What Is Credential Phishing Attack Indusface Blog

Credential Dumping Phishing Windows Credentials 1701434265 Pdf Credential phishing is where hackers attempt to steal your credentials by pretending to be a trusted party in an email or other communication channel. hackers will often sell the data they’ve collected to the dark web. Credential phishing is a specific kind of phishing cyberattack that is aimed at getting users to share their credentials (typically usernames and passwords) so that the attacker can steal and use them to gain unauthorized access to email accounts, business systems, and other secure resources.
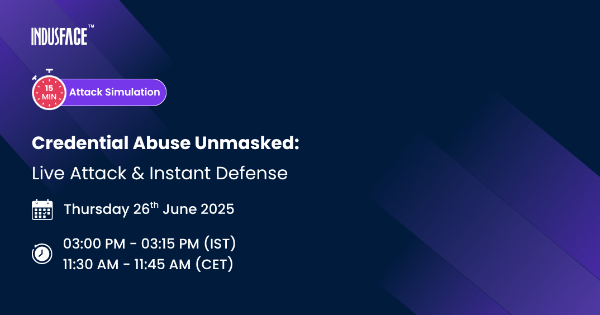
Credential Abuse Unmasked Live Attack Instant Defense Organizations that implement strong execution controls, phishing resistant authentication, and credential isolation architectures dramatically reduce the probability that an endpoint infection can. Credential phishing is a social engineering attack that targets users’ login credentials. learn how a strong cyber defense and login protocols can help prevent it. A credential based attack is a tactic in which adversaries use stolen, phished, reused, or programmatically guessed credentials to gain unauthorized access to systems, applications, or data. Credential phishing is an advanced cyber threat in which hackers steal users' credentials. in this article, we'll delve into what credential phishing is, how the attack is done, and how it can be prevented.

Credential Phishing Prevention 10 Steps To Get Started A credential based attack is a tactic in which adversaries use stolen, phished, reused, or programmatically guessed credentials to gain unauthorized access to systems, applications, or data. Credential phishing is an advanced cyber threat in which hackers steal users' credentials. in this article, we'll delve into what credential phishing is, how the attack is done, and how it can be prevented. Learn what credentials phishing is, how attackers steal passwords, and how to prevent credential based attacks with phishing resistant authentication. In a scheme called credential phishing, online scammers seek to steal the keys to your online accounts: your login and password combinations. just like you’d protect the keys to your house, so should you guard your online account credentials closely. In this article, you’ll learn exactly how credential phishing works, see real world examples of its impact, and walk away with practical steps to protect yourself and your organization. Learn what credential harvesting is, how to detect phishing attacks, and protect your organization from credential theft. breaching an organization's defenses typically begins with gaining initial access. and one of the most effective ways hackers achieve this is by stealing credentials.
Comments are closed.