What Is Credential Phishing And How To Stop It

Credential Dumping Phishing Windows Credentials 1701434265 Pdf Credential phishing is a social engineering attack that targets users’ login credentials. learn how a strong cyber defense and login protocols can help prevent it. Discover what credential phishing is, how it works, and which tactics attackers use. learn how to prevent phishing with passkeys, mfa, and advanced cybersecurity solutions from rsa.

Stop Credential Phishing Attacks Abnormal Ai Learn what credentials phishing is, how attackers steal passwords, and how to prevent credential based attacks with phishing resistant authentication. Credential phishing is an advanced cyber threat in which hackers steal users' credentials. in this article, we'll delve into what credential phishing is, how the attack is done, and how it can be prevented. Credential phishing is the act of obtaining user id email address and password combinations through deceptive means, often by posing as a trusted entity. attackers then use these stolen credentials to gain unauthorized access and carry out follow on attacks on other systems or accounts. Credential phishing is the theft of usernames and passwords through deception. learn how it works, see real examples, and protect your organization.
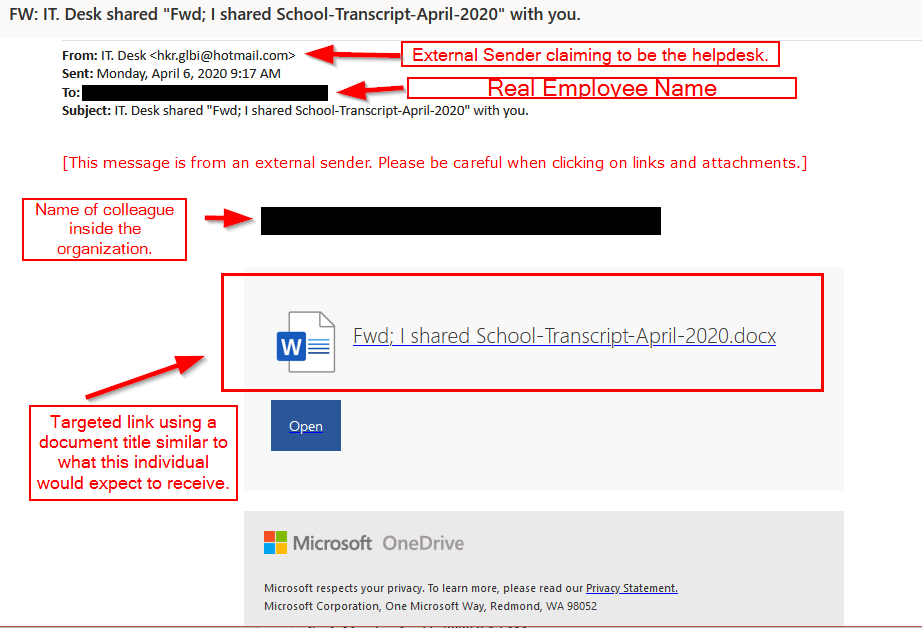
More Credential Phishing That Infosec Guy Credential phishing is the act of obtaining user id email address and password combinations through deceptive means, often by posing as a trusted entity. attackers then use these stolen credentials to gain unauthorized access and carry out follow on attacks on other systems or accounts. Credential phishing is the theft of usernames and passwords through deception. learn how it works, see real examples, and protect your organization. Learn what credential phishing is, how it works, and how the most effective defenses take a multi pronged approach of reinforcing behavior with security architecture. In a scheme called credential phishing, online scammers seek to steal the keys to your online accounts: your login and password combinations. just like you’d protect the keys to your house, so should you guard your online account credentials closely. Learn what credential harvesting is, how to detect phishing attacks, and protect your organization from credential theft. Discover methods of credential theft in cybersecurity, the impact of stolen credentials, and 5 actionable steps to protect against breaches now.
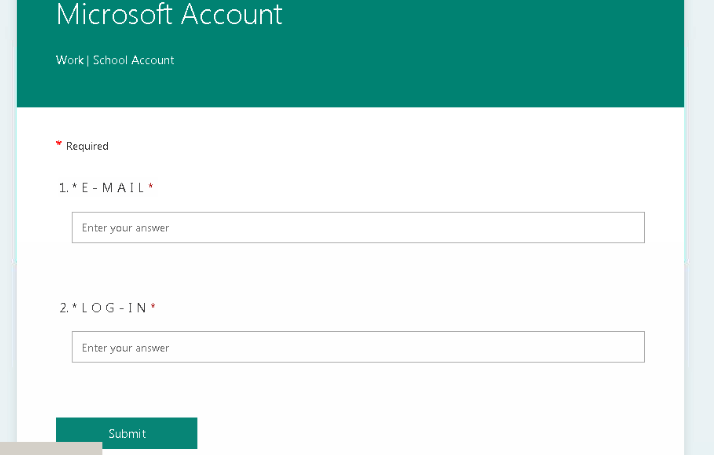
More Credential Phishing That Infosec Guy Learn what credential phishing is, how it works, and how the most effective defenses take a multi pronged approach of reinforcing behavior with security architecture. In a scheme called credential phishing, online scammers seek to steal the keys to your online accounts: your login and password combinations. just like you’d protect the keys to your house, so should you guard your online account credentials closely. Learn what credential harvesting is, how to detect phishing attacks, and protect your organization from credential theft. Discover methods of credential theft in cybersecurity, the impact of stolen credentials, and 5 actionable steps to protect against breaches now.
Comments are closed.