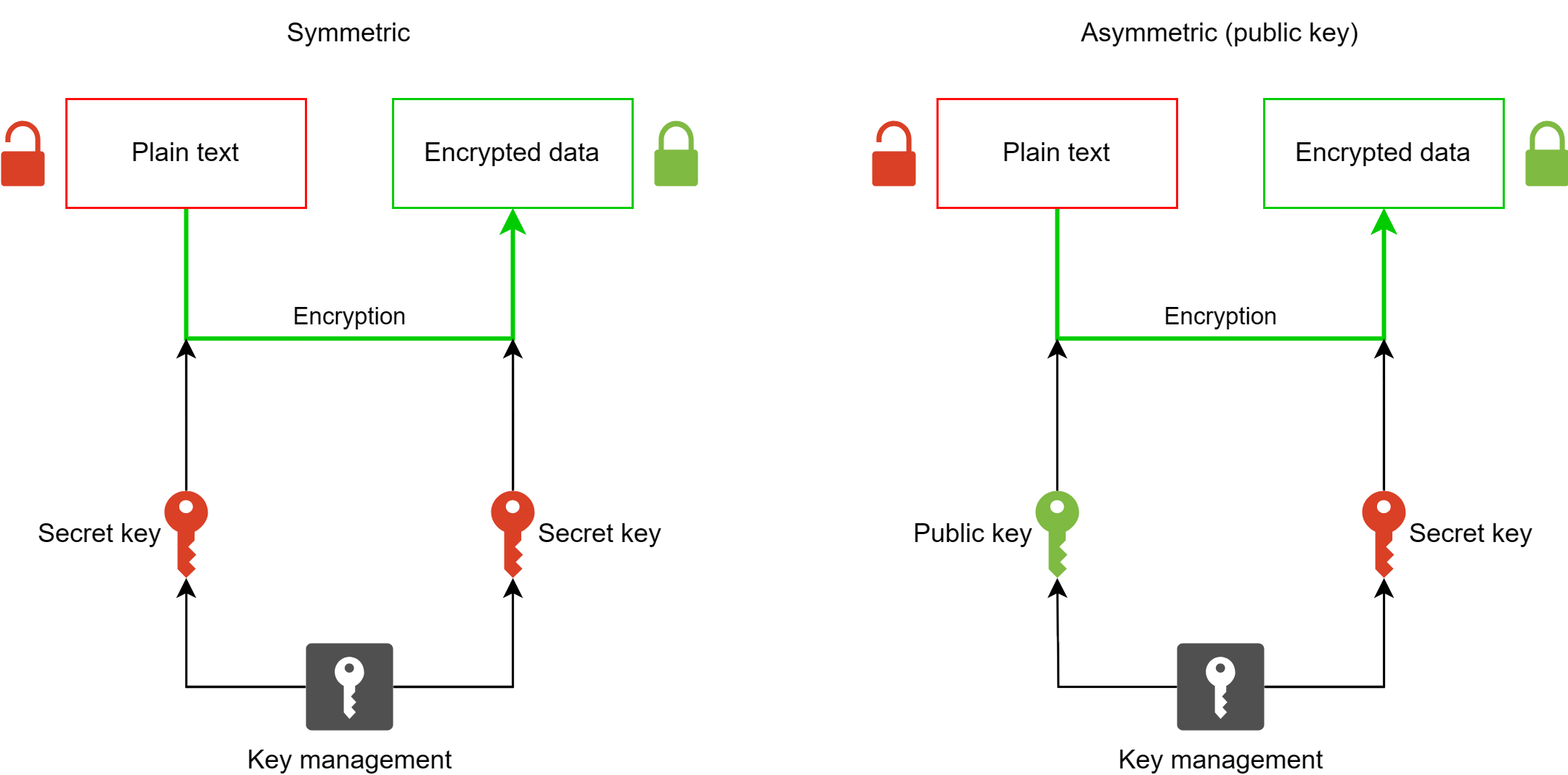
Encryption Algorithms Encryption algorithms are mathematical functions used to convert plain text into ciphertext to keep data secure. common encryption algorithms include aes, des, 3des, rsa, diffie hellman, elliptic curve cryptography, bcrypt, scrypt, and more. What is data encryption? learn how encryption works, explore key types of encryption, and see how cloud and database encryption protect sensitive data. Encryption uses a formula called a “cipher” or an encryption algorithm, which ensures that anyone who tries to intercept information communicated across a digital space cannot read its true contents. Data encryption scrambles a piece of data, making it unreadable to any person, service, or device without the key to unlock its content. encryption makes files, disks, objects, streams, and other types of data private between an encryptor and a key holder.
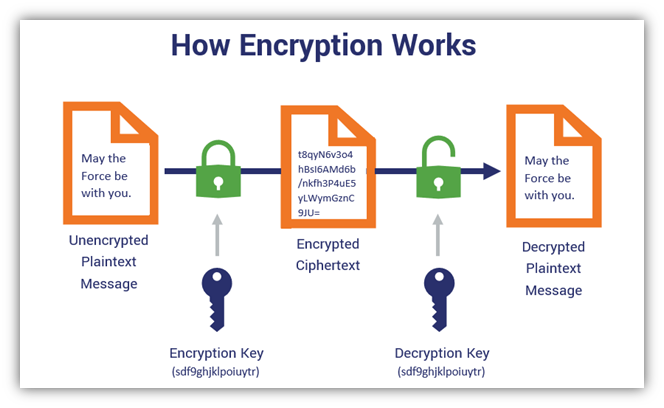
Top 8 Strongest Data Encryption Algorithms In Cryptography Encryption uses a formula called a “cipher” or an encryption algorithm, which ensures that anyone who tries to intercept information communicated across a digital space cannot read its true contents. Data encryption scrambles a piece of data, making it unreadable to any person, service, or device without the key to unlock its content. encryption makes files, disks, objects, streams, and other types of data private between an encryptor and a key holder. Data encryption is a method of converting data from a readable format (plaintext) into an unreadable, encoded format (ciphertext). encrypted data can only be read or processed after it has been decrypted, using a decryption key or password. Data encryption acts like a digital lock and key system. when you encrypt data, you're essentially scrambling it using complex mathematical formulas called algorithms. think of it like translating a message into a secret code—without the "decoder ring" (encryption key), the message looks like random gibberish. In this guide, we’ll break down 11 types of data encryption, explain how each algorithm works, compare their pros, and cons, and show how extending encryption with in line data protection helps maintain compliance, governance, and visibility everywhere your data flows. Data encryption is a fundamental building block of cybersecurity, ensuring that data cannot be read, stolen, or altered either at rest or in transit. as more data moves online, data encryption plays an increasingly crucial role in cybersecurity.

7 Data Encryption Algorithms For 2023 Data encryption is a method of converting data from a readable format (plaintext) into an unreadable, encoded format (ciphertext). encrypted data can only be read or processed after it has been decrypted, using a decryption key or password. Data encryption acts like a digital lock and key system. when you encrypt data, you're essentially scrambling it using complex mathematical formulas called algorithms. think of it like translating a message into a secret code—without the "decoder ring" (encryption key), the message looks like random gibberish. In this guide, we’ll break down 11 types of data encryption, explain how each algorithm works, compare their pros, and cons, and show how extending encryption with in line data protection helps maintain compliance, governance, and visibility everywhere your data flows. Data encryption is a fundamental building block of cybersecurity, ensuring that data cannot be read, stolen, or altered either at rest or in transit. as more data moves online, data encryption plays an increasingly crucial role in cybersecurity.

Strongest Data Encryption Algorithms рџ ќ In this guide, we’ll break down 11 types of data encryption, explain how each algorithm works, compare their pros, and cons, and show how extending encryption with in line data protection helps maintain compliance, governance, and visibility everywhere your data flows. Data encryption is a fundamental building block of cybersecurity, ensuring that data cannot be read, stolen, or altered either at rest or in transit. as more data moves online, data encryption plays an increasingly crucial role in cybersecurity.
Top 8 Strongest Data Encryption Algorithms In Cryptography
Comments are closed.